Table of contents
- What percentage of cyberattacks are phishing?
- Recent phishing attempts are more convincing
- Phishing email statistics
- How many phishing emails are sent daily?
- Common email phishing attacks to look out for
- Malicious attachments to avoid
- Website phishing statistics
- Top brands exploited by phishing scams
- Cost of phishing attacks
- Data breach statistics
- Phishing trends
- 4 tips to protect against phishing for businesses
- 1. Open emails with caution
- 2. Use two-factor authentication
- 3. Phishing cybersecurity software
- 4. Educate your employees
- Conclusion
Phishing attacks are a regular occurrence in 2026, but some phishing email scams are easier to detect than others. While you probably know that you shouldn’t respond to an email claiming “You’ve Won a Free iPad,” many fraudulent emails are more cunning with their approach.
Phishing is a form of cyberattack that uses deception and social engineering to trick individuals into revealing sensitive information such as login credentials, financial data, or internal company access. These attacks commonly occur through email, fake websites, or messaging platforms and often impersonate trusted entities.
Understanding phishing statistics provides critical insight into how frequently these attacks occur, how they evolve, and why they remain one of the most successful cybersecurity threats. This context helps individuals and businesses better assess risk and implement more effective prevention strategies.
After analyzing phishing statistics, we discovered just how effective fraudulent emails could be.
For example, in 2019 a cybercriminal successfully executed a spear phishing campaign that swindled employees from Google and Facebook into paying over $100 million in fraudulent invoices.
In 2017, scammers sent emails posing as the CEO of an Austrian aerospace parts maker, requesting large sums of money from entry-level employees. This resulted in approximately $61 million in losses. This type of phishing tactic is so prevalent that it even has a name: CEO fraud.
While social engineering scams are always changing, educating yourself on the latest phishing trends and security software options is the best thing you can do to stay safe. Check out our list of phishing statistics below.
While many of the statistics below provide historical context, phishing tactics and volumes have continued to evolve rapidly through 2024–2026. Recent cybersecurity reports indicate that phishing remains one of the leading initial attack vectors, with increasing use of AI-generated content, deepfake impersonation, and multi-channel delivery methods across email, messaging apps, and collaboration tools.
Key Takeaways:
- One in every 99 emails is a phishing email.
- It’s estimated that 3.4 billion fraudulent emails are sent daily.
- The top five most impersonated brands are eBay, Apple, Microsoft, Facebook, and Steam.
- 2021 was the costliest year for data breaches in 17 years.
- The total average cost of a data breach was $4.24 million in 2021, up from $3.86 million the previous year.
Recent cybersecurity reports further reinforce the scale and persistence of phishing threats:
- Phishing remains responsible for over 30–40% of reported cyber incidents in many enterprise environments.
- More than 90% of successful cyberattacks begin with a phishing email or social engineering attempt.
- The average organization faces thousands of phishing attempts per year, with large enterprises experiencing significantly higher volumes.
- Human error continues to play a role in over 70–80% of security breaches, often linked to phishing interactions.
Table of Contents:
- What percentage of cyberattacks are phishing?
- Recent phishing attempts are more convincing
- Phishing email statistics
- Website phishing statistics
- Top brands exploited by phishing scams
- Cost of phishing attacks
- Data breach statistics
- Phishing trends in 2022
- 4 tips to protect against phishing for businesses
What percentage of cyberattacks are phishing?
Phishing accounts for a significant portion of modern cyberattacks, frequently serving as the initial access point rather than the final stage of a breach. In many cases, attackers use phishing to obtain credentials, deploy malware, or manipulate users into transferring funds. Understanding the percentage of attacks involving phishing helps clarify its role as one of the most effective and widely used cyber threat methods.
Phishing is estimated to be involved in roughly 20% to over 30% of data breaches, depending on the reporting methodology and dataset. In broader security incident analyses, phishing often appears even more frequently as an initial attack vector, highlighting its central role in enabling credential theft, fraud, and system compromise.
Verizon’s 2020 Data Breach Investigations Report found that 22 percent of data breaches are phishing. That accounts for more than one in every five data breaches.
This only makes sense, given that the FBI’s Internet Crime 3 (IC3) Report recorded phishing as the most common cybercrime type of 2020.
The number of phishing, vishing, smishing, and pharming complaints came out to 241,342, resulting in adjusted losses of over $54 million.
