Table of contents
- What is bluesnarfing?
- Bluetooth vulnerability for bluesnarfing
- What does a bluesnarfing attack target
- Is bluesnarfing still a threat?
- Example of bluesnarfing attack
- How likely is your phone susceptible to bluesnarfing?
- Does cellular VPN protect from bluesnarfing?
- What’s the danger of bluesnarfing attacks?
- How to prevent bluesnarfing attacks
- Conclusion
What is bluesnarfing?
Bluesnarfing definition
Bluesnarfing is a type of cyberattack where a hacker gains access to your device via Bluetooth. In a bluesnarfing attack, a hacker detects your phone’s active Bluetooth connection and then targets a vulnerability that lets them hijack the connection.
Once they’ve cracked the Bluetooth connection, they can access any personal information on your device, including contacts, emails, text messages, and images. And worse, phones aren’t the only targets—bluesnarfing can affect laptops, tablets, and any other device that uses Bluetooth.
So, if you were wondering if Bluetooth can be hacked, the answer is yes.
Bluetooth vulnerability for bluesnarfing
Bluetooth-enabled devices, especially older ones, can have several vulnerabilities that let hackers gain access. After seeing that your device is “Discoverable,” the hacker will scan for weaknesses, including a lack of device authentication protections (like a PIN code), outdated software, and insecure data exchange protocols that let hackers bypass security measures.
What does a bluesnarfing attack target
Bluesnarfing attacks target the Object Exchange (OBEX) protocol. This is the transfer protocol that controls how Bluetooth-enabled devices share data. By hijacking the OBEX protocol, hackers can push applications onto your device or steal your data.
Is bluesnarfing still a threat?
Bluesnarfing is far less of a threat today than it was a few years ago. Device manufacturers have implemented stronger security measures, improved software, and enhanced authentication mechanisms to prevent bluesnarfing attacks from occurring. However, this doesn’t mean you should become complacent—bluesnarfing can still be a threat, especially to older devices.
Example of bluesnarfing attack
Here’s an example to illustrate how bluesnarfing works:
A hacker goes to a busy public location like a train station or coffee shop with a dense concentration of Bluetooth-enabled devices. These locations allow hackers to scan dozens (or hundreds) of devices while remaining inconspicuous.
After a short time, the hacker detects a discoverable Bluetooth connection. Then, they actively scan their victim’s Bluetooth connection for exploitable vulnerabilities. They find a vulnerability in the OBEX protocol using specialized software and gain access to their victim’s device.
Once connected, they steal the victim’s personal information and use it for personal gain. For example, they might steal sensitive photos and blackmail their victim into paying them not to share them publicly. Alternatively, they might gain access to the victim’s banking app and transfer money to their own account.
How likely is your phone susceptible to bluesnarfing?
Modern phones are much less susceptible to bluesnarfing since they have far stronger security measures in place. However, older devices are most vulnerable to hacking.
If your phone is a few years old and doesn’t have the latest security features, your phone might be susceptible. Likewise, your phone is more susceptible to bluesnarfing if you make it “Discoverable” to other Bluetooth-enabled devices.
Does cellular VPN protect from bluesnarfing?
No, a Virtual Private Network (VPN) will not protect you from bluesnarfing. A VPN secures and encrypts your internet connection rather than your Bluetooth connection. Since bluesnarfing targets your Bluetooth connection, a VPN can do nothing to protect you.
However, a VPN can help prevent hackers from intercepting your data when you’re connected to unsafe public Wi-Fi networks.
What’s the danger of bluesnarfing attacks?
Bluesnarfing attacks can pose several risks to you and your personal information, including:
- Theft of personal data. The primary goal of a bluesnarfing attack is to steal personal information and use it against you for personal gain.
- Identity fraud. With your personally identifiable information, scammers can take your identity and cause significant damage to your personal and financial life.
- Financial fraud. If the hacker gains access to your bank details, they can steal money or open accounts in your name.
- Blackmail. The hacker may find personal photos or other information and exploit these for blackmail or public embarrassment.
Clario AntiSpy can help protect you against bluesnarfing and other attacks with a step-by-step device security checklist. It will also scan your device for any spying threats and help you minimize any vulnerabilities so that you can keep your personal information private.
