Table of contents
- What Is a Rootkit: Definition & Meaning
- How does a rootkit work?
- Danger of rootkit
- How can I detect a rootkit?
- Blue screen
- Slow device performance
- Windows settings change without permission
- Unusual web browser behavior
- Web pages don't function properly
- New files or programs
- Rootkit types
- User-Mode Rootkits
- Firmware rootkits
- Kernel-mode rootkits
- Memory rootkits
- Bootkits
- Virtual rootkits
- Application rootkits
- Rootkit removal: how to get rid of rootkits on your computer?
- How to remove a rootkit from Windows
- How to remove a rootkit from Mac
- Rootkit examples
- How to prevent rootkit attacks?
- Update your devices in time
- Be aware of phishing emails
- Download only secure files
- Use anti-rootkit software
What Is a Rootkit: Definition & Meaning
If you are not familiar with what a rootkit is, then this expert guide will give you all the knowledge you need about rootkit malware and rootkit removal. A rootkit is a software bundle designed with malicious intent by a hacker to infiltrate your device and grant unauthorized remote access to the controller of the rootkit. These are incredibly hard to detect once they infect your system as the rootkit will conceal its presence within your infected operating system.
How does a rootkit work?
When a rootkit is installed into your system, it uses your computer as a host, and the virus takes over full control of your computer. The hacker in control of the rootkit is granted full remote access to your device. This access can allow them to disguise the malicious files as legitimate files, as they have privileged access to your system files and processes.
Danger of rootkit
As mentioned above, the biggest danger of a rootkit is the privileged access granted to the hacker controlling it. The hacker has full access to your system files and processes, meaning they can disguise the malicious files into your device and download more malicious malware onto your device, such as ransomware, etc.
Not only can the controller of the rootkit infect your device with more sophisticated malware once they have control, but they can disguise these malware files so carefully that they can even beat your antivirus software’s virus scans.
How can I detect a rootkit?
Now you know what a rootkit is and how dangerous it can be. It’s time to teach you what signs to look out for that may indicate if you have been infected with one.
Blue screen
You’ve all heard the harrowing tales of the “blue screen of death.” It’s never a good sign if your computer presents you with a blue screen with white warning text, as this typically means there is an error deep within your processors, which is preventing your PC from being able to startup.
Slow device performance
Your device may suffer from extreme input delay or frequent freezing as you try to use it. If it isn’t detecting your keystrokes or mouse movement, this can be another indication you have a rootkit.
Windows settings change without permission
If you haven’t changed any of your windows settings but are noticing unusual changes to your desktop screen, then you might have a rootkit. Changes to your screensaver, date and time, or taskbar are all signs that someone may be in control of a rootkit on your device.
Unusual web browser behavior
If you are noticing unusual bookmarks you don’t recall making or link redirects, then there is a good chance someone has altered your web browser settings with a rootkit.
Web pages don't function properly
If you have excessive network traffic being sent from your device, it will stop your web pages from functioning properly. If you are noticing significant delays on web pages and content failing to load, then there may be a more deep-rooted reason behind these delays.
New files or programs
Keep a close eye on your desktop as if new files and programs begin appearing on your home screen, then you might have someone else installing these files. Removal of files may also be something to look out for as hackers will likely try to remove your current antivirus programs from your system to stop you from detecting their rootkit before they have got what they want from your device.
Rootkit types
Rootkits, like many other types of malware, can be sorted into different types of rootkits depending on where they infect your machine and how severe their effects are. Take a look at the list below and become an expert at identifying the different types of rootkits.
User-Mode Rootkits
A user-mode rootkit infects your operating system’s administrative controller account, giving the hacker full access to change your computer’s security settings. These rootkits are hard to identify as the hacker can conceal the malware deep within the device’s system due to its administrative privileges.
A simple reboot isn’t enough to remove this rootkit. Instead, you’ll need to use deep-scanning antimalware software such as Clario to detect rootkits inside your system files.
Firmware rootkits
A firmware rootkit, or hardware rootkit, is malicious software that targets and takes control of computer hardware. Some of these rootkits are known to hide inside firmware when your device is switched off and reinstall itself once you turn it back on.
These can be notoriously difficult to remove from your device due to their bounce-back nature. It isn’t enough to simply detect and remove this rootkit with a scanner, as it will reinstall itself when you reboot your system.
Kernel-mode rootkits
Hackers created kernel-mode rootkits to counter the creation of kernel-level rootkit scanners. A kernel-mode rootkit lives on the same level as an operating system which, in turn, compromises your entire operating system.
Kernel-mode rootkits taint every level of your computer and can even compromise the results of rootkit scanners results. This can make them notoriously difficult to remove from your device, but they are easy enough to spot as kernel-mode rootkits struggle to operate without causing system crashes and other faults on your device.
Memory rootkits
A memory rootkit is often perceived as the least threatening due to its short time frame. They do not install permanent code onto your device as they infect your random-access memory, or RAM, meaning a simple reboot of your system will make them disappear. However, don’t underestimate the amount of damage that can be done to your system in the time that they are functioning.