According to CISCO’s 2021 Cyber Security Threat Trends, 86 percent of organizations had at least one user attempt to connect to a phishing website.
Additionally, F5’s 2020 Phishing and Fraud Report found that phishing incidents rose by 220 percent compared to the yearly average during the height of the COVID-19 pandemic.
Recent analyses from enterprise security reports indicate that phishing is involved in over one-third of all security incidents, and in many cases serves as the initial access vector rather than the final attack stage. This reinforces its role as one of the most effective entry points for cybercriminals.
What these statistics indicate:
- Phishing is often the starting point for larger cyberattacks rather than the final outcome
- Attackers rely on human interaction, making phishing harder to fully automate defenses against
- Even a single successful phishing attempt can lead to widespread system access or financial loss
- Organizations with weaker user awareness are significantly more vulnerable to phishing-based breaches
Recent phishing attempts are more convincing
Phishing attacks have become more convincing due to the use of personal data, targeted messaging, and increasingly sophisticated social engineering techniques. Modern phishing campaigns often mimic real communications from trusted sources, making them difficult to distinguish from legitimate messages. This shift from generic mass emails to highly tailored attacks significantly increases the likelihood of user interaction and successful compromise.
Modern phishing attempts are more convincing because they use real personal or organizational data, impersonate trusted contacts, and create a sense of urgency or legitimacy. Unlike traditional mass phishing, these attacks are often tailored to specific individuals or roles, making them significantly harder to detect through visual cues alone.
At one point, phishing attacks were known as easy-to-spot emails sent out to mass numbers of people. Today, spear phishing emails use personal information to craft convincing messages targeting specific individuals.
Recent threat intelligence reports show that highly targeted phishing attacks (spear phishing) now account for a growing share of successful breaches, with significantly higher success rates compared to generic mass phishing campaigns.
This is shown by Symantec’s 2019 Internet Security Threat Report, which found that 65 percent of targeted attacks in 2019 involved spear phishing tactics. The motivation of 96 percent of these targeted attempts were for the sake of gathering intelligence.
How modern phishing attacks become more convincing:
- Information gathering: Attackers collect publicly available data from social media, company websites, or previous breaches
- Personalization: Emails or messages are tailored with names, job roles, or recent activity
- Impersonation: Messages appear to come from trusted sources such as coworkers, executives, or service providers
- Timing and context: Attacks are sent during relevant events (e.g., payroll cycles, project deadlines)
- Action trigger: The message prompts urgent action, such as clicking a link or transferring funds
Email phishing is also the number one concern for 90 percent of IT professionals, according to a recent survey by IRONSCALES. The same survey found that 81 percent of IT directors and managers experienced higher rates of email phishing attempts since the start of the COVID-19 pandemic.
For example, an attacker may send an email that appears to come from a company executive requesting an urgent payment, referencing a real project or vendor. Because the message aligns with expected business activity and uses familiar language, employees may be more likely to comply without verifying the request.
Here’s a breakdown of how many respondents from that survey experienced phishing on platforms other than email:
- Video conferencing platforms: 44 percent
- Workforce messaging platforms: 40 percent
- Text messaging: 36 percent
These stats show how phishing attempts are becoming more convincing while spreading across different platforms, where the average worker might not see them coming.
Some studies also indicate that phishing emails generated or enhanced using AI tools can achieve notably higher engagement rates, particularly when combined with real-time contextual information such as recent transactions or internal company activity.
Security Note
Messages that create urgency or request immediate action—especially involving payments or credential access—should always be independently verified through a separate communication channel.
Phishing email statistics
Email remains the primary delivery method for phishing attacks due to its widespread use, low cost, and ability to reach large numbers of users quickly. Attackers exploit email to distribute malicious links, attachments, and impersonation messages that appear legitimate. Understanding phishing email statistics helps illustrate the scale, frequency, and effectiveness of these attacks across both individuals and organizations.
Phishing is most commonly done via email. In 2019, Avanan’s analysis of 55.5 million emails revealed that one in every 99 emails is a phishing attempt.
How many phishing emails are sent daily?

Valimail’s 2019 Email Fraud Landscape report estimated that 1.2 percent of emails are malicious.
If you convert that percentage into emails, it corresponds to 3.4 billion fake emails being sent per day. By those estimations, it means that over the course of a year, over 1 trillion fraudulent emails are sent out.
