Table of contents
- How Serious Are USB-Attacks?
- What is a USB attack?
- What are the threats?
- How does a USB virus attack devices?
- How to prevent bad USB attacks?
- How to prevent bad USB attacks on Windows PCs?
- How to prevent bad USB attacks on Mac computers?
- How to prevent bad USB attacks on iPhone and iPad?
- How to prevent bad USB attacks on Android phones?
- What to do after connecting a suspicious USB device?
- Conclusion
How Serious Are USB-Attacks?
Did you know USB drives were once banned from the US Defense Department offices after one infected their computer system with a virus? This ban was later lifted, leading to infamous whistleblower Edward Snowden stealing NSA’s dark secrets on a thumb drive and sharing his findings with the world. And these are just two memorable examples out of many other USB-related scandals.
But let’s focus on your USB safety. Here, Clario Anti Spy will teach you how to prevent USB-based attacks and still keep using flash drives.
What is a USB attack?
A USB attack is a cybersecurity threat that uses a USB-connected device to compromise a phone, tablet, or computer. Attackers can use infected flash drives, fake keyboards, malicious charging stations, or compromised USB firmware to deliver malware, steal data, or gain unauthorized access. USB attacks affect both desktop systems and mobile devices, including iPhones and Android phones.
Note
USB attacks generally fall into two categories: removable-media attacks that rely on infected files or firmware, and USB connection attacks that exploit charging ports, trust permissions, or device emulation.
There are at least 29 different types of USB malware attacks capable of being carried out in many different ways. Here are the most common ones:
- Through USB drives. A USB can accidentally download an infected file from someone’s laptop, then transfer it to yours. Or a USB drive can be purposefully infected, then either directly or indirectly handed to you. Like, dropped in a parking lot for you to find it (it’s called a USB drop attack and is more popular than you’d imagine).
- Through USB ports in charging devices or stations. This is called juice-jacking, and there isn’t any information or guidance on how to protect a USB from the virus in this situation. The only way to stay safe is to avoid using public charging stations. Just carry a regular plug-in charger with you or keep a spare power bank on your person at all times.
Security note
Modern smartphones include protections against many unauthorized USB data connections, but public charging stations can still pose privacy and security risks. If possible, use a wall charger, a personal power bank, or a USB data blocker that prevents data transfer. On an iPhone, iOS may display a “Trust This Computer” prompt before allowing data access through USB. Android devices typically require users to manually enable file transfer mode before data sharing is allowed. Using a charge-only cable instead of a full data cable can also reduce exposure to unauthorized USB communication.
USB threats aren't just a security issue on desktops. Mobile devices now support USB drives, so your phone could also be at risk. The best way to stay protected is by ensuring your iPhone or Android is running the latest and most secure version of the system software. An anti-spyware solution like Clario Anti Spy can help with that.
Here's how to run a Device system check with Clario Anti Spy:
- Download and Clario Anti Spy and subscribe to create an account.
- Tap Scan under Device system check.
- Wait until the scan to complete and follow the instructions to resolve any security issues.
