Table of contents
- What is encryption?
- How encryption protects data
- When should encryption be used?
- Everyday examples of data encryption
- Why is data encryption important?
- Can encryption be hacked?
- Is encryption safe?
- How to protect yourself where encryption doesn’t
- Conclusion
Google encrypts 95% of the traffic. What does it mean? What is encryption?
When Google says it encrypts most traffic, it means connections to many Google services use HTTPS (TLS encryption), so data is protected while traveling between your device and Google’s servers. Encryption helps prevent third parties (like Wi-Fi snoops or network attackers) from reading or altering information in transit. It doesn’t stop all risks if a device is infected or credentials are stolen, attackers may still access accounts.
Important to know:
Encryption mainly protects data in transit; it doesn’t automatically protect what happens on your device (malware) or what you share after it reaches an online service.
What is encryption?
Encryption is a security technique that uses mathematical algorithms and cryptographic keys to transform readable information into a protected format that unauthorized parties cannot understand. Only someone with the correct key can restore the original data. Encryption is widely used in web browsing (HTTPS), online banking, cloud storage, and secure messaging to reduce the risks of interception and data exposure.
Encryption is the process of making data unreadable to an unauthorized party. This is achieved by turning original data into seemingly random data using a cryptographic key. Later, this original data can be deciphered by an authorized party using the key.
How encryption works:
- Data is prepared for protection.
- An encryption algorithm combines the data with a secret key.
- The output becomes unreadable to unauthorized viewers.
- The correct key restores the original information for authorized access.
There are two main types of encryption: symmetric and asymmetric. Symmetric encryption involves a single cryptographic key for both encryption and decryption. In contrast, asymmetric encryption requires two keys to encode and decode information.
Quick key terms:
- Cipher: the mathematical algorithm used to protect data.
- Cryptographic key: a secret value that controls how data is encrypted and decrypted.
- Symmetric encryption: uses one shared key.
- Asymmetric encryption: uses a public key and a private key.
Note
Even strong encryption can fail in practice if keys are exposed, passwords are weak, or the software implementing encryption is improperly configured.
How encryption protects data
Encryption protects data by preventing unauthorized access and helping verify that information has not been altered during transmission. When you visit an HTTPS website, your browser and the server perform a secure handshake to agree on encryption settings and exchange keys safely. Once established, this encrypted session protects the data exchanged during that visit.
At its most basic level, encryption provides data confidentiality. But it also performs other functions to ensure you can trust encrypted and decrypted data.
- Confidentiality encodes and hides the message
- Authentication verifies the message’s origin
- Integrity proves the message’s contents haven’t been changed since sending
- Non-repudiation ensures a message sender can’t deny sending the message
Encryption vs hashing (clarification)
Encryption is reversible with the correct key, allowing authorized users to recover the original information. Hashing is a one-way process typically used to verify data integrity or securely store password verifiers, not to restore the original data.
To provide confidentiality, information is encrypted using formulas called encryption algorithms, or ciphers. One part of the algorithm must have a variable called a key.This makes the algorithm’s output unique, thereby turning your data into unreadable code.
If your encrypted information is intercepted by an unauthorized user, they have to either guess the encryption algorithm used to encrypt the data or the keys used as variables. Naturally, it’s a tough challenge, and this is what makes encryption such an effective security tool.
In real-world breaches, attackers often bypass encryption by stealing login credentials through phishing, password reuse, or malware. This means strong encryption alone does not eliminate account takeover risks.
It doesn't matter how strong your encryption is—if your accounts credentials get leaked, your data is still at risk. That's where Clario Anti Spy comes in. It's an anti-spyware solution for iPhone and Android that includes a Data breach monitor to alert you if your online accounts are involved in a data breach.
Here's how to activate the Data breach monitor in Clario Anti Spy:
- Download Clario Anti Spy and subscribe to create an account.
- Tap Scan under Data breach monitor.
- Wait for the scan to complete. If your email is found in a data breach, change your passwords immediately starting with critical accounts like banking and email. You'll also get alerts if your email shows up in any future breaches.
- If you need help, tap the Messages icon on the main screen to connect with a security expert.