What these statistics indicate:
- Even a low success rate can result in large-scale impact due to the sheer volume of emails sent
- Phishing campaigns rely heavily on automation and scalability
- Attackers do not need to target everyone—only a small percentage of users need to engage
- Email remains effective because it is a trusted and routine communication channel
More recent estimates suggest that phishing emails continue to represent a small percentage of total email traffic, but disproportionately account for a large share of successful cyber incidents due to their targeted and deceptive nature.
Why email continues to be the primary phishing vector:
- It is universally used across personal and professional environments
- Emails can be easily spoofed or impersonated
- Users are accustomed to clicking links and downloading attachments
- Many organizations rely heavily on email for critical workflows and communication
Common email phishing attacks to look out for
According to KnowBe4’s Q3 2021 Top-Clicked Email Phishing Report, here are the top five most common phishing email subjects in the U.S.:
- Vacation Policy Update
- Password Check Required Immediately
- Important: Dress Code Changes
- Acknowledge Your Appraisal
- Remote Working Satisfaction Survey
In the same study, these were the most common subject lines found in the Middle East, Europe, and Africa:
- Your Document is Complete — Save Copy
- Stefani Has Endorsed You!
- You Requested a Reset to Your LinkedIn Password
- Windows 10 Upgrade Error
- Internet Capacity Warning
Security awareness platforms report that click rates on phishing simulations can range from 5% to over 20%, depending on user training levels and attack sophistication.
According to Symantec’s 2019 Internet Security Threat Report, the most common business email compromise (BEC) email keywords were:
- Urgent
- Request
- Important
- Payment
- Attention
- Outstanding payment
- Info
- Important update
- Attn
- Transaction
This shows that you need to be wary of emails that use time-sensitive keywords or ask for payment in any way, shape, or form. This information is one way to help you spot phishing email scams.
Malicious attachments to avoid
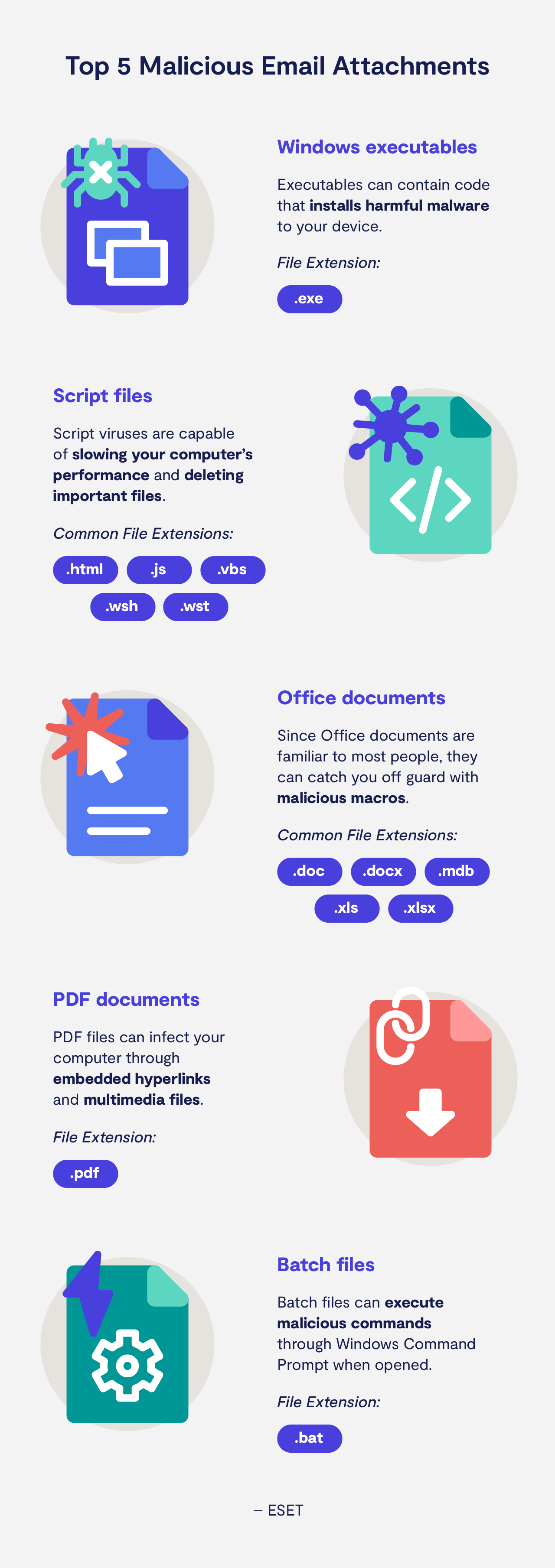
The ESET 2021 Threat Report found that Windows executable files made up 66 percent of malicious email attachments. Other common malicious attachments include script files, office documents, and PDF files. Here’s the full breakdown:
- Windows executables: 66 percent
- Script files: 21 percent
- Office documents - 4 percent
- PDF documents - 4 percent
- Batch files - 3 percent
- Compressed archives - 2 percent
These attachment types are commonly used because they can execute code, deliver malware, or prompt users to enable macros. Attackers often disguise malicious files as legitimate documents to increase the likelihood that recipients will open them.
