Table of contents
- What is Predator spyware?
- How does Predator spyware work?
- What kind of data can Predator access?
- How Predator spyware infects devices
- Who is typically targeted by Predator spyware?
- Where Predator spyware has been reported
- Legal and ethical concerns around Predator spyware
- How to protect your device from Predator spyware
- 1. Keeping software and systems up to date
- 2. Being cautious with links and messages
- 3. Using built-in device security features
- 4. Using additional security tools when appropriate
- Conclusion
What is Predator spyware?
Predator is a type of spyware that first came to light in the early 2020s. Sharing many similarities with Pegasus, Predator is incredibly sophisticated, providing access to call logs, text messages, files and documents, and other valuable data a device contains. It also listens into calls and allows real-time surveillance through a device’s camera and microphones.
Available from the Intellexa consortium, which includes North Macedonian malware developer Cytrox, Predator spyware can also add a certificate authority (CA) to your device, which tricks it into trusting other malicious software. The spyware is reportedly sold to governments around the world to monitor criminals, foreign agents, and in some cases, critics and political opponents.
How does Predator spyware work?
Predator takes advantage of zero-day exploits found in Android and iOS to circumvent the security protections built into Google and Apple's platforms. Once set up, the spyware hides itself and runs in the background, and uses automation features within iOS to ensure it persists after a device reboot.
Predator software constantly gathers information and feeds it back to authorities, and it takes control of device hardware to monitor a target’s communications, location, and more. As a result, it places a persistent load on device resources, typically leading to battery drain and overheating.
What kind of data can Predator access?
Predator is even more powerful than common spyware and stalkerware apps, which means it can access almost all data that a device contains, including:
- Calls and phone logs
- Text messages
- Social media data
- Photos, videos, and screenshots
- Browser activity
- Account login credentials
- Notes and voice memos
- Files and documents
- Crypto accounts
- Saved passwords and credit card details.
How Predator spyware infects devices
Predator software typically installs on a target device via a “one-click” link sent by text message, email, or instant messaging platforms like WhatsApp. Hackers trick their victims into clicking a malicious link that injects Predator onto their devices without any further action. Predator can also infect devices via malicious online ads and “zero-click” exploits that require no user interaction at all.
Who is typically targeted by Predator spyware?
You’ll be pleased to know that most of us aren’t targets for Predator. Leaked documents detailing the spyware indicate it costs millions of dollars per install, so its use is reserved for surveilling high-value individuals. This can include major corporate executives and people who are considered potential threats by government agencies, such as opposition politicians, journalists, activists, and international officials.
Where Predator spyware has been reported
Since its initial detection in around 2022, Predator software has been reported in various countries across Africa, Asia, Europe, and the Middle East. One of the most high-profile uses of Predator, according to Amnesty International, is “Greece’s Watergate,” which saw more than 80 politicians, journalists, and military officials targeted in 2022-2023, and resulted in the conviction of four people.
Legal and ethical concerns around Predator spyware
Many consider Predator spyware a threat to fundamental rights to privacy and freedom of expression, with human rights activists calling it a tool of repression. In many cases, investigations have shown that the software is employed outside of legal frameworks and without warrants, like in “Greece’s Watergate” scandal, and it seems to be more widely used in countries with poor human rights records.
Organizations like the EDRi (European Digital Rights) are calling for a full ban on the production and sale of software like Predator throughout the EU, while in other countries, citizens are pressuring governments to be more transparent about how they use surveillance technology since Predator was first revealed.
How to protect your device from Predator spyware
While it’s incredibly difficult to detect spyware like Predator due to its sophisticated nature and efforts to conceal itself, general cybersecurity precautions can help reduce the risk of infection from such threats. We recommend following these best practices:
- Keeping software and systems up to date
- Being cautious with links and messages
- Using built-in device security features
- Using additional security tools when appropriate
1. Keeping software and systems up to date
Software updates usually contain bug fixes and security patches that eliminate potential vulnerabilities and make operating systems more difficult to hack. We always advise installing these as soon as you can, as running out-of-date software increases the risk that a hacker can exploit known flaws to infect your device.
2. Being cautious with links and messages
Spyware and malicious software like Predator is commonly distributed via malicious links that are sent in text messages, emails, and through other communication channels. Be cautious before clicking any links you weren’t expecting or don’t trust, even if they are sent by someone you know.
3. Using built-in device security features
Modern operating systems, including Android and iOS, have a bunch of advanced security features built in to stop spyware and other dangerous threats. And the great news is, these are all enabled by default and constantly working in the background to keep you safe. All you have to do is make sure you don’t disable or circumvent any of them to install unauthorized software.
Outside of the EU, iOS in particular doesn’t allow users to install apps from third-party sources unless their iPhone is jailbroken. This makes it nearly impossible for hackers to install common spyware infections (those that target the average iPhone user).