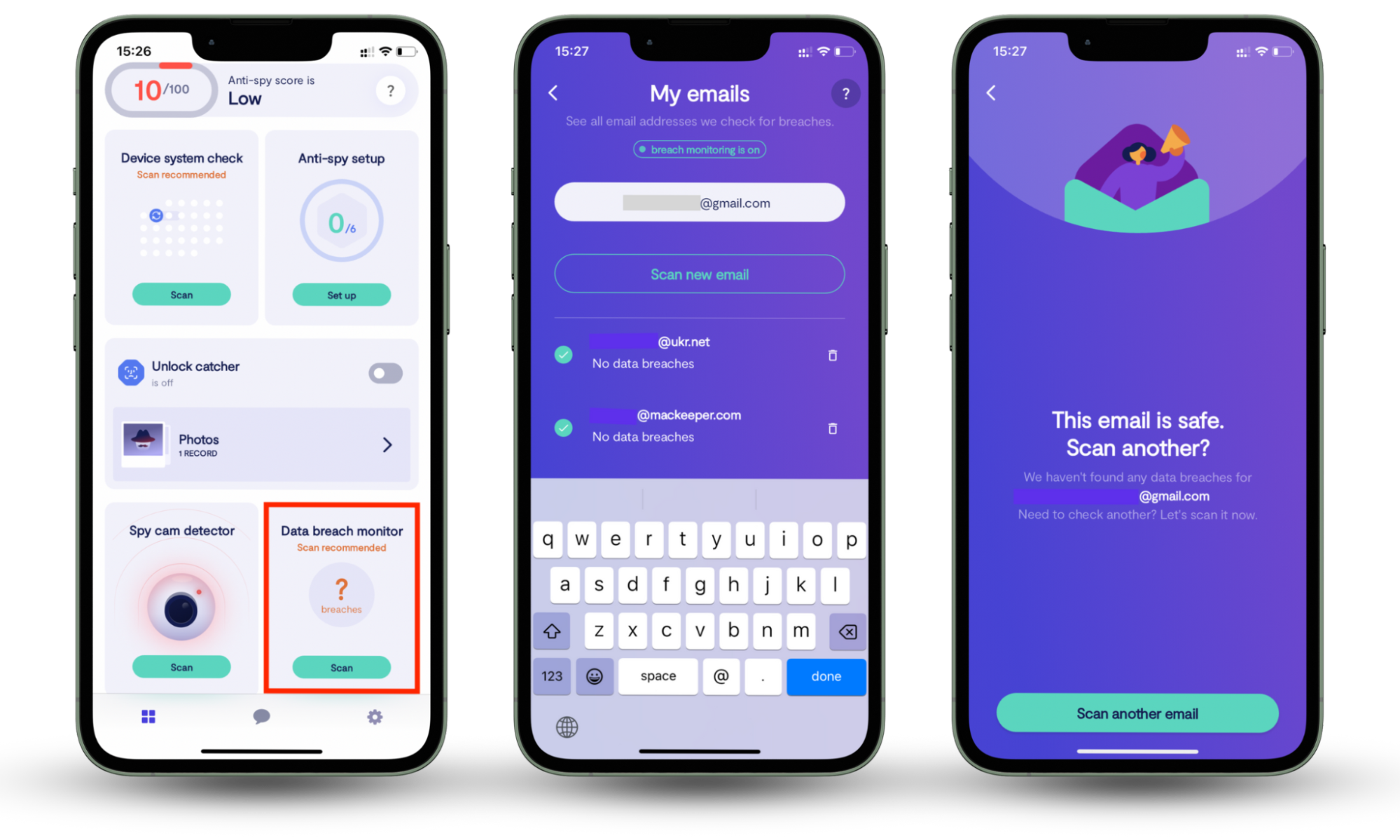
Clario Anti Spy also includes other powerful tools. For example, Device system check helps you detect security risks like hidden jailbreaks or device rooting, while Anti-spy setup walks you through securing your online accounts, web browsing, and social media for better overall privacy.
When should encryption be used?
Encryption should be used whenever sensitive data is stored or transmitted. Data can be exposed through stolen devices, intercepted network traffic, misconfigured cloud storage, or unauthorized system access. As a best practice, encrypt information both while it is stored and while it is moving across networks. This reduces the impact of interception or theft.
There are two scenarios when data should be encrypted:
1. When data is ‘at rest’
Any time data is stored, it should be encrypted to ensure security. For instance, this could be on a removable storage drive or your computer’s hard drive. Responsible organizations will encrypt any data they store.
Examples include laptop and smartphone storage, removable drives, database servers, and cloud backups that contain personal, financial, or business-sensitive information.
2. When data is ‘in transit’
Any time you send data from one place to another, there is a risk of interception by an unauthorized user. By encrypting data, you can minimize the adverse consequences of interception by scammers.
Examples include HTTPS web sessions, email transmission, messaging apps, remote work connections, and any communication over public Wi-Fi networks.
Everyday examples of data encryption
One of the earliest forms of encryption is known as ‘symbol replacement’, which was widely used by the militaries in Ancient Greece and Rome. The Caesar Cipher was a system where each letter in the original message or ‘plaintext’ was replaced by a letter situated a certain number of positions later in the alphabet. You might recall playing similar code-cracking games as a kid.