Being wary of senders when opening attachments is essential. While office workers may be more used to interacting with Office and PDF documents, if you don’t fully trust an email, don’t interact with any links or attachments.
Website phishing statistics
Website phishing involves directing users to fraudulent web pages that mimic legitimate services in order to steal sensitive information such as login credentials or payment details. These sites are often accessed through phishing emails or messages and are designed to appear trustworthy. Understanding how phishing websites operate and how frequently they occur is essential for identifying and avoiding these threats.
Phishing websites are fake or compromised web pages designed to look like legitimate sites in order to trick users into entering sensitive information. Many modern phishing sites use HTTPS encryption and realistic design elements, making them difficult to distinguish from genuine websites without careful inspection.
All too often you’ll find fraudulent emails claiming to come from a trusted source. Whether you receive a message from someone claiming to be a coworker or an email from “Facebook Customer Support” claiming your account has been hacked, website phishing happens all the time.
How phishing websites typically work:
- A user receives a phishing email or message containing a link
- The link directs them to a spoofed or cloned website
- The page mimics a trusted brand (e.g., login portal, payment page)
- The user enters credentials or sensitive data
- The attacker captures and uses this information for unauthorized access or fraud
It was previously thought you could avoid these dangerous sites by checking for HTTPS in URLs instead of HTTP. The former indicates that a web page is encrypted and more secure. This false sense of security, however, is something scammers have recently been taking advantage of.
Webroot found that approximately 32 percent of phishing websites used HTTPS during 2020. That means that one in three phishing websites are going the extra mile to maintain an image of security.
Recent research indicates that over 80% of phishing sites now use HTTPS encryption, highlighting how attackers increasingly rely on legitimate-looking security indicators to build trust with victims.
According to APWG’s Q2 2021 Trends Report, here are the industries mimicked most by phishing attempts:
- Financial industry: 29.2 percent
- Social media: 14.8 percent
- Payment: 12.2 percent
- SaaS/webmail: 8.7 percent
- E-commerce/retail - 8.2 percent
- Cryptocurrency - 7.5 percent
- Logistics/shipping - 6.9 percent
- Other - 10.1 percent
Common signs of a phishing website include:
- Slight variations in the domain name (e.g., misspellings or extra characters)
- Unexpected login requests or redirects
- Poorly formatted pages or inconsistent branding
- Requests for sensitive information outside normal workflows
- URLs that do not match the official domain of the service
Pro Tip
Instead of clicking links in emails, manually type the official website URL into your browser to reduce the risk of being redirected to a phishing site.
Because it’s common for trusted websites to be impersonated, be mindful of the warning signs of suspicious URLs. In fact, avoiding suspicious links is one of the most important internet safety rules.
Top brands exploited by phishing scams
Phishing attacks frequently impersonate well-known brands to exploit user trust and increase the likelihood of interaction. Attackers create emails and websites that closely resemble legitimate services, such as financial institutions, technology companies, and e-commerce platforms. Understanding which brands are most commonly targeted helps users recognize potential threats and remain cautious when interacting with unexpected communications.

F5’s 2020 Phishing and Fraud Report found that 55 percent of phishing websites used target brand names and identities in their URLs. In this way, cybercriminals use brand rapport to capture sensitive information from their victims.
