Table of contents
- Why the term “spam”?
- Types of spam
- Spam emails
- Phishing emails
- Malware spam (malspam)
- Tech support scams
- Social media spam
- Current event scams
- Advance-fee scams
- Spam texts and spam calls
- SEO spam
- How to identify spam
- What is the difference between spamming and phishing?
- Why am I getting spammed?
- How to prevent spam
- Conclusion
Why the term “spam”?
Spam or computer spam is any unsolicited communication sent to recipients, usually in bulk. It can take on many forms, but it usually includes texts, emails, and calls.
This unwanted digital communication was coined “spam” because of a Monty Python skit. In the skit, patrons in a restaurant continuously insisted that everyone eat “Spam” with a capital S. Spam is a brand of cooked cork packaged in cans that became widely used after World War II.
It's the insistence of the diners which was, in effect, quite spammy — similar to how internet spam works nowadays.
Types of spam
As you’ve probably experienced, there are different types of spam, especially in computer terms. In fact, some spam strategies are so subtle that you probably don’t realize what you're dealing with. Have a look at the different kinds of spam below.
Spam emails
Spam emails are so common you probably receive them every other day. Email spoofing is one of the more popular spam email categories.
Spoofed emails are fake emails made to look legit, as though they come from a reputable business like a bank or other financial institution. The goal is to get you to take action in some way, like clicking on a link.
Of course, taking any sort of action is risky because you could compromise your personal information. Most browsers have filters for spam emails, but that doesn’t mean it blocks them. You can still find them in the spam folder. If you’re tired of deleting spam emails, learn how to block them in Gmail, Yahoo! and Outlook. And keep spammers out of your secure inbox.
Phishing emails
Similar to spam emails, phishing emails are standard spam emails sent in bulk. Phishing is similar to fishermen lowering a wide-cast net in the ocean with the aim of catching unsuspecting fish, hence the term “phishing.” Essentially, it’s baiting individuals into giving up their personal information, like their:
- Credit card information
- Online login credentials
- Bank account details
- Social security number (SSN)
- Full name
- Home address
- Date of birth.
You’ll know you’re looking at a phishing scam if the email asks for any of the information listed above or has a tone of urgency. In some cases, it will contain spelling errors, grammatical errors, and incorrect punctuation.
Look out for non-official email addresses, like a Gmail or Yahoo! email address. Official businesses obviously don’t use those. Finally, although some phishing emails have the business name in the sender’s email address, one or two letters might be off.
Malware spam (malspam)
Otherwise known as malware spam, malspam refers to any form of online spam that infects your device with malware or spam viruses. Malspam typically comes in the form of an email, text message, or social media text. It delivers spam if you do any of the following:
- Click on a malicious link
- Open or download a malicious attachment.
Hackers can infect your device with a host of spam malware, including:
- Ransomware
- Spyware
- Trojans
- Bots
- Cryptominers
- Keyloggers, and more using malspam.
Think about all the sensitive information you store on your phone and computer. Imagine what could happen if a cybercriminal got a hold of that information. They could impersonate you, demand a ransom, post or sell your data on the dark web, and even scam innocent individuals.
Needless to say, malware can do much damage to your device and your life at large, as it compromises your personal information. That’s why you can’t take any chances. In this day and age, protecting your personal information should be as important as protecting your safety.
Thanks to the many cybersecurity solutions available, there are plenty of ways to reduce spam risks. One important step is making sure spam messages are not being used to sneak spyware onto your phone. Some scams use links or attachments to install tracking apps that can monitor what you do, even beyond your messages.
Clario Anti Spy helps detect and remove spyware from spam links or malicious downloads. If you accidentally tap on something suspicious, a quick scan can help you find and remove hidden threats before they cause harm.
Why not give it a try and check your device for hidden threats?
