Table of contents
- What is a computer worm?
- Famous computer worms
- What is a computer virus?
- Types of computer viruses
- Notorious computer viruses
- What is the difference between a virus and a worm?
- Virus vs. worm: which is more dangerous?
- How a computer worm spreads
- Example of a worm infection
- How a computer virus spreads
- Example of a virus infection
- How to tell if your device is infected
- How to protect all your devices from viruses and worms
- Avoid opening suspicious emails and links
- Use an ad blocker
- Use a trusted antivirus
- Don’t connect to unsecured networks without a VPN
- Keep your operating system up-to-date
- Wrapping Up
What is a computer worm?
Definition
A computer worm is a form of malware that self-replicates and independently spreads to other computers, without requiring human intervention. It often uses an infected computer’s network to spread itself, usually by exploiting a network security vulnerability.
In malware, the part of code designed to do harm is called the payload.
The payloads of computer worms are designed to:
- Steal data, like confidential documents and passwords
- Delete files on a host system
- Encrypt files for a ransomware attack, which holds data for a monetary ransom
- Create “backdoors” to devices for remote access by cybercriminals
Now that we know their potential, let’s discover how computer worms have impacted cybersecurity through the years:
Famous computer worms
Because they’re designed to spread rapidly and do serious damage, there have been a number of notorious incidents involving computer worms causing widespread damage.
Here are some famous computer worms:
- Morris Worm: Released in 1988, Morris Worm was one of the first computer worms to get widespread attention. It spread through the internet by exploiting weak passwords and other security flaws, causing infected computers to slow down or crash.
Though it wasn’t designed to be malicious, it infected thousands of computers and disrupted the early internet. Morris Worm was a landmark event for computer security that helped raise awareness about the importance of cybersecurity and network protections.
- ILOVEYOU Worm: The ILOVEYOU worm spread through email attachments in 2000, but it was no love letter. It arrived with the email subject ILOVEYOU, along with an attachment containing the malware worm. Once opened, it would infect the computer and replicate itself, sending copies of the email to everyone in the user’s address book.
The worm was designed to overwrite files or replace the original content with new content. It spread itself through network drive and the internet, and created backdoors for cybercriminals. It affects businesses, governments, and individuals. Also, it is said to have infected millions of computers, with an estimated $15 billion in total damages.
- WannaCry: The WannaCry worm operated as a blended threat with aspects of a worm and ransomware. It infected devices through the EternalBlue exploit, then encrypted files and demanded bitcoin in exchange for the decryption key. It spread itself by scanning the network for other devices with similar security vulnerabilities.
WannaCry caused considerable disruption and financial damage by targeting businesses, hospitals, and other organizations. The UK’s National Health Service (NHS) was particularly affected. It’s considered one of the biggest ransomware attacks in history, affecting over 200,000 computers in over 150 countries.
What is a computer virus?
Definition
A computer virus is a form of malware that replicates itself by attaching to other files on a device or network. Once that file is opened, the virus is activated and can infect other files or devices. In order to spread, viruses require human interaction, like opening an infected email attachment or downloading an infected file from the internet.
The payloads of a computer virus are designed to:
- Destroy or alter files on the infected device
- Steal confidential and personal data
- Spy on the infected system
- Launch denial-of-service attacks, which slow down or disable websites and networks
- Send spam emails or launch new attacks via the infected device.
Although that’s a tall order of damages, an individual virus generally carries out a specific payload. Different viruses are designed for different tasks. Let’s take a closer look at some common varieties:
Types of computer viruses
Just like the biological varieties, computer viruses each have their own characteristics and means of infection.
Here are some common types of computer viruses:
- File infectors attach to files on an infected device and are activated when the files are opened.
- Macro viruses infect files that contain macros, commands, or instructions recorded and saved in software apps, like Microsoft Word or Excel. They can spread through email attachments or shared network drives.