Why attackers target well-known brands:
- High user trust: Familiar brands reduce suspicion
- Large user bases: More potential victims
- Frequent interactions: Users expect regular emails or notifications
- Credential reuse: Compromised accounts can be used across multiple services
- Financial linkage: Many accounts are tied to payment or personal data
According to CISCO’s 2021 Cyber Security Threat Trends, the financial services sector experiences the most phishing attacks out of any other sector. For the healthcare sector, phishing and trojan attacks made up three-quarters of malicious traffic.
In Webroot’s 2021 BrightCloud Threat Report, researchers found which companies were most often impersonated by phishing websites. Here is a breakdown of that data:
- eBay: 13.2 percent
- Apple: 10.2 percent
- Microsoft: 9.5 percent
- Facebook: 8.8 percent
- Google: 8.6 percent
- Steam: 7.9 percent
- Yahoo: 5.4 percent
- Netflix: 3 percent
- PayPal: 3 percent
What this means for users:
- Receiving an email from a well-known brand does not guarantee legitimacy
- Even accurate logos and branding can be replicated by attackers
- Phishing attempts often mimic routine communications such as account alerts, password resets, or billing notifications
Sometimes phishing websites can look almost identical to the brand they’re impersonating. This is why it’s so important to use antivirus software that warns you about suspicious or potentially unsafe websites.
Cost of phishing attacks
Phishing attacks can result in significant financial and operational losses for organizations, ranging from direct monetary theft to long-term reputational damage. These costs often extend beyond the initial incident and include recovery efforts, legal consequences, and business disruption. Understanding the full cost of phishing attacks helps organizations evaluate risk and prioritize cybersecurity investments more effectively.
The cost of phishing attacks can range from thousands to millions of dollars per incident, depending on the scale and impact. Business email compromise (BEC) and data breaches caused by phishing are among the most expensive outcomes, often involving financial fraud, operational disruption, and extended recovery timelines.

According to APWG, in 2021 the average wire transfer requested in BEC attacks increased from $75,000 in 2020 to $106,000 in 2021.
The total cost of phishing attacks typically includes:
- Direct financial loss: Fraudulent transfers, stolen funds, or ransom payments
- Incident response costs: Investigation, containment, and remediation efforts
- Operational disruption: Downtime, productivity loss, and service interruptions
- Reputational damage: Loss of customer trust and potential revenue decline
- Legal and compliance costs: Regulatory fines and legal proceedings
Recent estimates suggest that phishing-related incidents cost organizations millions of dollars per breach on average, with business email compromise (BEC) attacks alone accounting for billions in global annual losses.
The same report found that in the second quarter of 2021, 24 percent of BEC attacks attempted to divert employee payroll deposits.
This information is supported by IBM’s Cost of a Data Breach Report 2021, where it was found that 2021 was the costliest year for data breaches in the last 17 years. They reported that from 2020 to 2021, the average total cost of a data breach increased from $3.86 million to $4.24 million.
Researchers from the same report found that, on average, data breaches caused by phishing took 213 days to be identified and 80 days to be contained. This means that the average time it takes to contain a phishing threat overall is 290 days.
In addition, the total global cost of cybercrime—including phishing as a primary driver—is projected to reach trillions of dollars annually, underscoring the scale of financial risk associated with these attacks.
Data breach statistics
Data breaches often occur as a result of successful phishing attacks, where attackers gain access to sensitive systems or credentials through deception. A data breach involves unauthorized access to confidential information, including personal data, financial records, or internal business systems. Understanding data breach statistics helps illustrate the real-world impact of phishing and the scale of potential damage.
Data from IC3’s 2020 report found BECs to be the most costly cybercrime, resulting in over $1.8 billion in yearly losses.
How phishing leads to data breaches:
- A user is tricked into revealing login credentials or downloading malicious content
- Attackers gain access to internal systems or accounts
- Unauthorized activity begins, such as data access or privilege escalation
- Sensitive information is extracted or systems are compromised
- The breach may go undetected for extended periods
In 85 percent of data breaches, a human element was involved, according to Verizon’s 2021 DBIR. This makes sense, given how often phishing tactics use social engineering to steal sensitive information.
