Table of contents
- Data Exposure discovered at EventBuilder
- Company Profile
- Data Exposure Summary
- How this exposure likely occurred
- Information Included in the Data Leak
- Expert Advice
Data Exposure discovered at EventBuilder
Editor note
Clario Tech researchers identified publicly accessible files linked to EventBuilder’s webinar operations. The exposed data appeared to include large CSV/JSON files containing event registrant details (such as names, emails, phone numbers, and other form responses). Because the storage was indexable, the information could be discovered and misused for targeted phishing and other social engineering.
The data exposure, discovered using the Grayhat Warfare search engine, involved the exposure of potentially hundreds of thousands of files containing sensitive information relating to events registrants. The investigation was led by the team at the Clario Tech research center and highlighted how thousands of large-sized CSV/JSON files with Microsoft events registrants' details and summaries had been exposed to potential hackers worldwide. This put EventBuilder in the unenviable position of being part of an elite but particularly vulnerable club.
Definition
A data exposure typically means information was publicly accessible due to misconfiguration (for example, cloud storage set to allow anonymous access). This differs from a data breach, which usually involves unauthorized access (such as stolen credentials or exploitation). Exposures can still lead to serious harm if indexed and collected at scale.
Company Profile
EventBuilder provides a suite of webinar tools and professional services that are intended to work seamlessly with Microsoft Teams, Teams Live Events, and Skype for Business. The idea is to extend their functionality by providing registration pages, security, cloud recording, and reporting, to mention just a few of the available services. In a nutshell, they cover event logistics so the client can focus on the content. The data was stored on Microsoft Azure Blob Storage — Microsoft’s object storage solution for the Cloud. Blob storage is optimized for storing massive amounts of unstructured data (data that doesn’t adhere to a particular data model or definition, such as text or binary data).
How cloud storage exposures commonly happen (Azure context):
- Anonymous/public access is enabled at the container or blob level (intentionally or accidentally).
- A storage area intended for public assets (e.g., recordings) is reused for sensitive exports (e.g., registrant CSV/JSON).
- Access relies on “link-only” sharing, but the files remain technically public if the container permits it.
- Without strict separation, audits, and logging, sensitive files can be uploaded to the wrong place and remain exposed.
| Timeline of Events | |
|---|---|
| Data Leak Discovered | June 10th, 2021 |
| Reported On | June 10th, 2021 |
| Was the Issue addressed? | Yes |
| Comment provided by EventBuilder? | No |
Data Exposure Summary
As mentioned above, the EventBuilder platform is widely used by Microsoft and integrated with their Teams solution. The storage in question was supposed to be partially public, to host recorded sessions for link-only access. However, for some reason, the webinar organizers were putting registrant information into the blob. This meant it was open to indexing by a Public Bucket searcher (Grayhat Warfare), thus compromising their personal information and potentially putting them in danger of being targeted by hackers from across the globe.
How this exposure likely occurred
While the exact internal workflow has not been publicly disclosed, exposures of this type typically follow a predictable technical pattern involving cloud storage configuration and file handling practices. The high-level sequence below illustrates how publicly accessible containers can unintentionally expose sensitive registrant exports.
- A storage location was configured to allow public/anonymous reads for hosting webinar recordings.
- Event or webinar administrators exported or uploaded registrant data files (CSV/JSON) into the same location.
- Public indexing services and crawlers were able to discover and index those files.
- Anyone with access to the indexed links could potentially download and compile the exposed records.
Information Included in the Data Leak
Thousands of large-sized CSV/JSON files with Microsoft events registrants details and summaries, including:
- Full names
- Email addresses
- Company names and position in the company
- Phone numbers
- Questionnaires answered
The estimated number of records leaked is unknown but based on the exposed file sizes, it could run into the hundreds of thousands.
Cloud storage leaks and exposed registrant lists can increase the risk of phishing, account takeover attempts, and identity misuse. Clario Anti Spy (available on iOS and Android) helps you monitor whether your personal data has already been exposed and guides you in strengthening your device security.
