Table of contents
- What is an Apple ID phishing scam?
- Why do scammers target your Apple ID?
- Types of Apple ID phishing scams
- Apple ID receipt email
- Disabled Apple account notification
- Apple ID fake text messages
- Apple ID phone call scams
- App store pop-up asking for your password
- Fake calendar invitation
- iPhone locked
- How to identify an Apple ID scam?
- Top tips on how to identify and prevent an Apple ID scam
- How to protect yourself from an Apple ID phishing scam
- What to do if you clicked an Apple ID phishing link
- How to report Apple ID phishing scams
- Identify and prevent Apple ID phishing scams to safeguard your data
What is an Apple ID phishing scam?
An Apple ID phishing scam is a type of cyberattack where attackers impersonate Apple Inc. to trick users into revealing their Apple ID credentials through fake emails, messages, or websites. These scams are designed to capture login details and gain unauthorized access to services like iCloud, App Store purchases, and personal data stored across Apple devices.
Hackers pose as Apple to lure you into thinking there’s a legitimate reason for them asking for such information. Messages from these imposters will usually contain a website URL that leads you to a forged website, where any entered details are sent to the hacker. Apple ID phishers specifically target your Apple ID and password in order to access Apple services such as the App Store, iMessage, iCloud, and Apple Music.
How Apple ID phishing typically works:
- You receive a message that appears to be from Apple (email, SMS, or pop-up).
- The message creates urgency (e.g., “account locked” or “unauthorized purchase”).
- You are prompted to click a link leading to a spoofed Apple login page.
- You enter your Apple ID and password.
- The attacker captures your credentials and accesses your account.
Important to know
Some phishing websites use HTTPS and display a padlock icon, which can falsely signal legitimacy. A secure connection does not guarantee that a website is genuinely operated by Apple, so always verify the full domain name before entering credentials.
Why do scammers target your Apple ID?
Scammers target your Apple ID because it acts as a centralized account that controls access to your personal data, financial information, and connected devices within the Apple Inc. ecosystem. Gaining access allows attackers to exploit purchases, extract sensitive files, impersonate you, or lock you out of your own devices for financial gain.
If a scammer is able to steal your Apple ID credentials, then you are handing over access to your contact information, addresses, banking information — all information that is probably best kept private. When you unknowingly give a stranger access to your iCloud, you are allowing them to probe deep into your files, documents and photo history. Scammers will rely on finding private information or media which can be used to extort money from you.
Example scenario
If an attacker gains access to your iCloud account, they may review your stored photos or documents to find sensitive or private content. This information can then be used to pressure you into paying money in exchange for not exposing it, a tactic commonly used in extortion-based scams.
What attackers can access with your Apple ID:
- Financial activity: Make unauthorized App Store purchases or subscriptions linked to your account.
- Personal data: View contacts, email content, photos, and stored documents in iCloud.
- Device control: Use features like “Find My iPhone” to lock your device or track its location.
- Identity misuse: Send messages or emails pretending to be you to scam others.
Why Apple IDs are high-value targets
Your Apple ID is linked across multiple services, including iCloud storage, device backups, messaging, and payment methods. This interconnected access increases the potential impact of a single compromised account compared to standalone credentials.
Types of Apple ID phishing scams
Apple ID phishing scams appear across multiple communication channels, including email, text messages, phone calls, and device notifications. Each type uses different tactics to impersonate Apple Inc. and trick users into revealing login credentials. Understanding how each method works makes it easier to recognize suspicious behavior and avoid account compromise.
Scammers are constantly innovating and inventing new ways to steal your information. As one scam is exposed, and people become wise to it, another will take its place. This constant development makes it harder for the public to stay protected.
Why these scams keep evolving
As users become more aware of common phishing tactics, attackers adapt by changing formats, language, and delivery methods. This constant evolution means that recognizing patterns—rather than specific examples—is essential for staying protected.
Common categories of Apple ID phishing scams:
- Email phishing: Fraudulent emails that mimic Apple notifications or receipts.
- SMS phishing (smishing): Text messages designed to create urgency and prompt quick action.
- Voice phishing (vishing): Phone calls where scammers impersonate Apple support.
- Interface spoofing: Fake pop-ups or system prompts requesting your password.
- Calendar and notification abuse: Unsolicited invites or alerts containing malicious links.
Apple ID receipt email
An Apple ID receipt email involves you receiving an email from an Apple imposter claiming that a purchase has been made by your Apple ID. Attachments can be sent with the Apple ID scam email to increase the believability of the trick, and to entice you into signing into your Apple ID through their falsified link. Once you enter your details, they will be saved and sent to the scammer.