In the same report, it was found that credentials are the most commonly stolen type of data in 61 percent of breaches. Here are the rankings of the most commonly stolen data types:
- Credentials
- Personal
- Medical
- Bank
- Internal
- Payment
- Other
According to Proofpoint’s 2021 State of the Phish report, they found that the most common impacts of successful phishing attacks included:
- Loss of data: 60 percent
- Credential/account compromises: 52 percent
- Ransomware infections: 47 percent
- Other malware infections: 29 percent
- Financial loss/wire transfer fraud: 18 percent
Phishing trends
Recent threat reports indicate that phishing attacks have continued to grow in volume and sophistication, with some organizations reporting year-over-year increases in phishing attempts exceeding 50%.
As we move into a more remote working environment and people spend more time on their devices, it brings more opportunities for phishing attacks to occur. Here’s a breakdown of the most notable 2022 phishing trends:
- Phishing attacks increased 510 percent from January to February in 2020. (Webroot’s 2021 BrightCloud Threat Report)
- Phishing URLs impersonating Netflix increased by 646 percent from March to July of 2020. (Webroot’s 2021 BrightCloud Threat Report)
- More than 60 percent of security professionals surveyed said that phishing campaigns were the most increased security problem during the COVID-19 pandemic. (Microsoft’s 2021 New Future of Work Report)
- Tech support fraud increased by 171 percent from 2019 to 2021, resulting in over $146 million in losses. (FBI’s Internet Crime 3 (IC3) Report)
These stats all point to the fact that, as our world becomes more remote, we have to be more proactive about cybersecurity. Keep your data secure with a VPN and try being more mindful about which emails you click on.
4 tips to protect against phishing for businesses
Protecting against phishing requires a layered security approach that combines employee awareness, technical safeguards, and ongoing monitoring. Because phishing attacks target human behavior as well as system vulnerabilities, businesses must implement multiple defensive measures to reduce risk. Effective protection involves not only preventing attacks but also detecting and responding to incidents quickly.
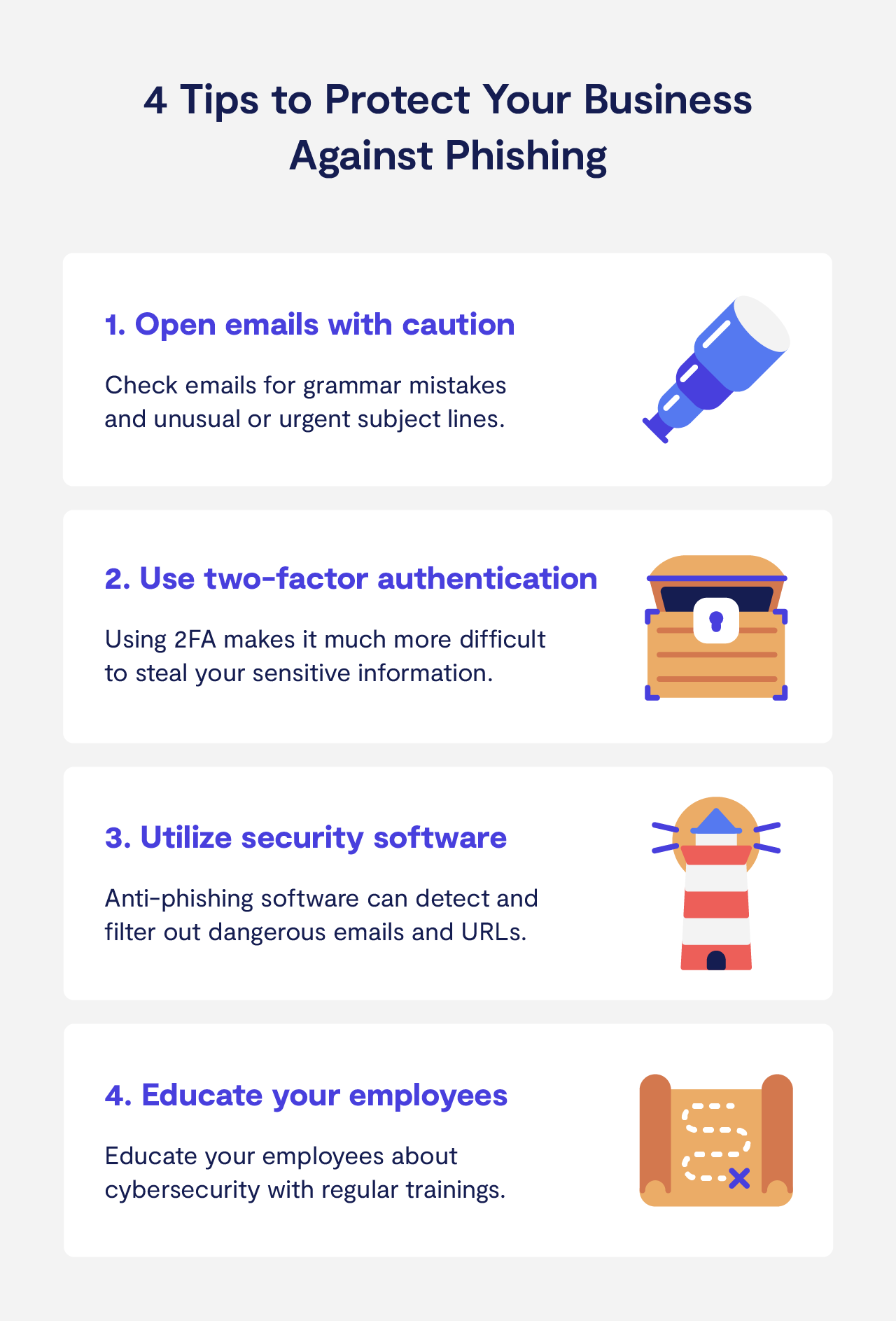