To use Clario Anti Spy:
- Download Clario AntiSpy and create an account
- Go to Spyware scan
- Select Run a deep scan
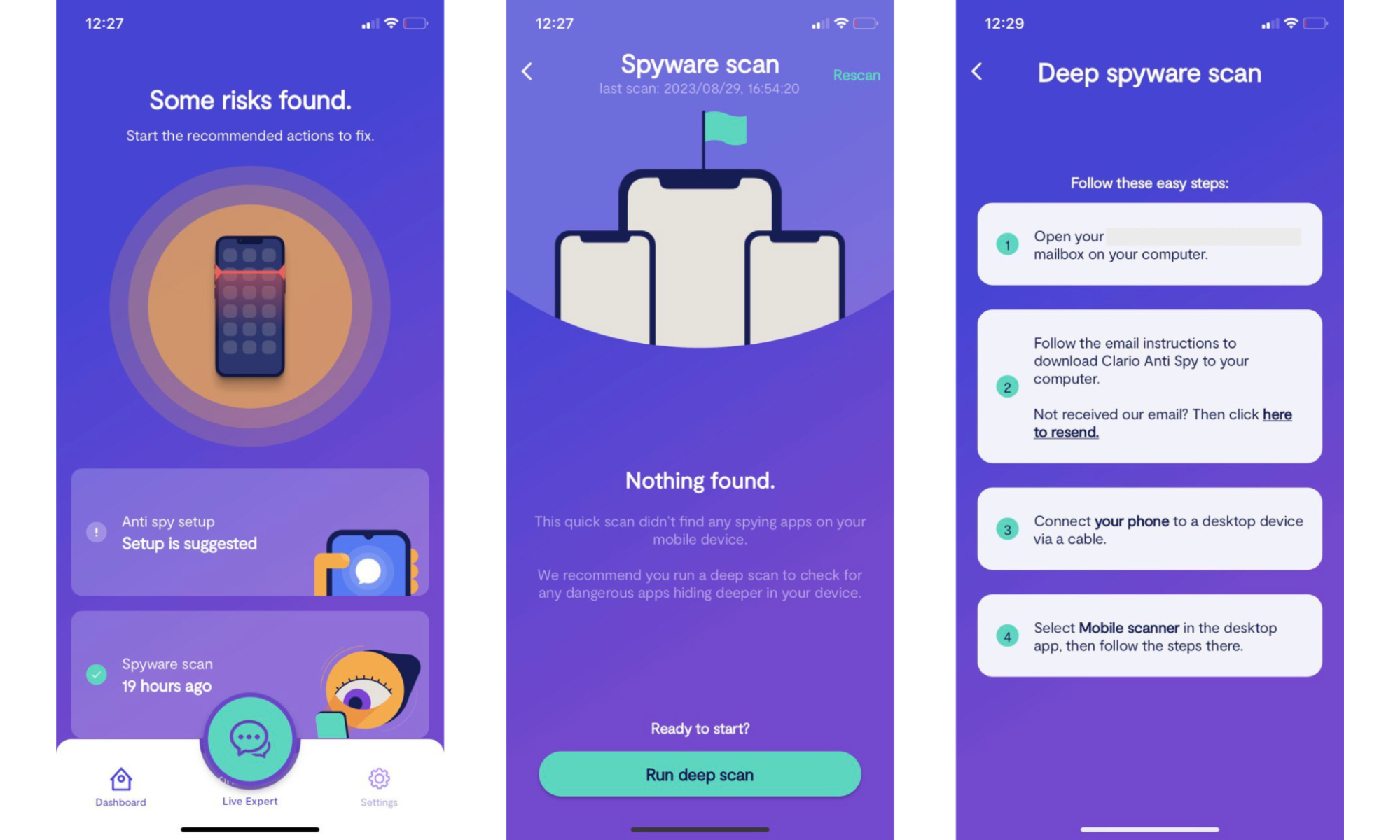
4. Follow the on-screen instructions to get rid of all vulnerabilities found by Clario AntiSpy.
How to prevent bluesnarfing attacks
To protect your Bluetooth-enabled devices from bluesnarfers, do the following:
- Keep your device updated. Make sure you regularly update your device’s operating system and apps. These updates often include security patches to protect you from the latest threats.
- Turn off Bluetooth when not in use. If you aren’t actively using Bluetooth, disable it. If you leave it enabled, you’re giving attackers more opportunities to target your device.
- Use strong device authentication measures. Set a strong, unique password on your device and use a PIN code to authenticate Bluetooth pairing. Also, use two-factor authentication (2FA) where possible to add another layer of protection.
- Turn on “invisible” mode. When you’re not actively pairing with another device, set your device to “non-discoverable” or “invisible” in the Bluetooth settings.
- Never pair with unknown devices. If you get a pairing request from a strange or unrecognized device, do not accept it.
- Limit which apps have Bluetooth permissions. Make sure that only vital apps have permission to access your Bluetooth connections.
More info
Think you’ve fallen victim to a hacker? Find out what to do if your computer is hacked and what codes to check if your phone is hacked.
Conclusion
Even though bluesnarfing attacks are becoming less common, they still pose a significant threat to your privacy. These attacks can lead to hackers stealing your personal data, taking your identity, and blackmailing you for financial gain. To protect yourself, follow the tips above and never accept unknown Bluetooth pairing requests.