4. Using additional security tools when appropriate
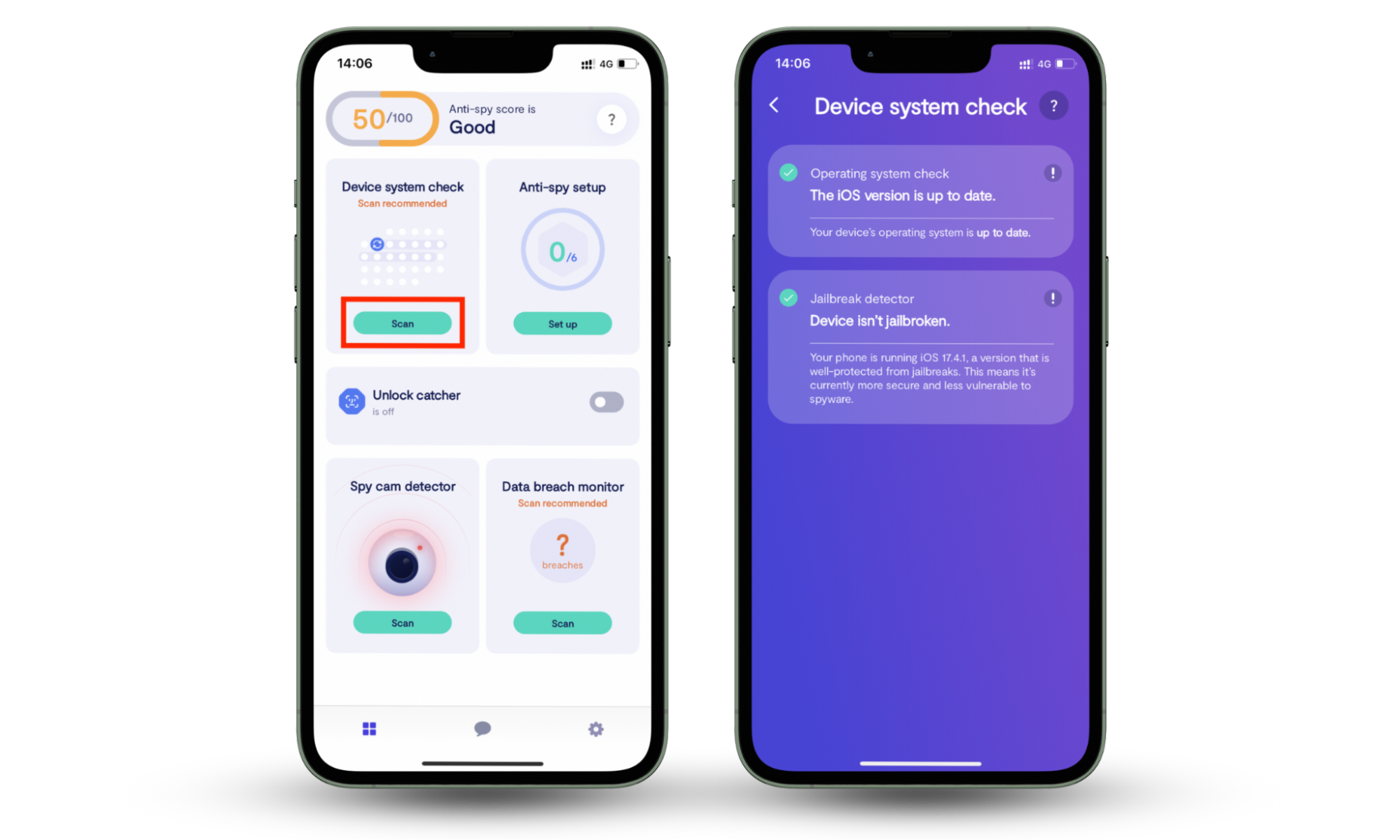
Although your iPhone has excellent security features built in, it’s a great idea to bolster your protection with additional tools to stop software like Predator. We highly recommend using Clario Anti Spy’s Device system check and Hidden App Scan to help keep your phone and your data safe.
Device system check is a helpful tool that tells you if iOS is up to date and whether your iPhone is jailbroken in just a few seconds. If you’re running an out-of-date version of iOS, it may contain security flaws that hackers can exploit to install spyware, while an active jailbreak indicates that unauthorized software is present. Try this:
- Install Clario Anti Spy on your iPhone.
- Under Device system check, tap Scan.
- Check to see the results. If your iPhone is running an older version of iOS, update it. If a jailbreak is detected, reset your iPhone to factory settings to remove it.
Clario Anti Spy’s Hidden App Scan helps you find potentially dangerous software that’s hiding or using suspicious app permissions. Here’s how to use it:
- After installing Clario Anti Spy, tap the Scan button under Hidden App Scan.
- See if any apps are hiding or using suspicious permissions, and delete any you don’t use or recognize.

Conclusion
Predator is widely regarded as one of the most advanced spyware tools in the market, but it’s incredibly expensive, which means that it’s mainly employed by state actors to monitor high-value targets. However, there are plenty of common spyware infections out there that infect the average smartphone user.
To avoid these threats, practice good cybersecurity, leverage the security features built into your device, and use third-party tools to enhance your protection. We recommend using Clario Anti Spy’s Device system check and Hidden App Scan to ensure your iPhone is up to date, not jailbroken, and free of potentially dangerous apps hiding in the background.