Businesses are frequently the targets of phishing campaigns. In severe cases, cyberattacks engaging in CEO fraud can cost companies millions of dollars.
The more proactive you are about security, however, the less likely you are to experience great losses from phishing scams. Here are some ways to defend yourself.
1. Open emails with caution
Since emails are the most common form of phishing scams, be mindful as you peruse your inbox. You don’t want a malicious attachment installing spyware onto your device. Warning signs of a fraudulent email include:
- Grammar mistakes
- Unusual requests
- Urgent subject lines
A common tactic scammers use in phishing emails is to pretend to be a coworker or a higher-up at the company you work for. That said, be on the lookout for emails from your “CEO” that request personal information.
2. Use two-factor authentication
Using two-factor authentication, or 2FA, simply means that you use two or more channels to verify your identity when accessing a platform. This means that to access your work email, you might be required to enter in a security code that’s sent to your phone as well as your usual password.
If your password is stolen by a cybercriminal, they still won’t have access to your company’s sensitive data with 2FA.
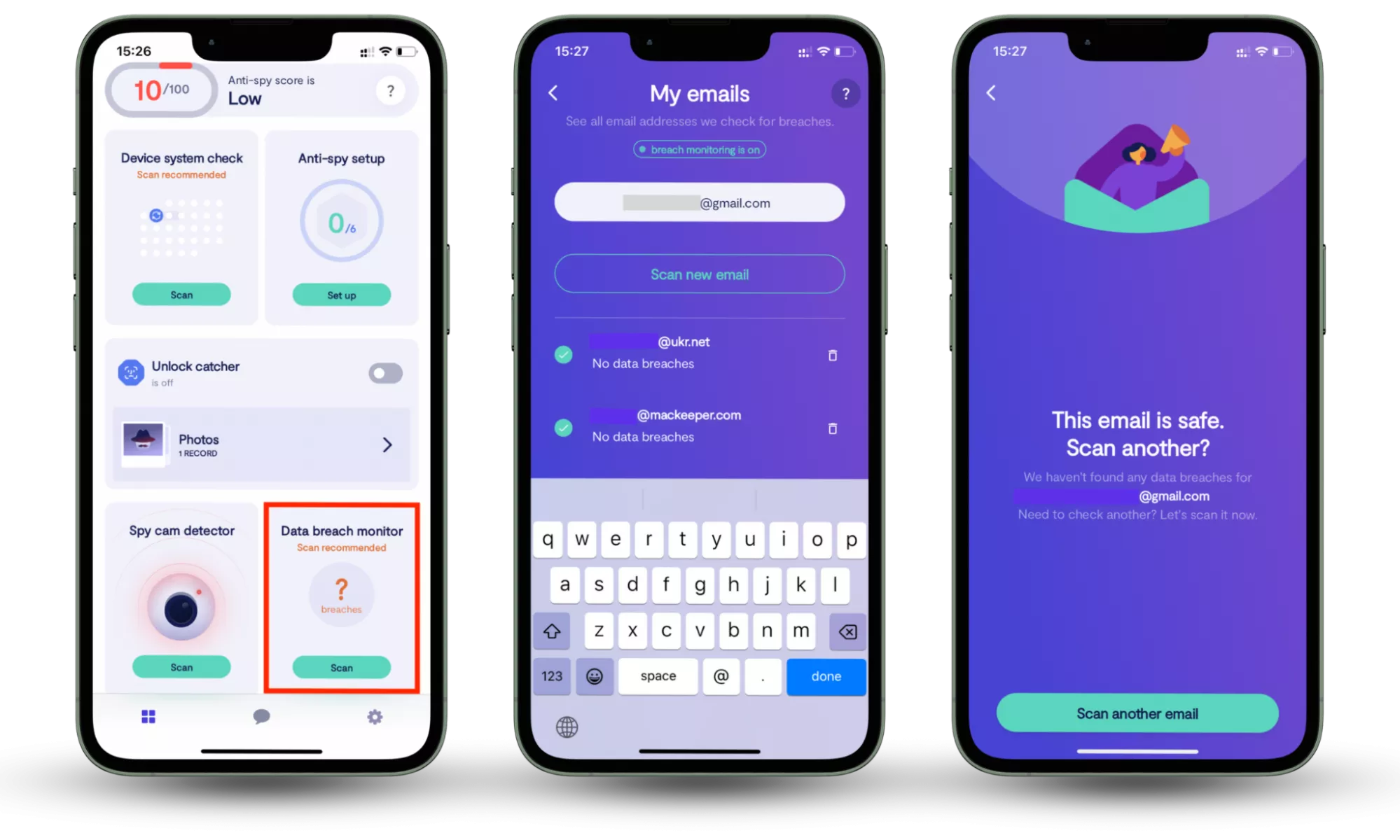
Even with strong passwords and multi-factor authentication, compromised credentials can still circulate in data breaches without immediate visibility.
A data breach monitoring tool helps identify whether your email accounts or login credentials have been exposed, allowing you to take action before attackers can use them.
With Clario’s Data Breach Monitor, you can:
- Scan your email addresses to detect known data breaches
- See which accounts may be exposed or compromised
- Receive alerts if your data appears in newly discovered leaks
- Continuously monitor your accounts with automatic 24/7 tracking
This type of monitoring adds an additional layer of protection by helping you respond quickly to potential threats before they escalate.
Here is how to use Clario Anti Spy's Data breach monitor:
- Download Clario Anti Spy.
- Open the app, and, under Data breach monitor, tap Scan.
- Enter your email address.
- When the scan is complete, follow the on-screen guidance to review any data breaches.
- Repeat the process for any other email addresses.