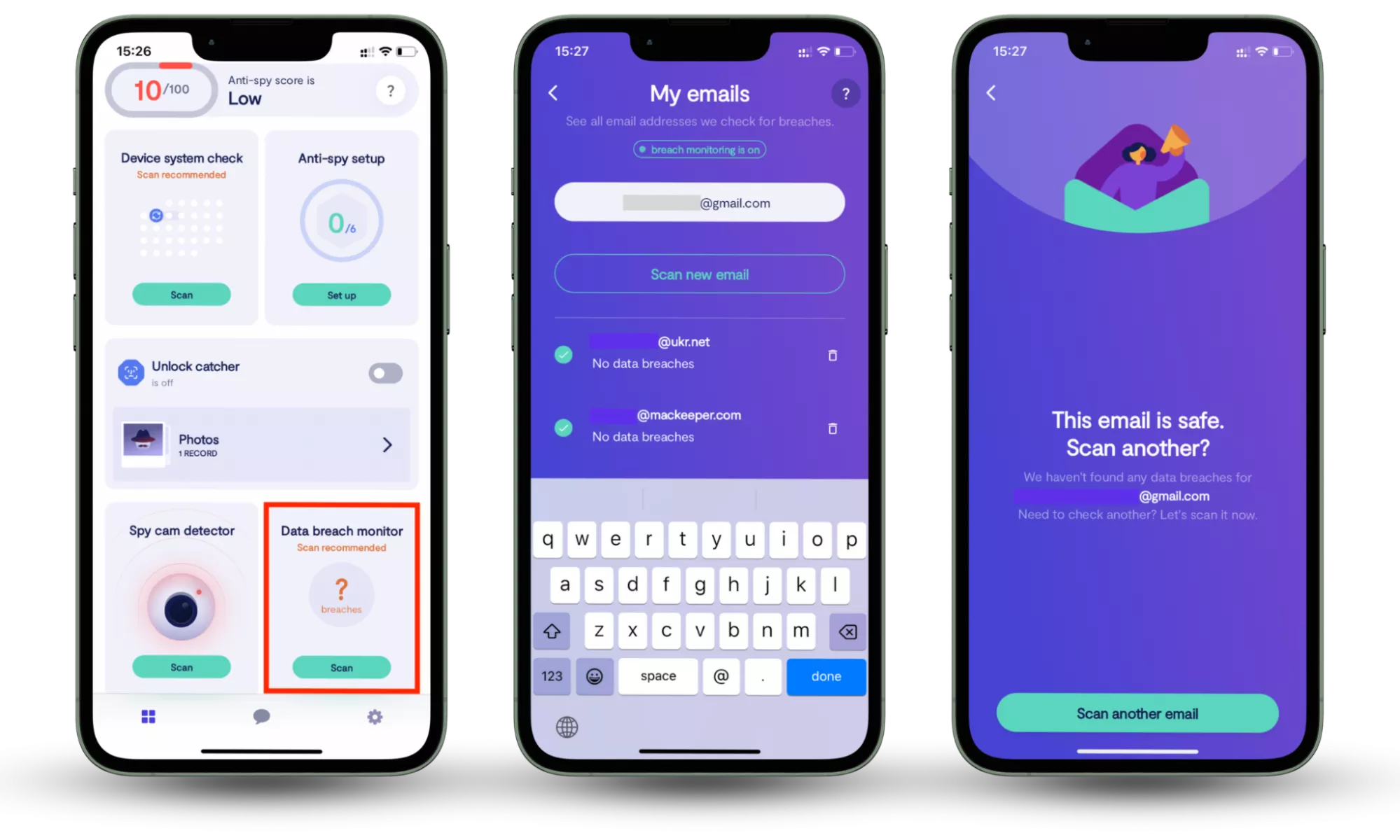
Data Breach Monitor (iOS & Android):
- Scans your email address for known data breaches
- Shows which accounts may be accessible to attackers
- Notifies you if your data appears in newly discovered breaches
- 24/7 monitoring is enabled by default
Here is how to check whether your information is compromised:
- Download Clario Anti Spy.
- Open the app, and, under Data breach monitor, tap Scan.
- Enter your email address.
- When the scan is complete, follow the on-screen guidance to review any data breaches.
- Repeat the process for any other email addresses.
Because exposed email addresses and contact details are commonly used in targeted phishing campaigns, early detection allows you to secure vulnerable accounts before attackers attempt exploitation.
Why these fields are sensitive (practical attacker use):
- Full name + email → targeted phishing and credential-harvesting lures
- Phone number → smishing (SMS phishing) and vishing (phone-based scams)
- Company + job role → business email compromise targeting and invoice/payment scams
- Questionnaire responses → personalization that makes social engineering messages more convincing
As can be seen, this was a serious leak of sensitive data containing potentially lucrative information to any unfriendly hackers that may have gained access to it.
Expert Advice
Was this a preventable data exposure? Undoubtedly! Online security is not a luxury in this day and age, but a necessity. Any company can avoid finding themselves in this dangerous situation by following some essential, but really quite simple, security measures:
- Make sure you implement proper access rules and only allow authorized personnel to access any sensitive information
- If a system doesn’t require authentication, never leave it open to the internet
- Don't ignore your corporate desktop and mobile security hygiene
Common pitfalls that lead to repeat exposures:
- Storing PII files in the same place as public webinar assets
- Assuming “unguessable links” are private access control
- Leaving old exports (CSV/JSON) online after an event ends
- Granting broad upload permissions without validating where files are being uploaded
- Skipping periodic permission reviews when teams or vendors change
With Clario Anti Spy protection, you’re always safe. It allows you to:
- Guard your online identity with 24/7 Data Breach Monitoring that scans your email for exposed accounts and alerts you if your data appears in new breaches
- Detect suspicious or hidden apps on your device with a Hidden App Scan designed to identify spyware and unusual permission requests
- Strengthen your device’s security posture with a Device System Check that verifies OS updates and flags potential system compromise (such as jailbreak on iOS)
- Capture evidence of unauthorized access attempts with Unlock Catcher, which records photos of anyone who unlocks your phone
- Identify suspicious devices connected to your network using the Spy Cam Detector
- Get help anytime with 24/7 human assistance from security experts
Please check out the Clario Anti Spy website for further information on how Clario can cover all your privacy requirements.