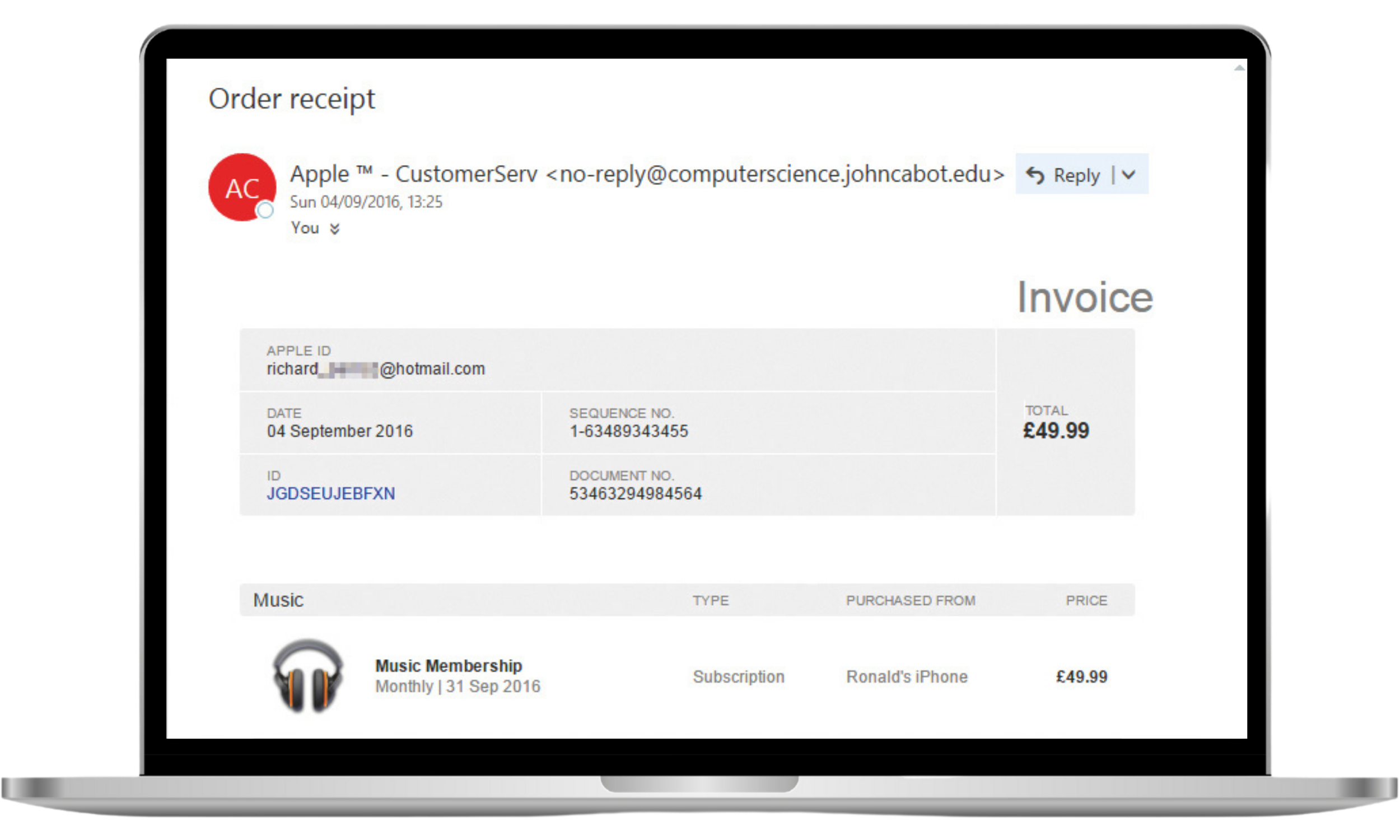
Common red flags:
- Unexpected purchase you don’t recognize
- Links that do not lead to an official apple.com domain
- Attachments prompting you to “view receipt”
- Urgent language pushing immediate action
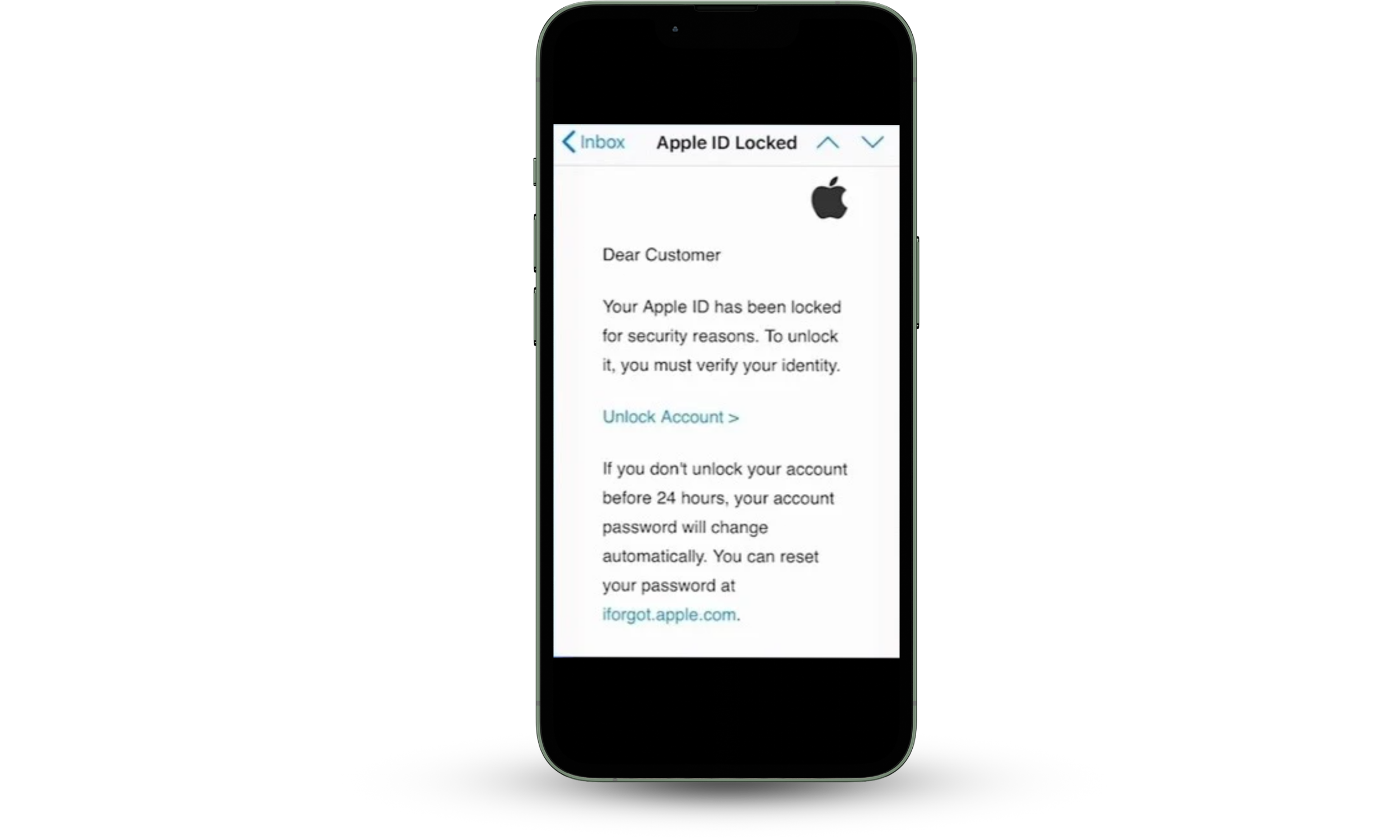
Disabled Apple account notification
One of the more common phishing scams, involving your Apple ID, is a strategy in which a scammer sends an Apple phishing email to your account, telling you your Account has been locked. A decoy website link will be attached to this email in hopes that you click the link and try logging into your account, thus sending your password to the scammer.
Apple does not ask users to unlock accounts through email links. Legitimate account issues are handled through official device prompts or by logging in directly via Apple’s website. Always navigate manually instead of clicking links.
