Table of contents
- Company profile
- Data Exposure Summary
- Data Breach Impact
- User Impact
- Impact on ISOC
- Data Breach Summary
The Internet Society (ISOC) is one of the oldest and most important international non-profit organizationss related to the internet, but, despite its prestigious reputation, personal details of its members were found to have been exposed in a recent data security breach.
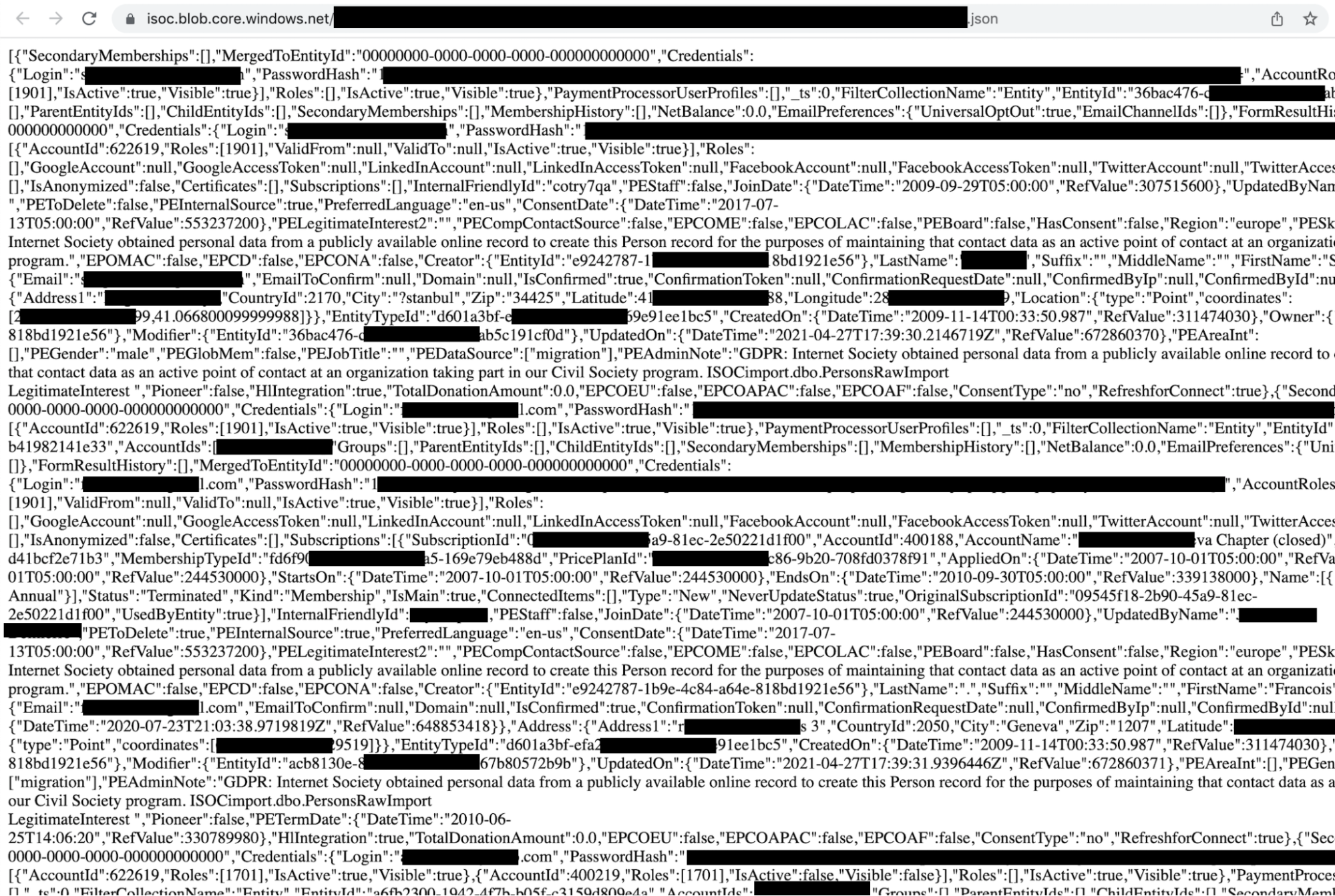
Our team of researchers recently discovered an open and unprotected Microsoft Azure blob repository containing millions of files with personal and login details belonging to ISOC members.