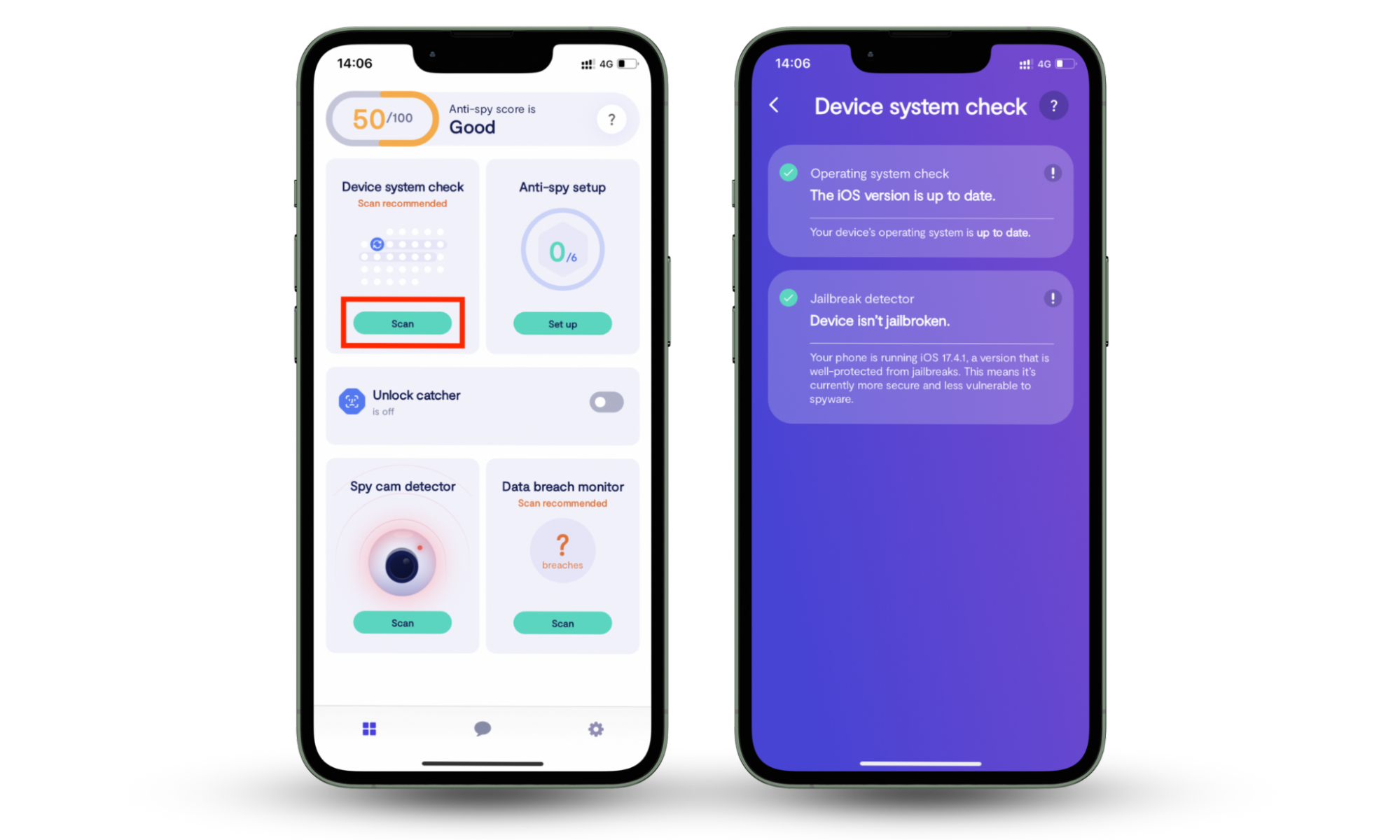
Clario Anti Spy also comes with more tools to keep your device secure. Don't miss out on the Anti-spy setup to enhance privacy across all areas and the Data breach monitor to receive alerts if your email or password is compromised. If you need help, tap the Messages icon to connect with a security expert 24/7.
What are the threats?
USB attacks can lead to malware infections, credential theft, unauthorized remote access, ransomware deployment, and hardware compromise. Some attacks rely on infected files stored on USB drives, while others use fake USB devices that imitate keyboards or trusted accessories. Both personal devices and workplace systems can be affected.
There are quite a few ways an infected USB key can compromise your safety:
- Malicious USB software can allow a hacker to control your device
- A third-party can acquire access to your webcam, microphone, or keyboard
- Hackers can steal your personal information or erase random data on your device
- An infected USB drive can even destroy your hardware
- Ransomware can encrypt files after malicious software launches from a USB device
- Attackers may steal saved browser passwords, authentication tokens, or cryptocurrency wallet information
- Some malware monitors clipboard activity to capture copied passwords or payment details
- Advanced attacks can execute PowerShell or terminal commands automatically after connection
- Fake USB accessories may install remote-access tools that allow attackers to monitor activity silently
One of the most infamous and dangerous USB drop attacks is called Stuxnet. Once it infected software at industrial sites in Iran, including a uranium-enrichment plant. And well, the Iranese government systems were probably using cybersafety software.
Still, a maliciously dropped USB stick managed to crawl its way into the system.
Important to know
Stuxnet became one of the most well-known USB-based cyberattacks because it spread through removable media in highly restricted “air-gapped” industrial environments that were not directly connected to the internet. This attack targeted industrial control systems and required significant technical sophistication, making it very different from most consumer malware.