Apple ID fake text messages
Scammers utilize many different forms of phishing techniques, hoping to catch you off guard. Fake text messages can be sent to your phone, often with an alarming statement such as ‘Your Apple account is now locked’. This technique is used to instill panic in the account holder and blur their rational thinking. These messages will often direct you to a link of a fake website asking you to input your account details, or to the scammers phone number where they will try to extract your account details from you over the phone.
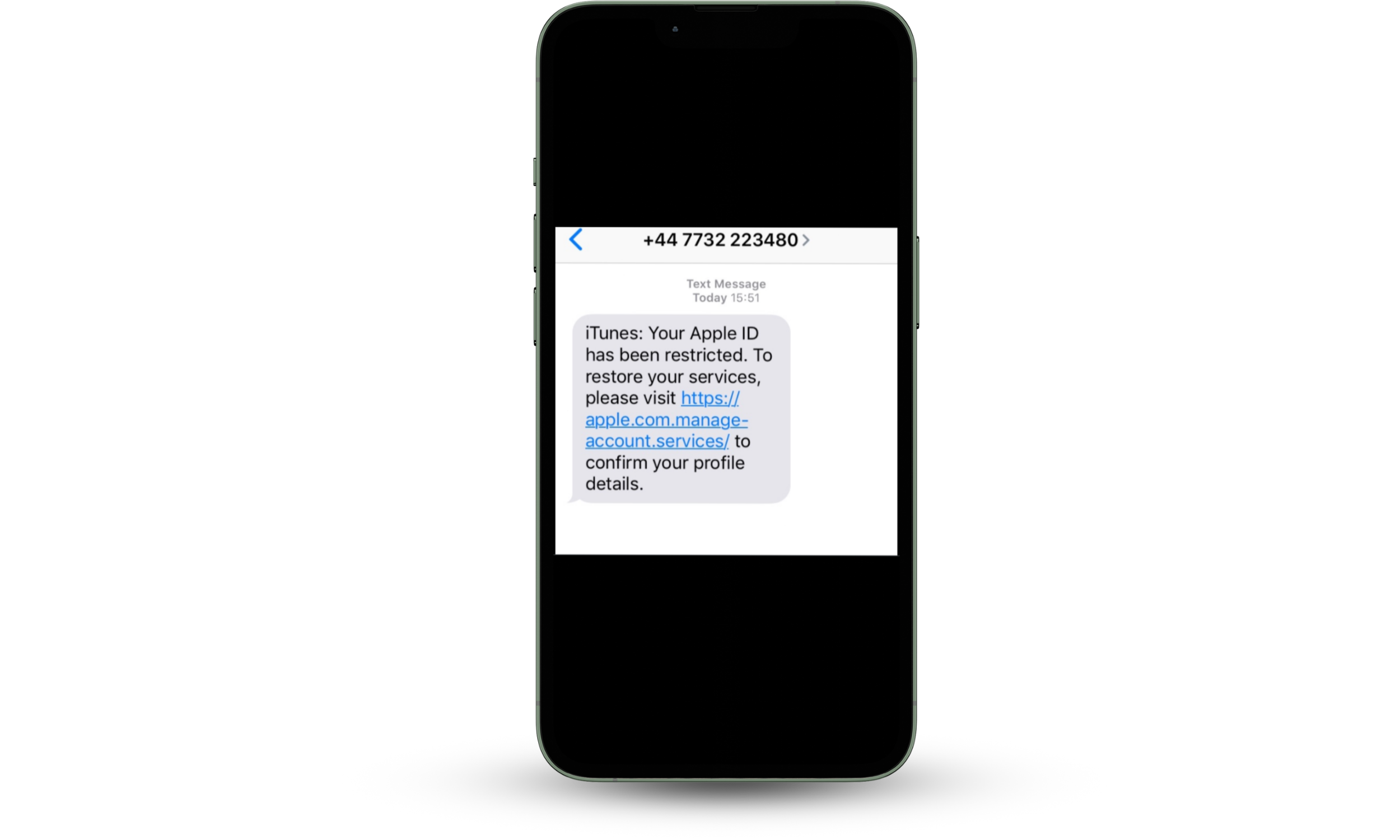
Note
Avoid tapping links directly from text messages. Instead, open your browser and manually type the official Apple website address to verify any claims.