Of course, today, data encryption is far more advanced. Its use is also incredibly widespread and is likely protecting your data right now without you even being aware of it.
Some examples of common uses of encryption are:
- ATMs - every time you use an ATM the information is protected by encryption
- Online payments - your payment details are protected by encryption
- Encrypted web traffic - many websites encrypt your web usage by default. If you’re using a website with ‘https’ (the ‘s’ stands for ‘secure’) at the beginning of the address, your data is encrypted
- Messaging apps - messenger apps such as WhatsApp have enabled end-to-end encryption. If cybercriminals breach WhatsApp, they won’t be able to decrypt your messages
- Digital rights management systems - prevent the unauthorized use or reproduction of copyrighted content and protect software against reverse engineering
- Data ‘at rest’ - responsible organizations always encrypt data they store
While organizations usually encrypt vast quantities of any data they store, you might also want to encrypt the files and folders on your Mac. Our guide on data encryption for Mac will get you started.
Why is data encryption important?
Encryption is important because it reduces the usefulness of stolen or intercepted data. By transforming sensitive information into a protected format, encryption limits what attackers can do even if they gain access to storage systems or network traffic. It also supports regulatory compliance, privacy protection, and risk management strategies across industries.
Data encryption is an essential privacy safeguard. If someone gains unauthorized access to your encrypted data, they will not be able to read it or use it for malicious purposes. As such, data encryption functions as the final line of defense against cybercrime.
Encryption is important for data security because it can greatly reduce data breach damage. Given that no system is 100% secure, companies operating in healthcare, finance, education, and other critical industries are mandated to encrypt their data. For instance, the Health Insurance Portability and Accountability Act (HIPAA) requires healthcare providers to implement data encryption to protect patients’ health information.
Can encryption be hacked?
In short, yes. Encryption can be compromised, but usually not by directly solving the underlying mathematics. In practice, attackers are more likely to exploit weak passwords, stolen keys, outdated protocols, or software vulnerabilities. Strong modern encryption standards are designed to resist direct decryption attempts without the key, but implementation flaws and human error often create real-world weaknesses.
Common real-world weaknesses include:
- Storing encryption keys insecurely
- Using weak or reused passwords
- Allowing outdated encryption protocols
- Failing to update software that handles cryptographic operations
Is encryption safe?
Yes, encryption is incredibly safe. Encryption is generally considered safe when modern, well-reviewed standards are used and implemented correctly. Widely adopted algorithms and secure transport protocols are designed to resist practical decryption attempts without access to the key. However, encryption safety depends on proper configuration, secure key storage, timely software updates, and strong user authentication practices.
Many widely used encryption standards, including AES, were selected and standardized through processes led by the National Institute of Standards and Technology (NIST).
Most encryption standards offer a level of safety unmatched by other cybersecurity safeguards. Due to the technology’s incredible reliability, the AES 256 encryption standard is approved by the US National Security Agency (NSA). The overwhelming popularity of WhatsApp messenger, which since its creation in 2016 has delivered over 100 trillion encrypted messages, is another testament to the safety of encryption.
Definition
AES (Advanced Encryption Standard) is a widely used symmetric encryption algorithm adopted as a global standard. The “256” refers to key length, which increases resistance to brute-force attacks. AES is commonly used in file encryption, VPNs, and secure storage systems.
How to protect yourself where encryption doesn’t
Encryption protects data during storage and transmission, but many cyber threats target accounts, devices, and user behavior instead. A layered security approach, often called defense-in-depth, combines encryption with regular updates, strong passwords, multi-factor authentication, cautious link handling, and privacy controls. This reduces the likelihood of account compromise and malware-related exposure.
Data encryption is a powerful tool in your security mix, but it’s important that you do have a mix and other tools to keep you secure. Don’t rely solely on data encryption, or any single measure alone to keep your data protected.
To protect your data, update your Mac regularly, adopt strong passwords, enable 2FA, avoid suspicious links, and use a VPN. A reliable VPN hides your online identity and serves as a second layer of encryption. Make sure the VPN you choose has a high user rating and a solid track record of respecting user privacy. Avoid free VPN services, as they can collect and sell your data.
Note
A VPN encrypts traffic between your device and the VPN server. Once the traffic leaves the VPN server and travels to the destination website, its security depends on whether that website uses HTTPS and how securely it manages your data.
Conclusion
Encryption is a great way to protect your data, but it's not fool-proof and it can be hacked. That's why it's important to take your security into your own hands. Using a VPN adds an extra layer of protection, and Clario Anti Spy takes it further with tools like the Data breach monitor to help keep your online accounts safe.