A Microsoft Azure blob repository is a cloud storage service used to store large amounts of unstructured data, which can become publicly accessible if not properly secured.
Company profile
Founded in 1992, ISOC’s mission is to ensure open internet development by enhancing and supporting internet use for organizations and individuals worldwide. As half of the world does not have online access, the organization’s initiatives are aimed at reducing this divide and making it more accessible. According to the body, its membership has now grown to more than 80,000.
Timeline | |
|---|---|
| Data Leak Discovered | December 8th, 2021 |
| Reported On | December 8th, 2021 |
| Was the Issue addressed? | Yes |
| Comment provided by the Internet Society? | Yes |
Data Exposure Summary
The data exposure occurred due to a publicly accessible Microsoft Azure blob storage container that required no authentication to access. This misconfiguration allowed millions of structured files containing personal details, login-related information, and social authentication tokens of ISOC members to be viewed or potentially downloaded by anyone with access to the storage URL.
The open and unprotected Microsoft Azure blob repository contained millions of files with personal and login details belonging to ISOC members and potentially putting their privacy at risk.
Based on the size and nature of the exposed repository, we can assume that all of the members' login and adjacent information was open to the public internet for an undefined period of time.
A blob container named ISOC contained millions of json files that were structured to include the following:
- login
- password hash
- isActive / Visible flags
- accountID
- social media tokens (if used to login): LinkedIn/Google/Facebook/Twitter
- joinDate
- preferredLanguage
- address (with zip and coordinates)
- gender
- full name
- pioneer (true or false flag)
- total donation account (amount)
- other service lines
Risk Categorization of Exposed Data
- High Risk: email addresses, password hashes, social media tokens
- Can enable account takeover, credential stuffing, and targeted phishing
- Medium Risk: full name, address, location coordinates
- Can be used for identity profiling, scams, or impersonation
- Lower Risk: language preferences, account flags
- Typically less sensitive but useful for enhancing attack personalization
As soon as the sensitivity of the data and the owner of the repository was confirmed, an email alert was sent to ISOC. On December 15th 2021, the repository was secured and the organization provided the following comment:
Thank you again for following up.
I wanted to let you know that the active investigation into this issue has now concluded. We have confirmed that the association management system we use was configured incorrectly by MemberNova, which made some Internet Society member data publicly accessible. Fortunately, we have not seen any instances of malicious access to member data as a result of this issue.
We notified all our members about this matter before the holidays and worked with MemberNova to correct the configuration issue and restore the system to normal operations. We have also just let our members know that the investigation has wrapped up.
Thank you again for bringing this issue to our attention as your notice allowed us to quickly resolve the situation.
Important to know
Although password hashes are not stored in plain text, they can still be vulnerable to cracking depending on the hashing algorithm used and whether users reused the same passwords across multiple services.
Data Breach Impact
The impact of this data breach includes both immediate and long-term risks for affected users and the organization. Exposed personal and authentication-related data can be used for phishing, identity theft, and account compromise, while the organization may face reputational damage and reduced trust. Even without confirmed misuse, such exposures create ongoing security risks due to potential delayed exploitation.
While many ISOC members are looking to support the organization in its mission, the exposure of their sensitive details could have put them at risk of being attacked by cybercriminals.
How attackers could use the exposed data:
- Extract and organize personal data. Attackers can collect email addresses, names, and account identifiers from the exposed files.
- Cross-reference with other breaches. The data may be combined with previously leaked credentials to identify reused passwords or additional personal details.
- Launch targeted phishing campaigns. Using accurate personal information, attackers can craft convincing emails that appear legitimate.