How does a USB virus attack devices?
USB malware attacks typically work by executing malicious files, tricking users into revealing sensitive information, or impersonating trusted USB hardware. These attacks remain effective because operating systems often recognize USB devices automatically, and users may trust familiar-looking accessories without verifying their origin.
Though, we can name three main types of USB malware attacks:
- Malicious code is the most common USB attack. Once a user clicks on a file on a shady USB drive, it launches malicious code to download malware from the internet.
- Social engineering. Once a user opens the necessary file on a malicious USB stick, the person is redirected to a phishing site designed to trick them into typing personal information and credentials (email password, credit card details, etc.)
- HID or Human Interface Device spoofing. Designed like a USB drive, this hardware tricks users’ computers into thinking it’s a keyboard. Once plugged in, it commands the device to grant remote access to hackers. Crazy, right?
Attackers often label malicious USB drives with names designed to trigger curiosity or urgency, including:
- “Employee Salaries”
- “Confidential HR Files”
- “Event Photos”
- “Invoices”
- “Company Benefits 2026”
USB drop attacks may also happen at conferences, office parking lots, coworking spaces, or public libraries where people are more likely to connect found devices.
Security limitation note
Because the operating system may treat the device as legitimate hardware instead of a suspicious file source, some HID attacks can bypass traditional antivirus scanning.
How to prevent bad USB attacks?
The most effective way to prevent USB attacks is to avoid connecting unknown devices, disable automatic file execution features, keep operating systems updated, and scan removable media before opening files. Security software can help detect known threats, but safe USB habits remain essential because some hardware-based attacks bypass traditional antivirus protections.
First of all, remember you are in charge of your safety, so follow these basic rules to stay secure:
- Keep personal and work-related USB sticks separately
- If you don’t know where the USB drive is coming from, don’t use it
- Occasionally change and update your USB keys
- Regularly scan your USB drives and devices with an antivirus
- Disable autorun features on all your devices (this will prevent any unknown files from launching without you knowing or giving permission)
- If you really need to get information from an unknown USB source, plug it into some sort of buffer device and scan it for malware
- If you have already plugged a suspicious USB drive in, immediately disconnect from the internet to prevent any downloads and restart your device
- Or avoid using USB sticks at all times! Just kidding. Get quality antivirus software instead.
Security note
According to NIST (National Institute of Standards and Technology) guidance on removable media security, organizations and individuals should treat USB storage devices as potential attack vectors and scan external media before accessing files.
How to prevent bad USB attacks on Windows PCs?
- Disable AutoRun and AutoPlay features to stop files from launching automatically.
- Scan removable drives with Microsoft Defender or another trusted antivirus solution before opening files.
- Organizations may use Group Policy settings to block unauthorized USB devices entirely.
How to prevent bad USB attacks on Mac computers?
- macOS handles removable media differently from Windows and does not rely on AutoRun in the same way.
- Users should still avoid opening unknown files or granting unnecessary permissions to external devices.
- Keep macOS and security software updated regularly.
How to prevent bad USB attacks on iPhone and iPad?
- Avoid connecting unknown USB accessories to unlocked devices.
- Review accessory permissions carefully when iOS displays trust prompts.
- Use official or trusted charging accessories whenever possible.
How to prevent bad USB attacks on Android phones?
- Disable USB debugging unless actively needed.
- Review USB connection modes before enabling file transfer.
- Be cautious when connecting external drives through USB OTG adapters.
Security note
Android Security guidance also recommends disabling USB debugging when it is not actively needed and carefully reviewing USB permissions before allowing file transfers or external accessory access.
What to do after connecting a suspicious USB device?
- Disconnect the USB device immediately
- Disable internet access temporarily to reduce the risk of additional downloads or remote communication
- Run a full antivirus or endpoint security scan
- Review recently installed applications, startup items, and browser extensions
- Change important passwords if sensitive information may have been exposed
- Monitor email, banking, and online accounts for unusual activity
- Contact IT support if the affected device belongs to your workplace or school
Conclusion
If it’s predictable, it’s preventable. Now you know USB security tricks, you should be able to keep away from potential threats. And your antivirus will take care of the rest. However, don't forget your mobile devices—install Clario Anti Spy to make sure your phone's system software is safe and secure.


