Table of contents
- Telltale signs your computer has been hacked
- What to do if your computer has been hacked
- 1. Reset your passwords
- 2. Log out of all online accounts
- 3. Disconnect from the internet
- 4. Remove external hard drives
- 5. Scan your computer for malware and viruses
- 6. Wipe your hard drive (if necessary)
- 7. Spread the word
- 8. Closely monitor your credit and financial accounts
- 9. Install security software
- How to avoid being targeted by computer hackers again
- Step 1: Read up on how to detect online scams
- Step 2: Maintain strong passwords
- Step 3: Use VPN at all times
- Step 4: Keep files backed up
- Step 5: Ensure your firewall is properly configured
- Step 6: Don’t leave your devices unattended in public
- Reasons why you were hacked in the first place
Telltale signs your computer has been hacked
You might recognize suspicious events when you see them, a general sign that something’s not right and your computer or internet browsing is not operating as it should.
More specifically, you might have been hacked if:
- Google searches redirect you to sites you didn’t intend to visit.
- There’s been an installation of an app that you’re unfamiliar with.
- You’re seeing suspicious pop-up ads, such as fake antivirus warnings. (Please do not click on these, by the way!)
- People on your email contact lists receive social media invites you didn’t send.
- Your computer slows down or freezes.
- You notice rogue, third-party activity ranging from the minimal (keyboard strokes, your mouse moving) to the very big (money taken from your online bank or credit card account).
- There’s an email sent from your account that you have no recollection of sending.
- You have new suspicious programs installed on your computer.
- Your web browser layout looks different.
Once you’ve noticed these signs, rush to follow the steps Clario experts have collected for you.
What to do if your computer has been hacked
Breathe in, breathe out. Nothing harmful may have happened yet. You can mitigate anything bad that has happened.
Here’s what to do if your computer is hacked.
1. Reset your passwords
This might seem difficult at first – you have a lot of passwords after all. But focus on the key places; social networks (Facebook, Twitter, Instagram), emails, devices (phone, laptop, and so on), and anywhere involving credit cards and finance (shopping, banking).
Pro Tip