3. Phishing cybersecurity software
The last thing you want is for ransomware to infect your work computers. To keep your business protected, make sure your computers are always running the latest software updates and using anti-tracking software.
When it comes to keeping your business safe specifically from phishing emails, there are a number of security solutions out there. When choosing security software, simply make sure that it features ways to filter and remove spam, email filtering rules, and malicious URL detection.
4. Educate your employees
The more educated your employees are about security and potential phishing tactics, the more secure your business will be overall. Whether you keep your employees informed through a newsletter or weekly training, you should help them understand common phishing threats and how to avoid them.
You may even want to go the route of requiring your employees to complete full cybersecurity training courses. Some free options include the Department of Health and Human Services Training and FedVTE.
While phishing attacks are on the rise, there are plenty of ways to defend yourself. Be wary of common phishing signs, such as urgent emails and suspicious links and attachments.
You’ll also want to download Clario’s antivirus software and VPNs to defend against phishing attempts. Our data breach monitor allows you to scan emails for threats while alerting you to any leaked sensitive information we detect. Download our mobile security software for Mac, iOS, or Android to keep your data safe.
The landscape of cybersecurity is ever-changing, so you have to be proactive about keeping yourself and your business informed.
Get our research in simple facts gathered in one comprehensive infographic.
Conclusion
Phishing remains one of the most effective cyberattack methods, often serving as the entry point for credential theft, financial fraud, and data breaches. As these attacks become more sophisticated and harder to detect, relying on awareness alone is no longer enough—protection requires both preventive measures and ongoing vigilance.
One practical way to reduce your risk is to monitor whether your data has already been exposed. Clario Anti Spy’s Data breach monitor helps you identify compromised accounts, receive alerts about leaked information, and take action before attackers can use your credentials.