Bootkits
A bootkit or a bootloader rootkit is a kernel-mode rootkit variant that targets and infects your Master Boot Record (MBR). The MBR is the record that your computer consults on when booting up its operating system. If you have a bootkit, then anytime you turn on your device and it refers to the MBR, it will also activate the bootkit.
While your rootkit scanners won’t be able to detect a bootkit as it doesn’t reside in your operating system, both Windows 8 and Windows 10 have successfully eradicated their danger with the addition of the Secure Boot feature.
Virtual rootkits
A virtual rootkit will load itself under the operating system before placing the operating system onto a virtual machine. They run separately from the computer’s operating system, which makes them very hard to find when performing a malware scan.
Application rootkits
An application rootkit will replace the files of common applications on your computer, such as Microsoft Word, Paint, or Spotify. Each time you run the infected program, you grant access to the hacker to begin prying your data and controlling your device.
An application rootkit is hard to detect without a malware scan as these compromised applications will still work as normal, but running a malware scan will pick up these infections.
Rootkit removal: how to get rid of rootkits on your computer?
Rootkits are complex and thus can require some specialized tools to get rid of them from your computer. Sometimes if the infection is too deep, you may have to start from scratch, erase your computer’s operating system and rebuild from the beginning.
How to remove a rootkit from Windows
Typically, removing a rootkit on Windows will involve using a scanner. Once the rootkit is detected by your malware scanner, your antivirus software will be able to remove the rootkit. More sophisticated rootkits infect you on a deeper level and may require you to reinstall Windows or have a professional repair to complete your rootkit removal on Windows 10. If, after having your PC repaired, you still have a rootkit, then it may be time for you to replace the PC altogether.
How to remove a rootkit from Mac
Mac doesn’t just add new features when they release updates to their operating systems, so make sure you keep your computer up-to-date, and you’ll benefit from their latest antivirus software. When Apple updates its systems, they also remove any malware on your device, such as rootkits. While there aren’t any specific rootkit scanners available for Mac, should you suspect you have one, simply reinstall macOS, and it will remove most apps and rootkits that might have infected your device.
If you still suspect you have a rootkit on your device after reinstalling macOS, then you may need to have your Mac professionally repaired or even buy a new device.
Rootkit examples
Whenever a new rootkit is discovered, it shakes up the cybersecurity space and becomes the focus of attention. Rootkits are known for being extremely dangerous in the wrong hands, here are some of the more well-known rootkits that were discovered in the past 30 years.
The first known rootkit. In the year 1990, Steven Dake and Lane Davis created the first known rootkit in history at Sun Microsystems.
NTRootkit. In 1999, Greg Hoglund released an article about the creation of a Trojan called NTRootkit. The first known rootkit was designed to work on Windows, which also operated in kernel mode.
HackerDefender. In the year 2003, Windows 2000 and Windows XP were rocked by the arrival of HackerDefender, a user-mode rootkit that then led to the creation of RootkitRevealer.
Greek Watergate. In 2004, 100 mobile phones on the Vodafone network in Greece (including the phone of the then prime minister) were infected by a rootkit. This scandal would become known as Greek Watergate.
Anti-piracy rootkit. In the year 2005, a huge scandal broke, which saw Sony BMG installing rootkits onto users’ devices without their consent through the form of an Anti-piracy tool CD.
TDL-1. In 2008, TDL-1, which is now known as the TDL-4 bootkit, powered the Alureon Trojan onto people’s devices which created a series of infected devices under one botnet.
Machiavelli. In the year 2009, Mac OS X was targeted by the Machiavelli rootkit, demonstrating that Macs are also vulnerable to dangerous malware.
Stuxnet worm. In 2010, the US and Israel allegedly co-created the Stuxnet worm and used a rootkit to conceal its presence when spying on Iran’s nuclear program.
Flame. In the year 2012, a mammoth modular malware named Flame dropped and caused enormous disruptions across the middle east and north African networks. Most malware clocks in under 1MB, however, Flame’s size exceeds 20MB.
Lojax. In 2018, the first rootkit was launched that infected a computer’s UEFI (Unified Extensible Firmware Interface), otherwise known as the firmware which controls the motherboard. The rootkit named LoJax was able to survive the operating system reinstallation, which made it extremely troublesome.
Scranos. In 2019, one of the more notorious attacks in recent years saw the Scranos rootkit, which stole the passwords and payment details stored in your browser. Your PC was then turned into a click farm to secretly generate video revenue and YouTube subscribers for the hacker.
How to prevent rootkit attacks?
So now you know exactly what a rootkit is and what it does. The only thing left to learn is how to prevent becoming a victim of a rootkit attack. Rootkits, especially the more sophisticated ones, can be tricky to identify once they are installed onto your system, so follow this advice and prevent yourself from getting one in the first place.
Update your devices in time
As long and annoying as system updates can be, they are there for a reason. Often they contain updates to your PC's defense systems against dangerous and modern malware, including rootkits. The sooner you stay updated, the less chance you have of becoming a victim of the latest rootkit technology.
