Table of contents
- Brute Force Attack Definition
- Types & methods of brute force attacks
- Simple brute force attacks
- Dictionary attacks
- Hybrid brute force attacks
- Reverse brute force attacks
- Credential stuffing
- Brute force attack prevention
- Use a strong, unique passwords
- Enable two-factor authentication
- Use a password manager
- Be aware of phishing scams
- Avoid connecting to unsafe Wi-Fi
- Monitor your personal info for breaches
- Keep yourself safe from brute force attacks
- Conclusion
Brute Force Attack Definition
A brute force attack is a type of cyberattack wherein a hacker uses an automated program to guess the password or personal identification number (PIN) of a victim's account. Hackers often use this method when they have obtained a list of usernames or email addresses but don't have the corresponding passwords.
Brute force attacks work by systematically attempting login combinations until the correct credentials are found. These attacks typically target user accounts, admin panels, and encrypted systems. While simple in concept, modern brute force attacks are highly automated and can execute millions of attempts in a short time, increasing the likelihood of unauthorized access.
How brute force attacks work:
- The attacker selects a target (e.g., login page or account)
- An automated tool generates password combinations
- The system tests thousands or millions of attempts rapidly
- If a correct match is found, access is granted
In simple words, an attacker targets an email account login page and uses a script to test thousands of common passwords against a known email address until the correct password is found.
Important to know
Brute force attacks are significantly less effective against systems that use protections like rate limiting, CAPTCHA verification, or temporary account lockouts after repeated failed login attempts.
Types & methods of brute force attacks
Brute force attacks can take several forms depending on how attackers generate or obtain login credentials. Some methods rely on guessing passwords systematically, while others use precompiled wordlists or stolen data from breaches. Understanding these variations helps identify how attacks work and which defenses are most effective against each type.
In addition, brute force attacks aren’t just used to crack passwords. They can also be used to discover hidden pages and content on websites (i.e. directories and files that have not been linked to from the main website).
While previously, hackers would need to guess your passwords manually, these days brute force attacks are automated. This means that hackers can try thousands–or even millions–of log-in combinations until they find the right one.
Signs of a brute force attack:
- Multiple failed login attempts in a short period
- Login attempts from unfamiliar or changing IP addresses
- Account lockouts or security alerts
- Unusual login activity from different locations
Common types of brute force attacks differ in approach:
- Simple brute force: tests random or common password combinations
- Dictionary attacks: use predefined wordlists of likely passwords
- Hybrid attacks: combine wordlists with variations (e.g., numbers, symbols)
- Reverse brute force: tests one password across many accounts
- Credential stuffing: uses leaked username-password pairs from data breaches
Different brute force attack methods vary in how they are executed, when they are used, and how effective they are depending on password strength and system protections.
| Attack type | When it’s used | Example | Limitation |
| Simple brute force | When attackers have no prior knowledge and rely on guessing passwords | Testing thousands of random password combinations on a login page | Ineffective against strong passwords or systems with login attempt limits |
| Dictionary attacks | When targeting users likely to use common or predictable passwords | Trying passwords like “password123” or “qwerty” | Blocked by modern password policies and banned password lists |
| Hybrid attacks | When attempting to bypass password complexity rules with variations | Trying combinations like “Summer2024!” or “Password1” | Less effective against strong password requirements and detection systems |
| Reverse brute force | When a common password is tested across many accounts | Testing “123456” against multiple usernames | Fails if users use unique passwords or if suspicious activity is detected |
| Credential stuffing | When attackers use leaked credentials from previous data breaches | Using stolen login data to access accounts on other platforms | Ineffective if passwords are unique or multi-factor authentication is used |
Simple brute force attacks
A simple brute force attack is a trial-and-error method used by hackers to obtain information such as a user password or personal identification number (PIN). Oftentimes, simple brute force attacks work by targeting a specific login page and then trying to guess the username and password using lists of common passwords.
Dictionary attacks
A dictionary brute force attack is one of the most common types of brute force attacks involving a list of common words to guess a password. While this might sound like an easy task for a hacker, it can actually be quite difficult. Unlike before, most sites now have measures in place to prevent these kinds of attacks, such as requiring a minimum number of characters or banning common words.
Hybrid brute force attacks
Through a hybrid brute force attack, hackers combine a simple brute force attack with a dictionary attack by trying various combinations of passwords with the most commonly used words in mind. By combining these two methods, the hacker has a much higher chance of success.
Reverse brute force attacks
A reverse brute force attack is when an attacker takes a list of common passwords and tries them all against a single account. The goal is to eventually find the correct password for that account. This type of attack can be very successful if the attacker has a large list of common passwords.
Credential stuffing
Credential stuffing is a type of brute force attack where hackers use lists of stolen usernames and passwords to gain access to your accounts. These lists are usually obtained through data breaches at other companies. Hackers will use automated tools to try these stolen credentials on your accounts until they find a match.
Different types of brute force attacks are used in specific scenarios depending on what information the attacker already has and how they attempt to generate or obtain passwords.