Use a password manager to generate complex, unique passwords for every account. Enabling two-factor authentication (2FA) can provide an additional layer of security.
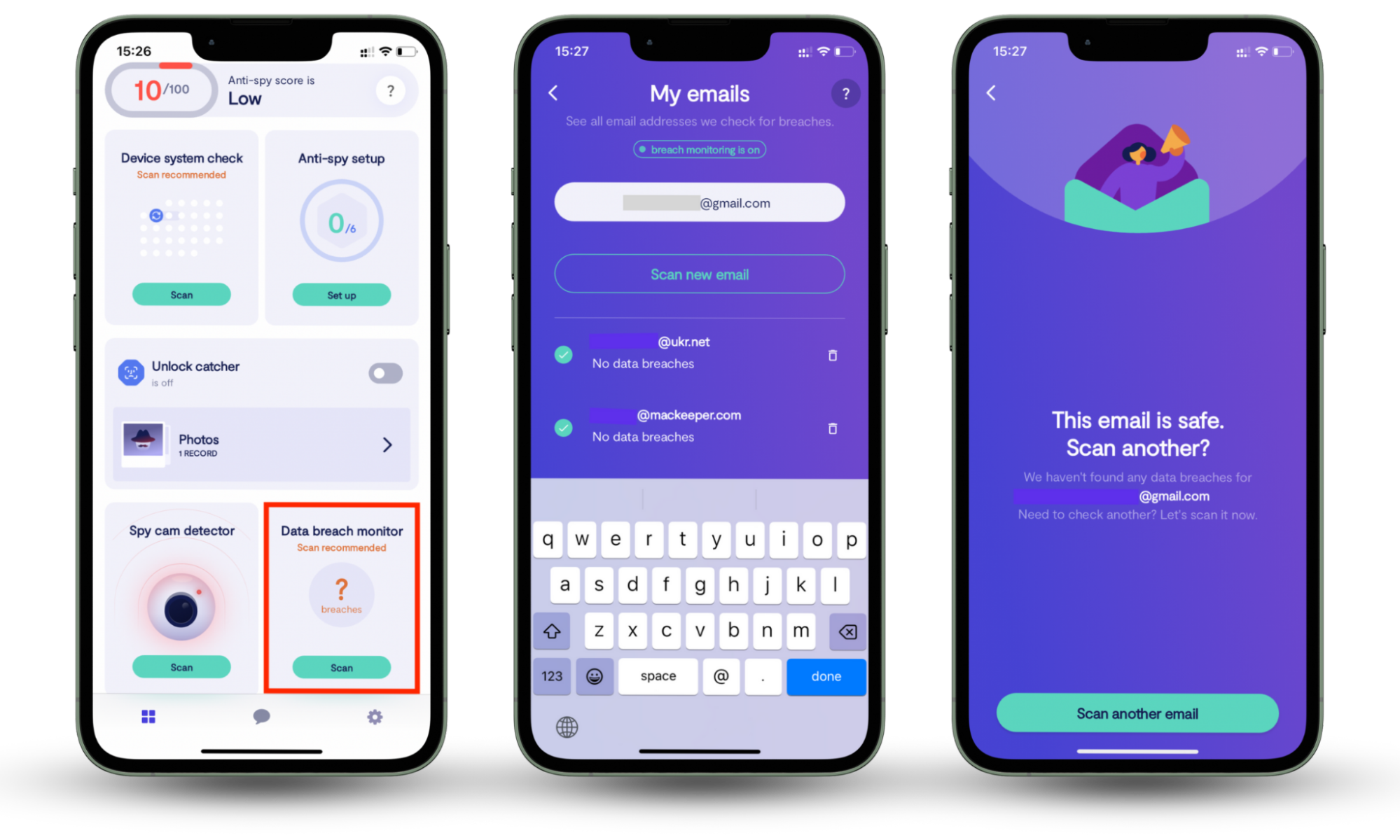
The best way to start is by checking for any data leaks. Use Clario Anti Spy to run the data breach monitor. Scan your email address, and it will show if your account details have been exposed to a breach. It will show you if any website has compromised your personal data: Social Security Number, bank credentials, emails, phone number, etc. If the data break monitor detects a leak, change the password on the corresponding websites and apps first.
Follow these steps to launch the Data breach monitor on Clario Anti Spy:
- Download Clario Anti Spy on your device and create an account.
- Go to Data breach monitor on the dashboard.
- Add the email you want to check and tap Scan.
- Review any breaches found and follow the different recommendations to secure your accounts.
2. Log out of all online accounts
After you’ve reset passwords, log out. It’s easy to forget that we tend to have our social media (and other online accounts) set to log us in automatically.
3. Disconnect from the internet
Next, shut down your connection to the internet: that means turning off Wi-Fi on your computer and switching phones and tablets to airplane mode.
After you follow the next steps and you are ready to connect to the Wi-Fi again, make sure you use VPN to encrypt your data and avoid falling victim to a hacker’s trap again.
For more on safe browsing, check out our guide to malware.
4. Remove external hard drives
Remove any external drives. This means USB sticks or other external hard drives. Be sure to “eject” them first. (Go to the appropriate folder, then click “eject”).
If you’re certain you’ve been hacked, you might want to remove the computer’s hard drive too. Back up any files you have (you can even save them to the cloud, like Google Drive, or email small files to yourself); switch off all power sources.
Once the computer is shut down, you can remove the hard drive (the big black rectangle within your laptop). Its location will vary depending on the make or model. If you are not certain what to do, consult Clario tech support. It’s easy to reach — just click the message icon in the upper right corner to connect to the agent. Professional support engineers are available 24/7 to help you.