- Boot sector viruses infect the boot sector of your hard drive, which is responsible for starting up your computer’s operating system (OS). Because the virus targets a crucial part of your hardware, it can be difficult to get rid of.
- Polymorphic viruses change their code each time they infect a new system, so they’re difficult to detect and delete.
- Resident viruses remain within a device’s RAM memory, even after removing their source file, continuing to infect files and networks.
- Multipartite viruses: These viruses infect both files and boot sectors, making them very tricky to remove.
Notorious computer viruses
Featured in movies and books, computer viruses have captured the popular imagination more than any other form of malware. But along with celebrity status, computer viruses have a history of cybersecurity mayhem to back it up.
Learn more
Check out our guide to computer virus names for a rundown of the most notorious computer viruses through the years.
What is the difference between a virus and a worm?
A virus and a worm are both forms of malware that are designed to spread rapidly — the difference is that a virus requires human interaction and a host file, whereas a worm does not. A virus needs you to open the infected file in order to infect the system, replicate, and spread. A worm can autonomously replicate and spread itself.
Virus vs. worm: which is more dangerous?
Both viruses and worms are dangerous, depending on their characteristics, but worms are generally considered more dangerous. Unlike viruses, worms have the ability to self-replicate without a host file or human interaction. This helps them spread rapidly through networks and makes them more difficult to detect since infection is not always obvious.
How a computer worm spreads
Computer worms are designed to spread themselves, without the need for human interaction. A worm typically spreads by exploiting a security vulnerability in an operating system or network to gain access to a system, then uses that access to spread independently to other devices or networks.
Here’s the process of how computer worms spread:
- Infection: The worm activates when it's executed on a vulnerable system, either through an email attachment, a file download, or a network connection.
- Scanning: Once it infects the system, it scans the local network or internet for other vulnerable systems.
- Exploitation: Once the worm finds a vulnerable system, it exploits the same vulnerability to gain access and execute itself to the new system.
- Replication: The worm replicates itself on the newly infected system and continues spreading by scanning and exploiting other systems.
This vicious cycle moves fast and has the potential to spread rapidly to a large number of devices. Now, let’s walk through the worm infection process with a real-life example:
Example of a worm infection
The WannaCry computer worm was one of the most effective in history. Here’s how it was able to infect and quickly spread to over 200,000 systems worldwide in May 2017.
- Initial infection: The WannaCry worm initially infected devices by exploiting a key vulnerability in Microsoft Windows called Eternal Blue.
- Scanning: Once a system was infected, WannaCry scanned local networks for other systems to infect. It used the Server Message Block (SMB) protocol to scan open ports and search for unpatched Windows systems.
- Exploitation: Once a new system was found, WannaCry would exploit it via the Eternal Blue vulnerability.
- Payload: With access to the system, WannaCry would encrypt files on the device and display a ransom note demanding Bitcoin in exchange for the decryption key.
- Replication: With the files encrypted, WannaCry used the same SMB protocol to search for other systems to infect.
How a computer virus spreads
For a computer virus to spread, it requires someone to open an infected file. Once the system is infected, the virus can replicate itself and attempt to spread to other systems.
Here’s the process of how computer viruses spread:
- Infection: The virus infects an initial system by tricking someone into opening a file containing the virus. This happens through downloading an infected file, opening an email attachment, or visiting a malicious site.
- Replication: Once it infects a system, the virus creates multiple copies of itself. It may even hide in different locations within the system, like the memory, hard drive, or files and folders.
- Spreading: The virus attempts to spread by sending copies of itself to other systems within the same network or the internet. This can be done via email, messaging, file-sharing networks, or by exploiting vulnerabilities in network protocols.
Now let’s take a look at a computer virus in action using a real-life example:
Example of a virus infection
CryptoLocker is a recent example of a computer virus that really rocked the cybersecurity world. Here’s how CryptoLocker was able to extort around $3 million from victims in 2014.