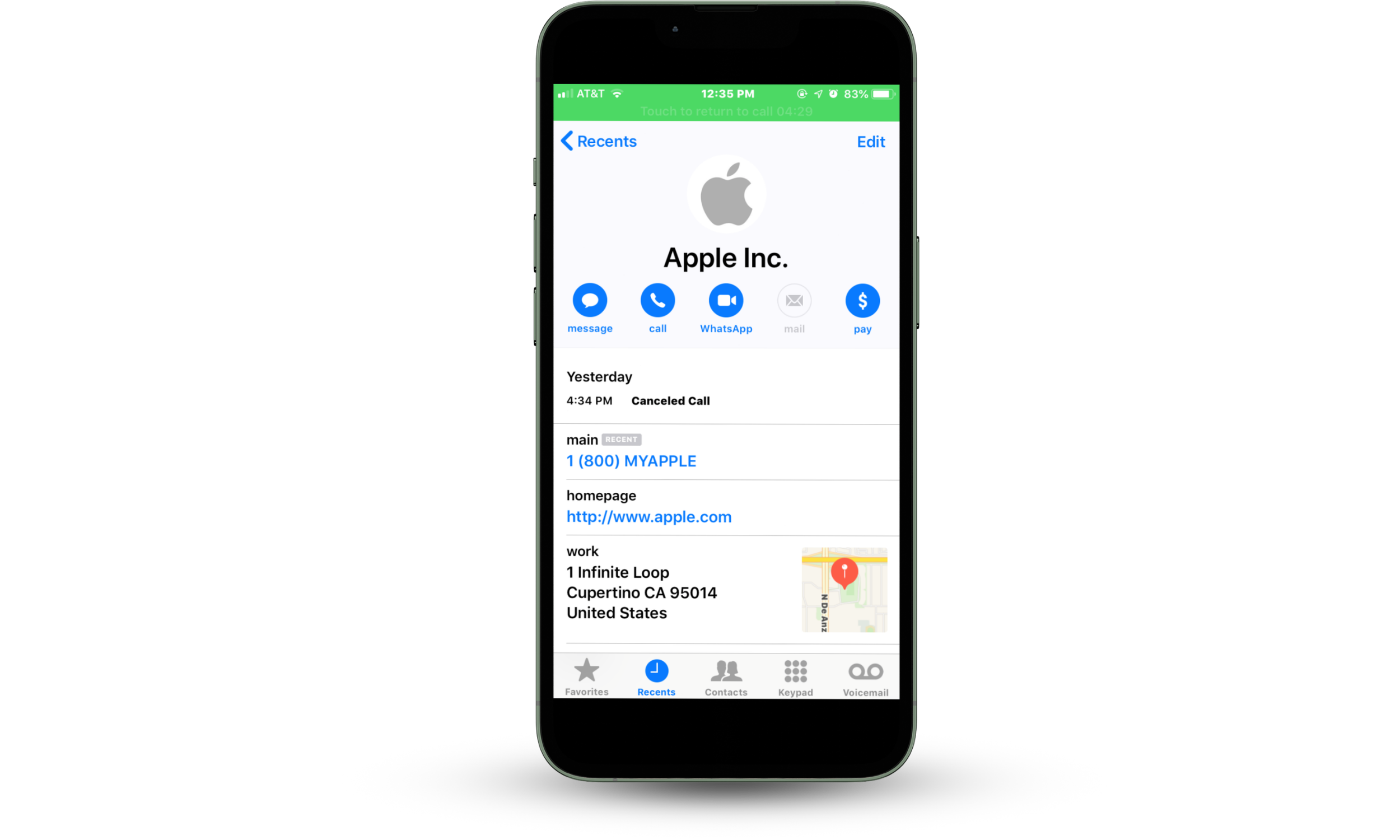
Apple ID phone call scams
Scammers are able to disguise their Caller ID with the official Apple name and logo. This makes the illusion that much more real. The effectiveness of this scam really depends on how convincing and confident they are on the phone, making it harder to spot the scam. The best approach to identifying these scams is to disconnect the call, and dial the official Apple support number back to ask if they had just phoned you.