5. Scan your computer for malware and viruses
Your device’s security software or a trusted third-party tool can help detect and remove malicious files. Frequent scans ensure malware doesn’t compromise your system or personal data.
While scanning your computer is essential, don’t forget about your smartphone.
Hackers often target phones to access sensitive information. Clario Anti Spy complements your computer’s security by helping you detect suspicious apps, secure your accounts, and protect against spying threats.
For more information on running a scan, check out our guide to getting rid of viruses.
6. Wipe your hard drive (if necessary)
If your scan reveals a virus or hack, you can (and probably should) wipe your hard drive, then reinstall your OS. Wiping means to erase permanently, so be aware that whatever you’re deleting will be gone for good unless you back it up.
Do not just manually delete files: they’ll still exist somewhere on your hard drive. Instead, use a downloadable program to carry out the wipe. Like a virus scan, a wipe will let you know when it’s been carried out completely.
7. Spread the word
Unfortunately, your hack might have affected people in your contact list: friends and families might have been emailed by a hacker posing as you. If that happens, it’s important to contact those who have been emailed or texted to let them know you weren’t behind the message and that you may have been hacked.
And if your hack was the result of clicking on a suspicious email or attachment, it’s a good idea to warn others of the attack. Similar hacks tend to happen in waves, as multiple victims are contacted at a time.
8. Closely monitor your credit and financial accounts
After the hack, keep an eye on your online expenditures, regularly checking your bank and credit card accounts.
9. Install security software
Naturally, up-to-date, reputable security software is the best line of defense against a future hack.
How to avoid being targeted by computer hackers again
Anyone can fall victim to a hack, but there are ways to minimize the risk.
Step 1: Read up on how to detect online scams
Sadly, hackers are always looking for ways to breach security. It’s a good idea to keep on top of unwelcome trends related to hacking, phishing, and other forms of attack.
Step 2: Maintain strong passwords
Remember to keep strong passwords and to change them regularly. Include a combination of numbers, letters, and punctuation, and try to use different passwords for your various online accounts.
Step 3: Use VPN at all times
It doesn’t matter if you’re using your home Wi-Fi network or browsing the internet at the cafe – once you’re connected to the internet, you are transmitting data to the network. A hacker can hijack your session at any time. Thus, to protect your personal information from being stolen, encrypt it with a VPN.
Step 4: Keep files backed up
It’s good practice to maintain important or sensitive files beyond your computer, ideally in multiple places, USB, external hard drives, cloud storage, or if you’re feeling especially cautious, all of the above.
Step 5: Ensure your firewall is properly configured
You should have a firewall installed on your computer. A firewall in a building is a sealed wall that prevents the spread of fire. On your computer, it works the same way.
You can configure your firewall to block communication between your computer server and another. This firewall block could filter based on suspicious IP addresses (other specific servers), potentially dangerous phrases, or even a website.
Step 6: Don’t leave your devices unattended in public
Even two minutes is time enough for a hacker to gain personal information or sow the seeds for a later hack.
Reasons why you were hacked in the first place
Hackers, like any criminals, are opportunists. Just like a shop window left open or a bag left unattended, some online activities leave you vulnerable to hacks.
For safer browsing, you should:
- Avoid opening suspicious email attachments.
- Make sure your operating system (OS) is up to date: you’ll be regularly informed of updates on your phone or computer. Don’t put off installing these updates, as they help keep your device’s security current.
- Use strong passwords, including numbers, letters, and punctuation – and not your mother’s maiden name! (We have a guide to creating more secure passwords if you’d like to know more.)
And lastly, consider how you’ve protected your phone. If you haven’t installed a reliable anti-spy app, your device could be an easy target for hackers. A good anti-spy app like Clario Anti Spy can help secure your smartphone by detecting apps with suspicious permissions and keeping your personal data safe.
Don’t wait to strengthen your defenses; install Clario Anti Spy today.