- Infection: CryptoLocker infected systems when users opened phishing emails, infected attachments, or malicious links.
- Encryption: Once it infected a system, the virus searched for files to encrypt, including photos, videos, documents, and other valuable data. The virus would then demand a ransom in exchange for the decryption key.
- Replication/Spreading: When infecting a system, CryptoLocker would also replicate itself and search for files located on other devices connected to the infected computer, like network drives, external hard drives, or cloud storage.
How to tell if your device is infected
A malware infection can be obvious or subtle, depending on the characteristics of the threat. But there are some surefire ways to detect an infection.
Here’s how to tell if your device is infected:
- Performance issues: If your device is suddenly slower, crashing, or generally acting strange, it could be a sign of infection. Performance issues can be caused by viruses or worms using system resources or because of their payload.
- Pop-up ads or ransoms: If you receive random pop-up ads, especially for software or services you never installed, this could be due to malware. Another obvious sign is a ransom demand in exchange for reversing damages or decrypting your data.
- Changed settings or unusual network activity: If your device is changing network or other settings that you didn’t authorize, it could be malware. Another sign could be increased network resource usage or unusual network activity, like connections to unfamiliar IP addresses.
Whether dealing with worms or viruses, early threat detection is key. Clario Anti Spy’s Hidden app scan helps you stay safe by checking your device for secretly installed spying apps, stalkerware, and other hidden malware.
Follow these steps to run Hidden app scan:
- Download Clario Anti Spy and create an account.
- Open Hidden app scan.
- Tap Scan.
- Review the list of suspicious apps and permissions.
- Follow the recommendations to remove threats.

And that’s it! If the app detects any malware threats, it will quickly strike to stop the threat and prevent its spread. Clario’s antivirus tool gives you hassle-free and powerful malware protection that’s always on duty.
How to protect all your devices from viruses and worms
Viruses and worms can be nasty, so evading them all together is the best strategy. Luckily, that’s not so hard to do. To avoid worms, viruses, and other forms of malware, apply these tried and tested security tips:
Avoid opening suspicious emails and links
Worms and malware often spread and gain access to a system via infected email attachments and malicious links. Don’t open suspicious emails and avoid links on unverified websites. Hackers will also try to create convincing ploys with suspiciously great deals or emotional language. Don’t fall for it!
Use an ad blocker
Malversting, or malware-infected ads, can do serious damage with just one click—or sometimes without any interaction. You can avoid this pitfall with an ad blocker, like the one featured in the Clario app. It also stops ad trackers from following your online activity.
Use a trusted antivirus
A trusted and dedicated antivirus tool, like the one featured in the Clario app, can stop malware in its tracks—way before you even realize it’s there. Quality antivirus makes device security easy, so you don’t have to constantly stay vigilant to potential threats.
Don’t connect to unsecured networks without a VPN
Worms and viruses rely on unsecured networks to spread to other devices. A VPN will hide your location from hackers and other snoops and encrypt your internet traffic. With a VPN, potential malware threats won’t stand a chance of infecting your device through unsecured networks.
Keep your operating system up-to-date
Regularly updating your operating system protects you from the latest bugs and security vulnerabilities. To gain access to devices, worms, and viruses, rely on system vulnerabilities. System updates fix these vulnerabilities so hackers can’t exploit them.