Brute force attack prevention
Brute force attacks are prevented by combining strong authentication practices with system-level protections that limit repeated login attempts. Effective defenses include using complex, unique passwords, enabling multi-factor authentication, and implementing safeguards like rate limiting and CAPTCHA to block automated attack tools.
The most effective ways to prevent brute force attacks include using strong passwords, enabling multi-factor authentication, limiting login attempts, and monitoring for suspicious activity. These measures reduce the chances of attackers successfully guessing or reusing credentials.
Here are some ways how to prevent brute force attacks:
- Use a strong, unique password for each of your online accounts
- Enable two-factor authentication
- Use a password manager
- Be aware of phishing scams
- Monitor your personal info for breaches
Different prevention methods protect against brute force attacks in different ways, and their effectiveness depends on how they are implemented and combined.
| Method | How it helps | Example | Limitation |
| Strong, unique passwords | Makes it harder for attackers to guess credentials | Using a password like “T9!kL2#vP8@z” instead of “password123” | Can still be compromised if reused across multiple accounts |
| Two-factor authentication | Adds an extra verification layer beyond the password | Using authenticator apps, SMS codes, or security keys | Does not protect against phishing if users share verification codes |
| Password manager | Generates and stores complex passwords securely | Storing all credentials behind one master password | Risk if the master password is weak or exposed |
| Phishing awareness | Prevents attackers from obtaining credentials directly from users | Identifying fake login pages or suspicious emails | Sophisticated phishing attacks can still deceive users |
| Avoid unsafe Wi-Fi | Reduces risk of intercepted data on unsecured networks | Avoid logging into accounts on public Wi-Fi | Encryption helps but does not eliminate all network-based threats |
Use a strong, unique passwords
When it comes to keeping yourself safe online, a tried-and-tested internet safety rule is to make an effort to create strong, unique passwords. To create a strong password, it’s best to use a combination of letters, numbers, and symbols.
In addition, it’s also recommended to avoid using common words, repeating the same password across multiple accounts, or sharing your passwords with other people. These days, many websites have tools to help determine whether a password is weak or strong. So, it’s best to try different combinations until you find one that fits the bill.
Enable two-factor authentication
Through two-factor authentication (2FA), you can include an additional layer of protection in the event of a hack. There are several types of two-factor authentication, which include one-time pin codes to be sent to your email or mobile number and authentication apps.
With two-factor authentication enabled, you can be sure that even if a hacker can crack your password, they will not have automatic permission to access your account. Aside from email addresses, you should also make sure that all accounts which allow for 2FA are enabled, including social media accounts.
Use a password manager
After creating a strong password, the next challenge is to remember it. Because strong passwords often mean a combination of difficult to remember strings of letters and numbers, it can be a hassle to keep all of them in check.
Using a password manager, you can make sure that your passwords are always within reach. With this, you’ll be incentivized to keep creating strong passwords without having to memorize all of them.
Be aware of phishing scams
Aside from creating and keeping strong passwords, the next thing you should do is to make sure they stay safe. Unfortunately, the internet is rife with phishing scams, wherein hackers try to get your exact password directly from you.
In some cases, hackers create convincing emails, landing pages, and apps, which they use to confuse unsuspecting users. By accidentally filling up these copies, you can serve your passwords on a plate to hackers. To prevent this, make sure that you always check if you’re on the right website, or you’ve downloaded the right app before logging into your account.
Avoid connecting to unsafe Wi-Fi
One of the most common ways wherein hackers access your data is through unsafe public or home Wi-Fi. Using unsafe internet connections, hackers can gather a wealth of information, which can help their automated bots guess your passwords more effectively.
For example, having access to your device through public Wi-Fi helps hackers identify what websites or apps you normally use. It also helps them learn things like your full name, mobile number, pet names, and other information. Thankfully, there are many things you can do to make your home Wi-Fi more secure.
Monitor your personal info for breaches
While you can be as careful as possible, there is always a chance that a company that you’ve trusted with your data exposes it. As more aspects of our lives go online, data breaches are only going to become more common.
To prevent any issues from leaked personal information, it’s best to monitor your email addresses for any breaches or invest in apps which can do them for you. This is where Clario comes in — check your emails for data breaches and take action as soon as possible to protect your digital privacy.
Keep yourself safe from brute force attacks
Staying safe from brute force attacks requires a combination of strong password practices, multi-layered authentication, and ongoing monitoring for compromised data. While no single solution guarantees complete protection, using multiple security measures together significantly reduces the risk of unauthorized access.
Unfortunately, brute force attacks are becoming more common as lists of stolen log-in credentials are readily available on the dark web. With technology becoming more advanced, the programs which enable hackers to perform brute force attacks also become more sophisticated.
Knowing all this, it makes sense to not only be mindful of how brute force attacks work but also know the different ways you can prevent it from happening. Aside from this, it also makes sense to invest in more advanced technology for your peace of mind.
What to do if your account may be compromised:
- Change your password immediately
- Enable or update multi-factor authentication
- Check your email for breach exposure
- Log out of active sessions on all devices
- Monitor accounts for unusual activity
Monitoring your personal data for exposure is a critical step in preventing account takeovers, especially when login credentials may already be circulating in data breaches.