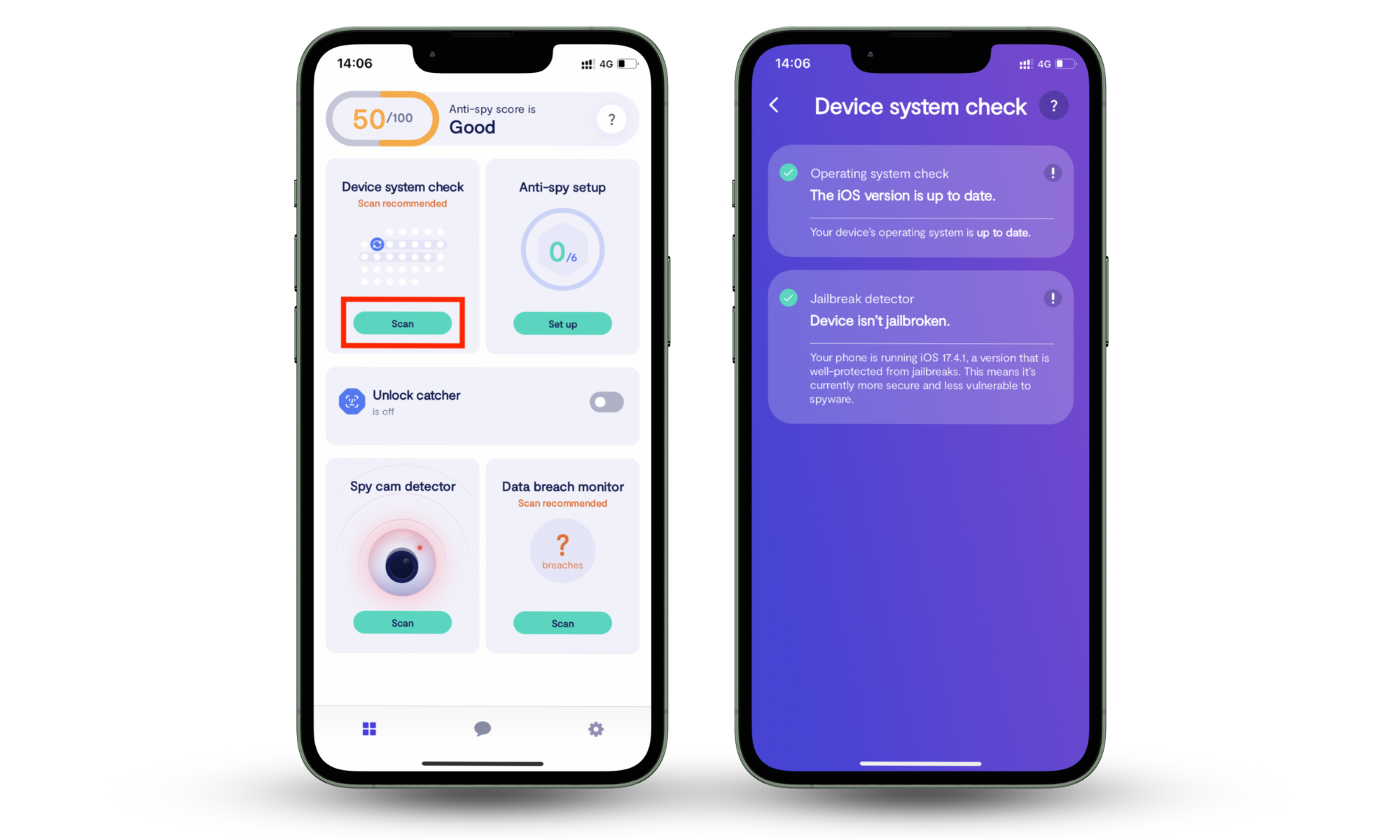
Follow these steps to scan your phone with Clario Anti Spy:
On Android (Spyware scan):
- Download Clario Anti Spy and create an account.
- Open Clario Anti Spy on your phone.
- Tap Spyware scan in the main menu.
- Run a Scan to detect tracking apps or suspicious permissions.
- Follow the steps to remove any detected threats.

On iPhone (Device system check):
- Download Clario Anti Spy and create an account.
- Open Clario Anti Spy on your phone.