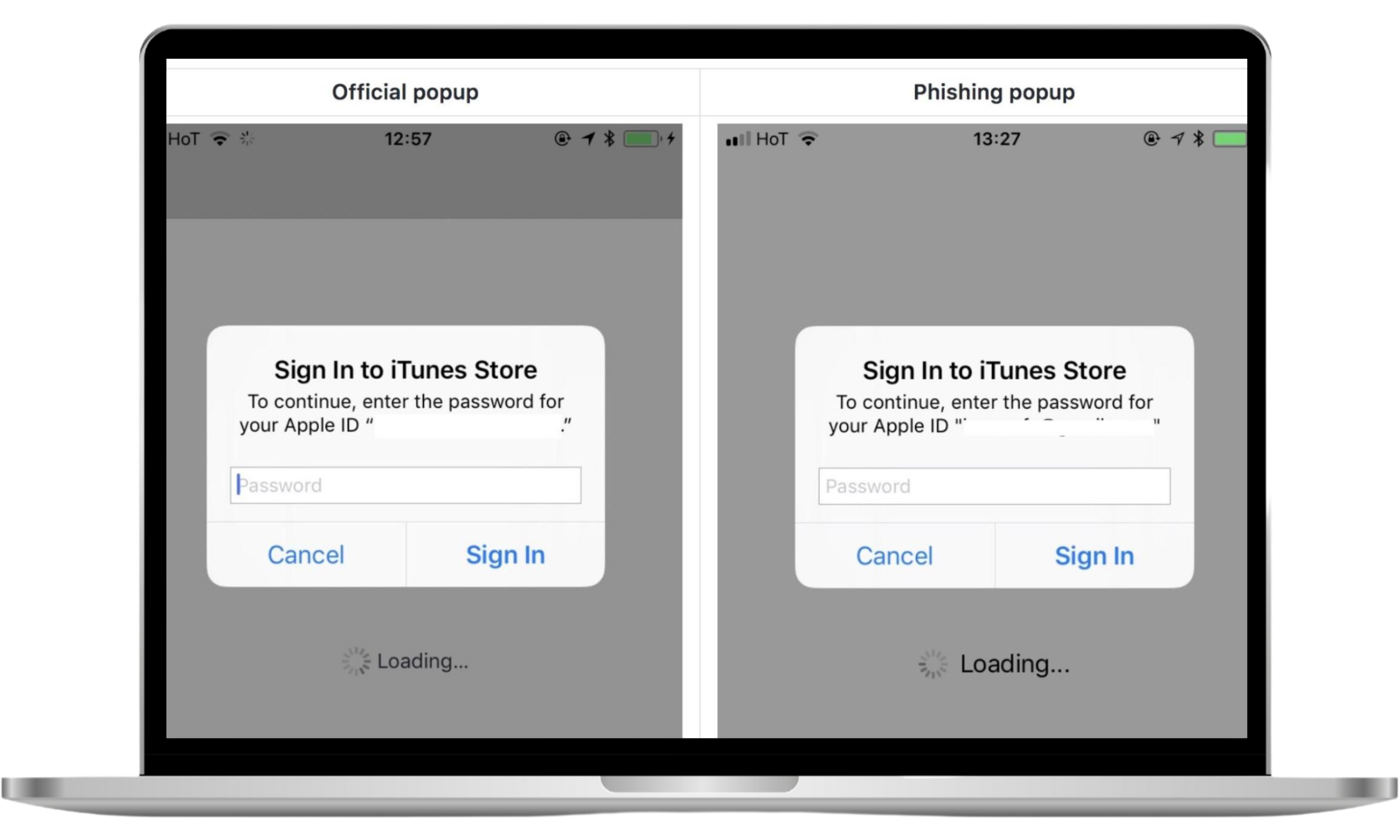
App store pop-up asking for your password
App store pop-ups show up so regularly when interacting with your phone, that it becomes natural to just enter in your password whenever prompted to do so. This can be dangerous should a scammer find a way to send a pop-up directly to you.
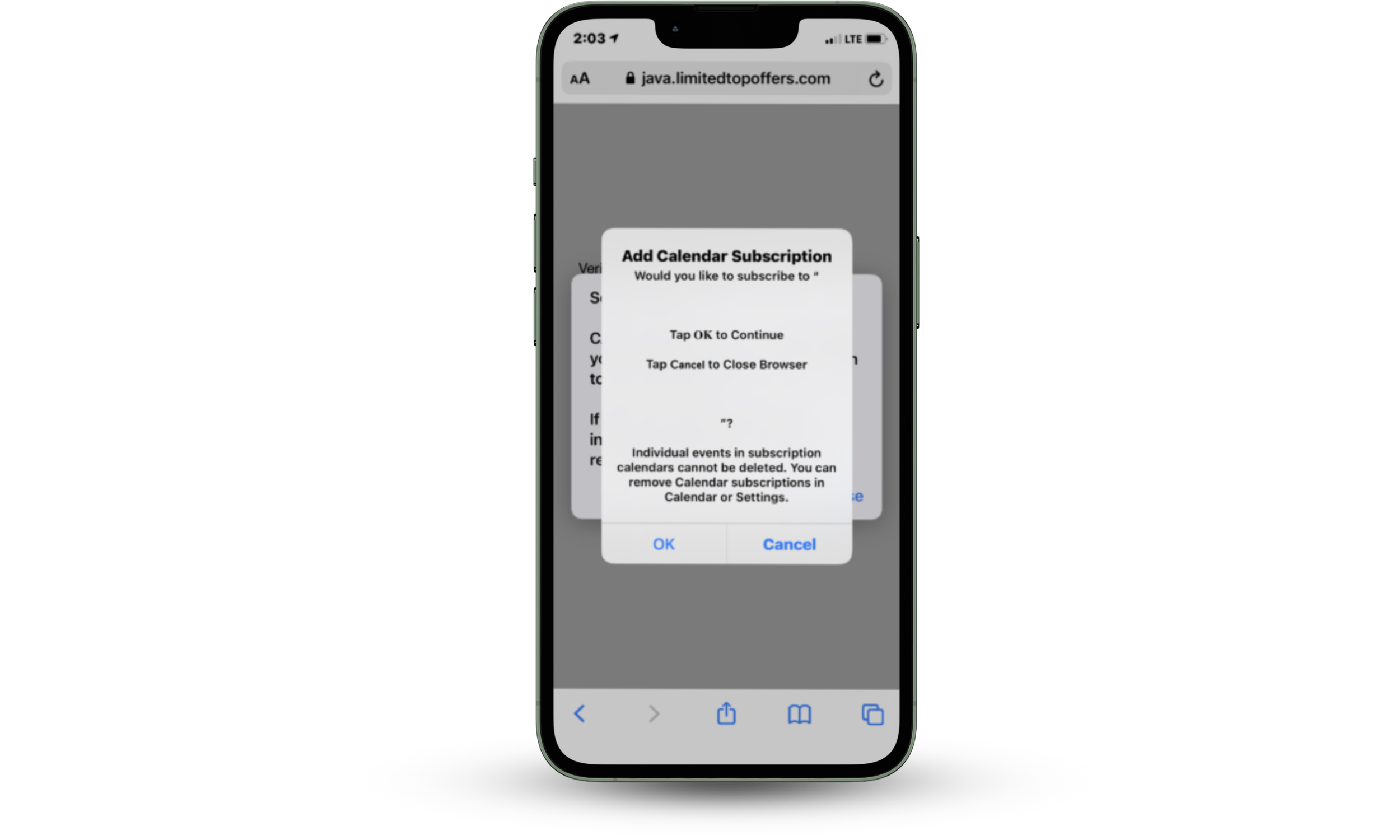
Fake calendar invitation
If an invite is sent through to your Calendar or Mail that you aren’t expecting, it’s best to take a moment and analyze the invitation. Delete fake calendar invites so scammers don’t gain access to your private information.
iPhone locked
Finding yourself in this situation is never usually good news. Perhaps you have already fallen victim to one of the