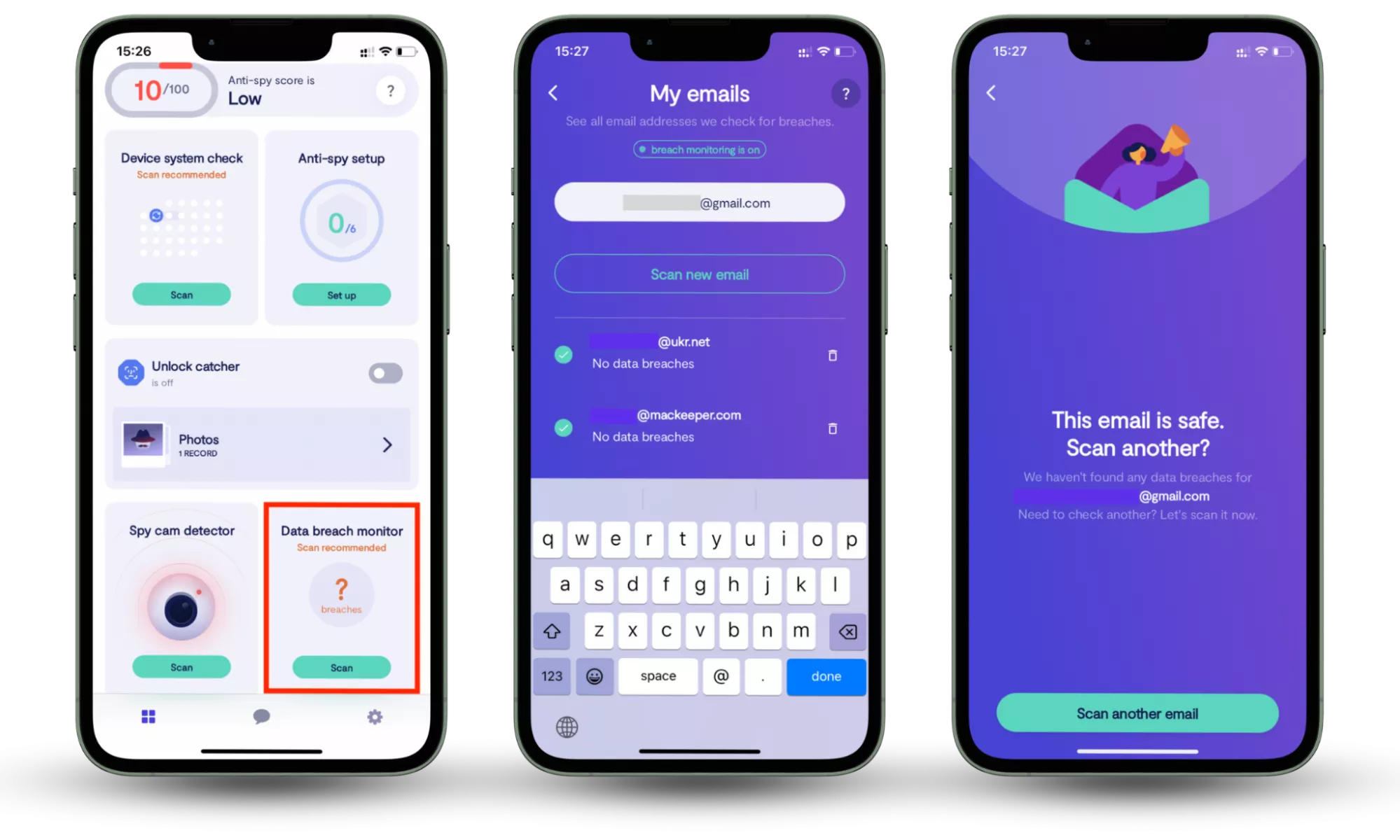
Clario Anti Spy includes a Data breach monitor that scans your email addresses against known data leaks to identify whether your personal information has been exposed. It helps detect compromised accounts early and alerts you if your credentials appear in breach databases, reducing the risk of unauthorized access and credential-based attacks.
Data breach monitor works by scanning your email for known breaches, showing which accounts may be affected, and allowing you to take action by securing them outside the app. You can track resolved issues, add additional email addresses for monitoring, and rely on continuous 24/7 monitoring to detect new exposures. However, it’s important to note that only publicly known breaches can be detected, meaning some newly leaked data may not appear immediately.
How to check whether your information is compromised:
- Download Clario Anti Spy.
- Open the app, and, under Data breach monitor, tap Scan.
- Enter your email address.
- When the scan is complete, follow the on-screen guidance to review any data breaches.
- Repeat the process for any other email addresses.
Conclusion
Brute force attacks rely on weak or exposed credentials, making strong passwords, multi-factor authentication, and proactive monitoring essential for protecting your accounts. While no method guarantees complete security, combining these measures significantly reduces your risk of unauthorized access.
To stay protected, it’s important to not only secure your accounts but also monitor your data for potential breaches. With Clario Anti Spy, you can detect compromised credentials early and take action before they are misused, helping you maintain control over your digital privacy.