- Tap Device system check in the main menu.
- Run a Scan to check for jailbreaks or security vulnerabilities.
- Follow the recommendations to secure your device.
Tech support scams
Tech support scams are often performed by hackers who pose as tech support agents from a technology or cybersecurity company. They inform you that something is wrong with your device and offer help.
These scammers are known to name-drop a large company you’ll recognize, so you can trust them and click on the link provided or call the phone number in the message.
If you think something might be wrong with your mobile phone or computer, find the phone number on the official website and contact the company's support team instead. For example, contact Apple Support or take your iPhone, iPad, or Mac in to have it examined.
Social media spam
Spammers and hackers take advantage of any opportunity and use any platform necessary to lure their victims. To that end, social media is one of the platforms on which spammers carry out their activities.
Here’s how spammers contact you on social media:
- They comment on your posts to attract attention to their own fake profiles or bot accounts, which usually contain links to their websites.
- They send you Direct Messages (DMs) with links. Small jewelry and clothing brands are known to create spam accounts that DM content creators for collaborations, even if you don’t follow them or have never engaged with their content.
If you take the conversation far enough, you’ll find that you must fork out your own money to get the product shipped to you. To avoid getting scammed, never click on suspicious links on sketchy profiles or engage with DMs from strangers.
Current event scams
On social media, trend jacking refers to using trending topics for views and engagement. Event scams work similarly. They hop on the bandwagon of current events to trick you into performing an action.
For example, the COVID-19 pandemic opened the door to COVID-19 scams that took advantage of vulnerable people who were concerned about their health. Examples of these scams include scammers posing as health officials and offering masks, vaccines, and more in phishing text messages and emails. The aim was to steal their victims’ credentials when they clicked on the malicious links.
Beware of engaging with texts, calls, and emails that ask you to provide your personal information, send money toward a cause, or click on links.
Advance-fee scams
These types of scams are aimed at obtaining cash from you. Scammers try to convince you to send them a financial advance, which will yield financial gain in the future. The scenarios vary.
Below are some examples of advance-fee scams:
- The scammer is in the middle of a large business deal, but their money is stuck in an offshore account or tied up in the business deal. So, they need you to loan them money in the meantime, which they’ll return, perhaps with interest, when their money is freed up.
- Someone has sent the scammer money via a digital platform, like Western Union. However, the money won’t arrive in time, but they need funds urgently. They’ll pay you back as soon as the money reflects in their bank account.
- They want to purchase something for you, but they require you to send them the money, and they’ll reimburse you at a later stage.
Scammers can be very convincing, and some have been doing this for so long, it can be hard to catch them in their lies. The Tinder Swindler is one of many scammers out there who rip innocent people off.
In some cases, scammers can provide “proof” that they have the money they claim to have. Falling victim to advance-fee scams can leave you broke, depressed, and sometimes homeless. You should never, under any circumstances, loan or give someone money unless it's to a family member you trust or a friend you’ve known for years.
Spam texts and spam calls
Sometimes, spammers take their efforts a step further by calling you on your mobile phone. These annoying, unwelcome automated calls (or robocalls) are known as spam calls.
- Spam calls are usually placed by telemarketers and sometimes political parties who get your number from an online database. However, sometimes, you willingly give them your contact details at an event you attend, like a conference, and forget about it.
- Spam texts, also known as SMiShing, are a form of phishing, and they urge recipients to click on unknown links. You can receive spam texts via SMS, WhatsApp, and social media. Never engage with such texts and calls. In fact, block the caller and sender immediately to prevent them from contacting you again.
SEO spam
While spam is often spread via text, email, social media, and sometimes calls, it also extends as far as search engines.
Search engine optimization (SEO) is a popular skill whereby a specialist strategically places specific, well-researched keywords around a particular topic throughout a blog article. The goal is to make a website’s blog post around that topic rank higher on Google.
SEO spam, therefore, refers to the process of manipulating SEO tactics to make an organization’s website or web page around a specific topic rank higher on Google.