scams above, and now the scammer has got your Apple ID credentials. So what happens next? The scammer will usually look to register your phone as lost, activate the “Find My iPhone” settings, and threaten to keep you locked out of your phone unless you pay them to relinquish back control of your device.
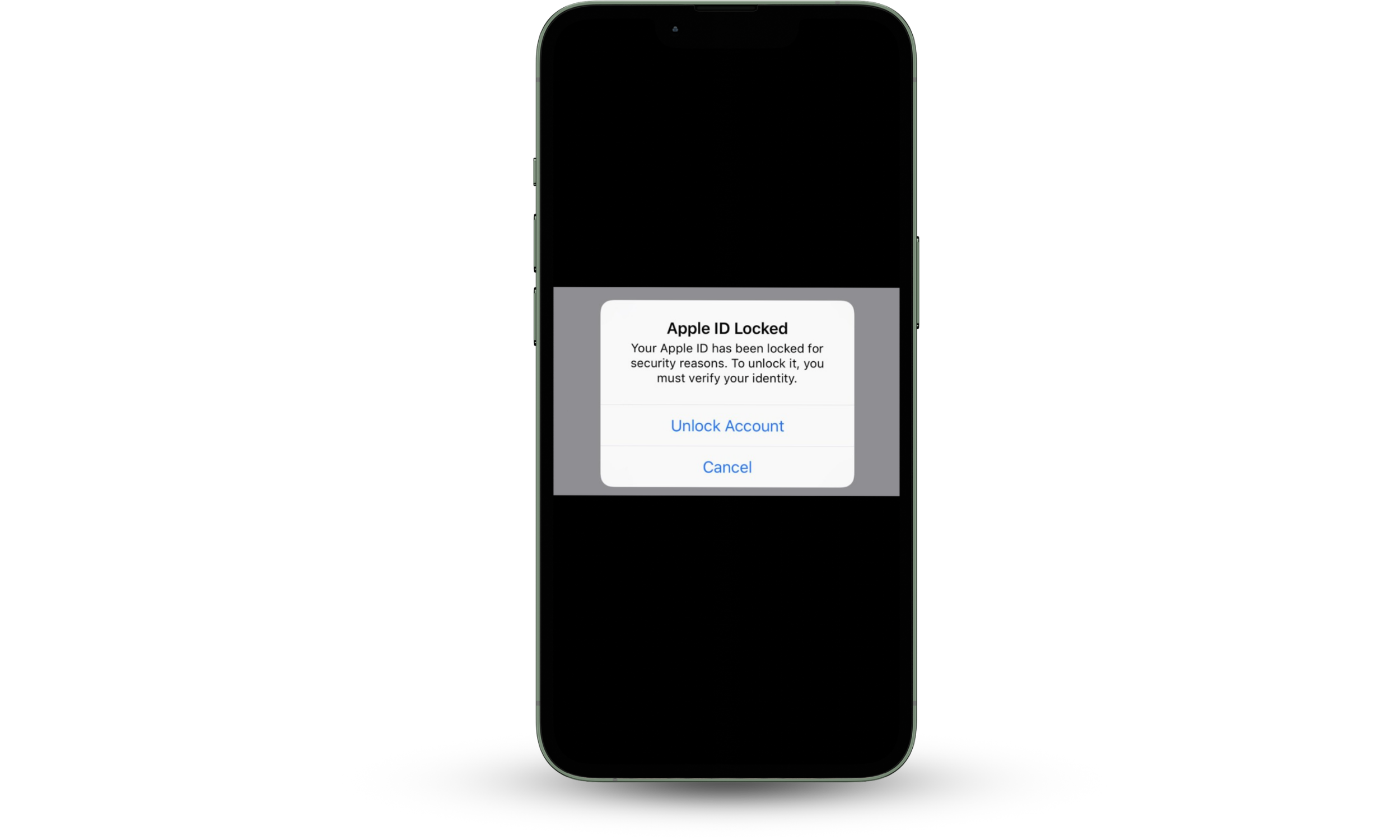
Your mobile iPhone is often the hub of your life. Countless hours are spent scrolling through your phone, but what you may not realize is just how much information you have saved on your iPhone. This makes it a very lucrative target for scammers to try and gain access to your device for their own monetary gain. Keep on reading to find out more about Apple ID scams and how you can prevent them.