Be aware of phishing emails
Like most types of malware, a simple phishing email is the easiest way for a hacker to gain access to your device and infect your PC. Always stay alert when using your web browser and make sure you don’t fall for a phishing email, as tempting as that brand new iPhone sounds that you have just won, if it sounds too good to be true, it usually is.
Download only secure files
If you don’t know the sender of a downloadable file, it’s probably not a good idea to download it. Only download secure files from trusted websites and avoid third-party websites that claim they can give you cracked versions of applications or programs, as these often contain compromised files and malicious malware within.
Use anti-rootkit software
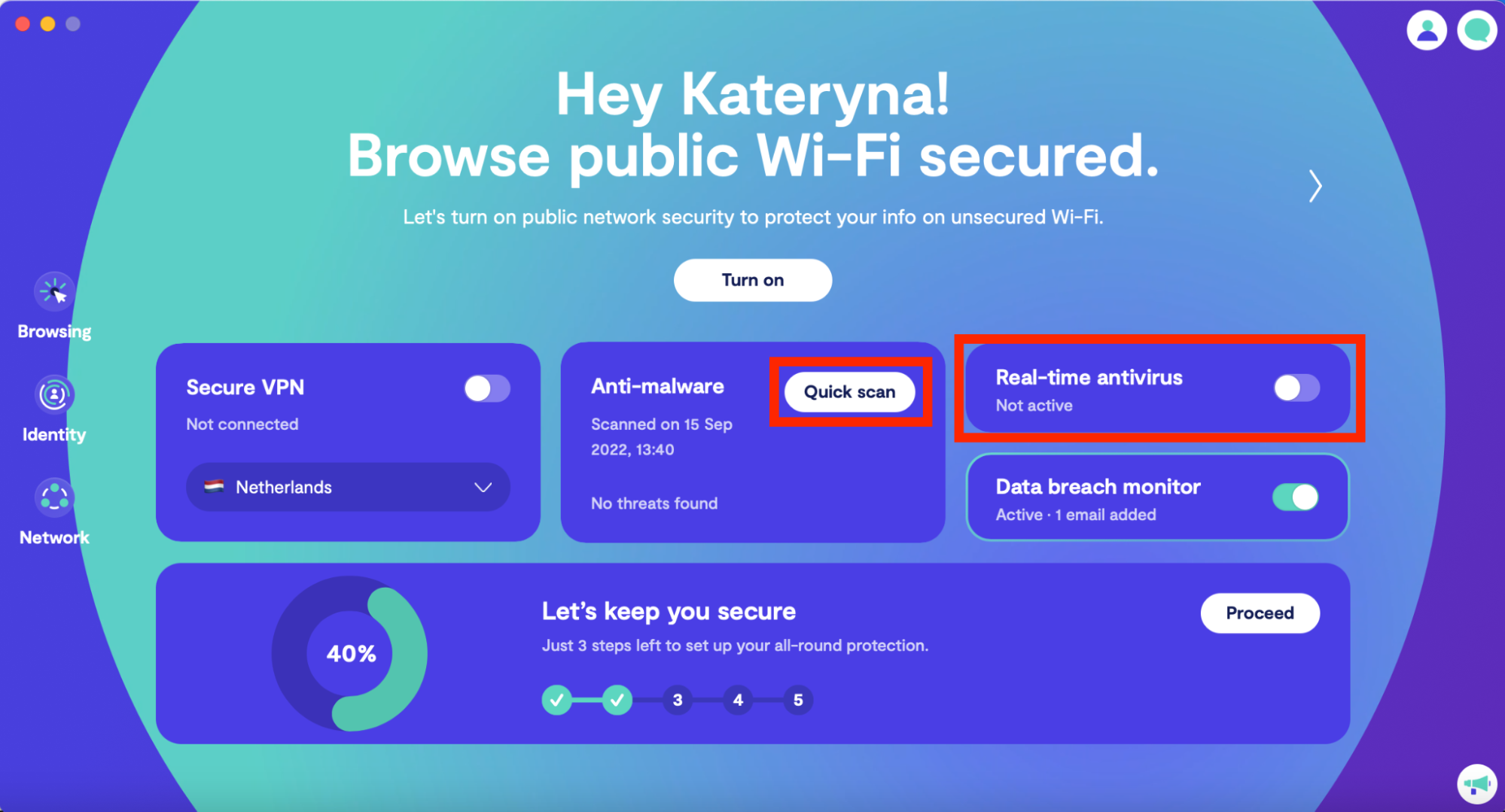
A good anti-malware software, like Clario Antivirus, will help keep you protected from the malicious threats of malware such as rootkits. The best offense is a good defense, and this applies to defending your sensitive data from being stolen.
Clario Antivirus is quick and easy to install and will be your first line of defense when encountering malicious files, links, and websites online. You can use the on-demand scans to detect if you have a rootkit on your system, as well as benefit from the daily security scan used to check newly installed applications haven’t compromised your device.
Not only does Clario’s Antivirus keep malware off your device, but its jailbreak checker will check if your device has become rooted and stop strangers from gaining full access to your operating system. Try Clario now.