There are two types of SEO spam:
- Content spam. Spammers intentionally include specific keywords in their web content to make that content and their web pages rank higher on search engines.
- Link spam. Instead of keywords, spammers cram a ton of unrelated links in a blog post to increase the chances of readers clicking on them.
How to identify spam
We’ve all received spam communication at some point, whether we were aware it was spam or not. Maybe you’ve even fallen victim to it because you didn’t recognize what you were dealing with. Fortunately, there are ways to identify spam so you can protect yourself.
Look out for the following signs to determine whether you’re dealing with spam:
- Attachments: Treat any emails with attachments from unknown senders as suspicious, especially if the body of the email contains little information.
- Links: suspicious links are often a telltale sign that an email or text message from an unknown sender is spam.
- Dodgy email address: If an email address looks like a variation of a company name or has a series of numbers and letters in it, it’s probably spam. Email addresses from spammers pretending to be company representatives are also often unofficial email addresses, like a Gmail or Yahoo! email address. In some cases, these email addresses contain the sender’s name.
- Unidentified sender: Spammers typically email you from their personal email accounts, hardly from an official business email. If you don’t recognize the sender, block them and delete the email.
- Poorly written text or email: Spammers almost always send poorly written texts and emails. If you receive a text or email with grammatical errors, spelling errors, and that is poorly punctuated, chances are it’s spam.
- Inflated offers: Treat text messages and emails that promise you anything that sounds too good to be true as suspicious. Examples include spam SMSes that urge you to claim prizes like large sums of cash, a house, or a car, especially if you didn’t enter any competition.
- Missing information: Spam attacks rarely take the time to find out enough about you. If you receive an email with limited information from someone who claims to know you, they’re probably trying their luck. Generic emails that lack identifiers beyond your name are probably spam.
- Adult content: Adult content ads are usually spam. While your curiosity might make you consider clicking on the links, it’s not worth it.
- Inheritance claims: Some scammers still use the age-old trick of sending you a misleading email announcing the death of a relative who left you a large inheritance. But you must respond to the email by calling or emailing the sender to claim your inheritance. If this were true, you’d be contacted by a lawyer via a business email address or phone call, or they’d visit you in person.
What is the difference between spamming and phishing?
Spamming and fishing are both nuisances, but they aren’t exactly the same. The difference is their motivations. Spamming is often undertaken by parties who want to sell you something.
Phishing has malicious intentions, like hacking your device or stealing your personal information. Unlike spamming, phishing is frequently done by hackers and cybercriminals.
For example, if a telemarketer tries to sell you insurance on the phone, that’s a spam call. But if someone claiming to be from your insurance company asks you to confirm your personal details via email, that’s phishing.
Learn more
Why am I getting spammed?
A lot of money and resources go into sales and marketing efforts. At best, recipients will open the email or read the text message. Sometimes, the business will receive an inquiry about the text or email. All that effort typically yields minimal results.
Simply put, spamming attacks are a more cost-effective way to reach out to people because messages are sent in bulk and calls are automated. Given that hundreds and thousands of these messages are sent at a time, the companies sending them can expect even a handful of recipients to respond.
How to prevent spam
It’s impossible to completely prevent spam, but you can reduce it. Here’s how:
- Block and report spam senders and callers
- Avoid providing your contact details to organizations, in online forms, and at events
- Use Clario Anti Spy’s data breach monitor to check whether your email address was involved in a data leak
- Use strong passwords for all your online accounts
- Avoid using your main email address for online accounts
- Notify people you know when they’ve sent you spam.
Conclusion
Spam is everywhere, and while you can’t stop it entirely, you can take steps to reduce it and protect yourself from its risks. Blocking spam senders, being mindful of where you share your contact details, and using strong passwords all help keep unwanted messages at bay.
Some spam is just annoying, but other messages contain malicious links that can lead to spyware or data theft. If you accidentally click on something suspicious, Clario Anti Spy helps you check your phone for hidden spyware and security risks, so you can remove threats before they cause harm.