How to identify an Apple ID scam?
Apple ID scams can be identified by analyzing the sender, message quality, links, and the type of request being made. Phishing attempts typically rely on urgency, impersonation of Apple Inc., and deceptive links to trick users into revealing credentials. Carefully inspecting these elements helps you recognize and avoid fraudulent communications.
Spotting an Apple ID scam without prior awareness of what to look for can be tricky. Follow this list of helpful hints and know what to look out for next time:
- Unusual email senders. The team at Apple would come up with a more professional sounding email then appleid@apple.id.com. If it doesn’t look legit…it probably is an Apple ID spam email.
- Typos. “Hello friend,we come wit bad news”, either Apple have dropped their copywriters standards immensely, or you have caught yourself a scammer. Keep a close eye out for spelling mistakes, grammatical errors, or incorrect spacing to identify potential scam messages.
- URL shorteners. Unless you receive links that send you directly to apple.com or other official website addresses, you shouldn’t trust the link. Official Apple emails will never contain link shorteners like Bitly.
- Urgency. Slow down, what’s the rush? If you notice unnatural urgency in a message then take a moment to think, why is the sender trying to make you respond so quickly? Chances are they don’t want you to stop and notice other tells in this list.
- Attachments. Attachments are often the gateway for scammers to gain access. Don’t download anything or click external attachments without verifying it first.
- Verify requests. Apple employees will never ask you for your personal details. If you are being asked private questions about your social security number or credit cards, don’t engage in the conversation.
- Generic greetings. Apple will have your name on record and will address you by it when contacting you. If a message refers to you as Sir/Madam/Friend, there’s a high possibility that message is a scam.
Important to know
Some phishing attacks closely mimic legitimate Apple communications, including branding and formatting. If you are unsure, avoid interacting with the message and instead access your account directly through Apple’s official website or device settings.
Top tips on how to identify and prevent an Apple ID scam
The best way to prevent yourself from falling victim to an online scam is by staying alert. Preventing Apple ID phishing scams requires a combination of secure account settings, safe browsing habits, and awareness of common attack tactics. If a matter concerns highly targeted private information or credentials, then take extra care. There is no harm in contacting Apple yourself if you encounter a message that you cannot clearly identify as a threat. Afterall, it is better to be safe than sorry. Use these key principles to stay ahead of the scam:
- Account security practices:
- Don’t use the same password across multiple sites
- Update passwords routinely
- Enable two-factor authentication (2FA) for your Apple ID
- Use a password manager to generate and store strong, unique passwords
- Safe browsing & interaction habits:
- Always check the URL
- Never share your Apple ID password with anyone
- Avoid clicking links in unsolicited emails or messages
- Manually navigate to official Apple websites when verifying account activity
- Device & software protection:
- Install antivirus software on your device
- Keep web browsers up to date
- Make sure you have the latest version of your operating system
- Regularly review devices connected to your Apple ID and remove unfamiliar ones
Pro Tip
If you receive a suspicious message about your Apple account, do not interact with it directly. Instead, open your device settings or type the official Apple website address into your browser to verify the information safely.
The best way to prevent yourself becoming a victim of one of the scams above is to have an expert in your corner to protect you.