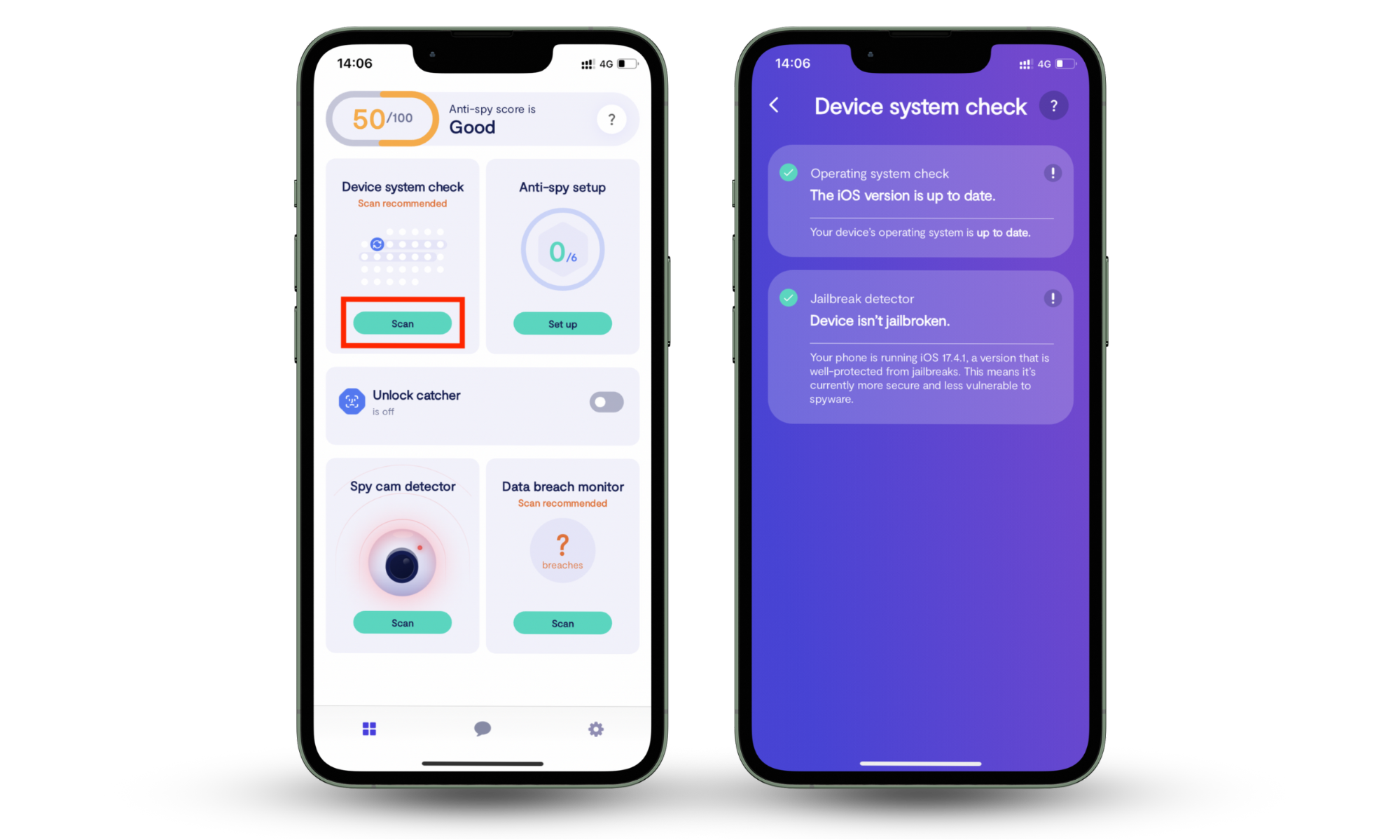
Clario Anti Spy’s Device system check helps by scanning your phone for missing updates or jailbreak risks. If it finds a gap, it gives you clear recommendations so you can patch vulnerabilities before attackers use them.
Follow these steps to run Clario Anti Spy’s Device system check:
- Download Clario Anti Spy and create an account.
- Open Device system check.
- Tap Scan.
- View the results on your device.
- Follow the recommendations to secure your system.
Wrapping Up
The best defense against viruses, worms, and other forms of malware is prevention. Clario Anti Spy protects you with tools built for early detection and system security. Hidden app scan finds malicious or spying apps before they can spread, while Device system check closes the system flaws that worms and viruses rely on. Together, they give you simple but powerful ways to keep malware off your device.