- Attempt account takeover. Password hashes or social login tokens may be used to gain unauthorized access to user accounts.
- Exploit identity data for fraud. Personal details such as names and addresses can be used to impersonate individuals or create fraudulent accounts.
User Impact
The exposure of personal and account-related data creates multiple risks for affected users, including phishing attacks, identity theft, and unauthorized account access. When sensitive information such as email addresses, authentication data, and personal identifiers is exposed, attackers can combine these elements to carry out highly targeted and convincing attacks that are more difficult for users to detect.
Phishing
Phishing is a form of cybercrime where scammers target online users to hand over money or personal information. With information such as an email address, name or password, they could have tricked ISOC members into transferring them cash or inadvertently falling prey to a hack.
Example scenario
An attacker could use a member’s name, email address, and association with ISOC to send a convincing email requesting a password reset or donation confirmation. Because the message contains accurate personal details, it may appear legitimate and increase the likelihood of the recipient clicking a malicious link or providing additional sensitive information.
Identity Theft or Fraud
With personal details such as name, date of birth or email address, scammers could have impersonated ISOC members to commit fraud or identity theft in their name. For example, they could have potentially set up online accounts or even donated funds without their knowledge or consent.
Impact on ISOC
The data exposure may have significant implications for ISOC, including reputational damage, reduced member trust, and increased scrutiny of its security practices. As an organization associated with promoting internet standards and best practices, such incidents can raise concerns about governance, third-party risk management, and the effectiveness of internal security controls, even if the issue originated from a vendor misconfiguration.
Loss of reputation
There are challenges for ISOC if this data breach had been widely reported with loss of reputation the main issue. As the organization works in the online world and is viewed as an upholder of standards and best practice it could be particularly embarrassing if this had come out. The breach suggests ISOC needs to do more to enhance their security infrastructure and adhere to the best practices they champion around making the internet stronger and more secure.
How to stay safe from data breaches
At Clario, we aim to work 24/7 to ensure that user personal data is kept secure. In case of a data breach, we advise:
- Immediately open your account and change your passwords
This is the easiest and fastest way to ensure your accounts stay secure, especially if you take action as soon as you find out that a security breach has occurred. Remember that your passwords should be updated every 180 days as best practice anyway.
- Cautiously approach suspicious-looking emails or links
Follow your instincts and be careful if you see anything suspicious. If you suddenly start getting bombarded with certain ads or deals which seem too good to be true, then tread carefully so you can avoid becoming a cybercriminal’s latest victim.
- Work with a trusted cybersecurity provider…
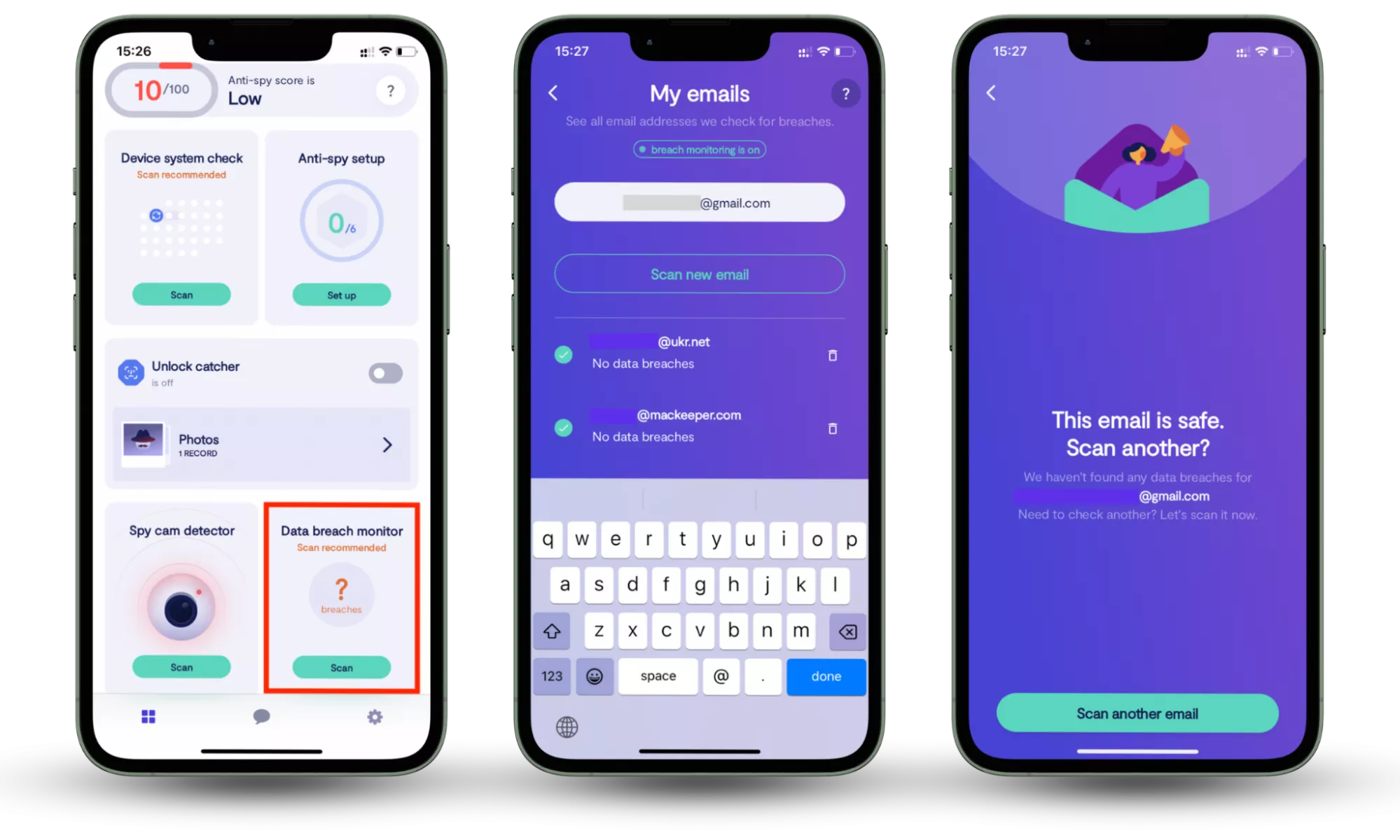
A Data breach monitor helps identify whether your personal information has already been exposed online and alerts you to new risks as they appear. Clario Anti Spy includes a built-in data breach monitoring feature that scans your email against known breach databases and continuously checks for new exposures.
How to check whether your information is compromised:
- Download Clario Anti Spy.
- Open the app, and, under Data breach monitor, tap Scan.
- Enter your email address.
- When the scan is complete, follow the on-screen guidance to review any data breaches.
- Repeat the process for any other email addresses.
Data Breach Summary
This data breach involved the exposure of millions of Internet Society (ISOC) member records due to a misconfigured Microsoft Azure storage container. The exposed data included personal information and login-related details, which may have been accessible to the public internet for an unknown period. The issue was later identified and secured after responsible disclosure.
| Affected company | ISOC |
| Exposed environment | Microsoft Azure blob repository |
| Type of data exposed | Personal and login details of ISOC members |
| Estimated number of records | Millions of files were reportedly exposed |
| Publicly indexed by | Unknown public search engine |
| Discovered on | December 8th, 2021 |
| Reported on | December 8th, 2021 |
| Issue addressed | Yes |
Although the issue has been resolved, the exposure of structured user data increases the risk of delayed exploitation. Attackers may store exposed information and use it later for phishing, credential-based attacks, or identity fraud, even if no immediate misuse was detected at the time of discovery.
Users concerned about potential exposure may benefit from monitoring whether their personal data appears in known breaches. Tools such as Clario Anti Spy include a Data breach monitoring feature that scans email addresses against breach databases, identifies affected accounts, and provides alerts if new exposures are detected, helping users take timely action to secure their information.