How to protect yourself from an Apple ID phishing scam
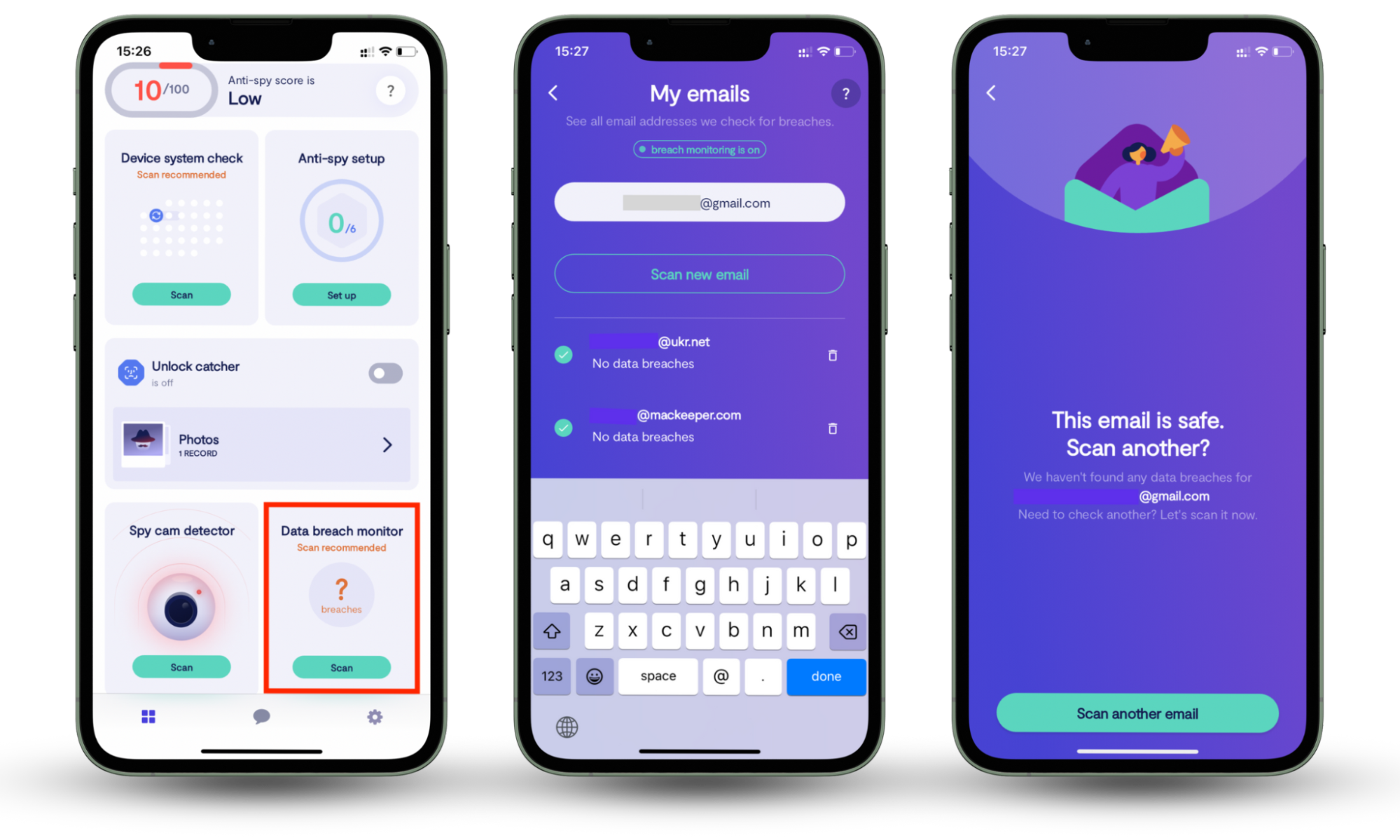
If you suspect you have become a victim of an Apple ID phishing scam, use Clario Anti Spy’s Data breach monitor. It will tell you if your email address, which holds the key to troves of sensitive information in your emails and online accounts, has been leaked online. This gives you the edge over a scammer to change your passwords and resecure your accounts — before it’s too late.
Here’s how to use it:
- Download Clario Anti Spy and get a subscription.
- After setting up an account, navigate to the Data breach monitor option and tap the Scan button.
- On the new window that appears, select Check for breaches at the bottom of the screen. Clario Anti Spy will start looking for breaches your email address was included in and let you know what it discovers. If your email address was leaked in a data dump, follow Clario Anti Spy’s prompts to secure it. However, if your email wasn’t leaked, you’re good to go.
- You can now check more email addresses by choosing the Scan another email option on the screen and repeating the process. Alternatively, rest assured that Clario Anti Spy will constantly monitor the email address you’ve already checked for future leaks.
What to do if you clicked an Apple ID phishing link
If you clicked an Apple ID phishing link or entered your credentials on a suspicious website, you should act immediately to secure your account and prevent unauthorized access. Quick response steps—such as changing your password, reviewing account activity, and contacting Apple Inc.—can significantly reduce potential damage.
Steps to secure your Apple ID after a phishing incident:
- Change your Apple ID password immediately using official Apple settings
- Enable or reset two-factor authentication (2FA)
- Sign out of all active sessions on your Apple ID
- Review your account for unknown devices and remove them
- Check recent purchases and subscriptions for unauthorized activity
- Update passwords on other accounts that share similar credentials
How to report Apple ID phishing scams
Reporting Apple ID phishing scams helps protect both your account and other users by enabling faster detection and removal of fraudulent activity. If you receive a suspicious message claiming to be from Apple Inc., reporting it through official channels allows security teams to investigate and take action against attackers.
Ways to report Apple phishing attempts:
- Forward suspicious emails to Apple’s phishing reporting address (as listed on Apple’s official website)
- Use built-in Report Spam feature in messaging apps
- Contact Apple Support directly to report phishing attempts involving your account
Include the following details when reporting:
- The full message or email (do not edit or modify it)
- Sender information and timestamps
- Screenshots of suspicious messages or websites (if safe to capture)
Identify and prevent Apple ID phishing scams to safeguard your data
Unfortunately, Apple ID phishing scams are here to stay. As long as that’s the case, your best bet is to educate yourself about them, including prevention measures and risks, to avoid falling victim. Using the tips in this article, you can stay alert and keep your emails and other sensitive information secure. Clario Anti Spy’s suite of privacy tools, including its proactive Data breach monitor, empower you to safeguard your data.


