Table of contents
- Eye-Opening Cybersecurity Facts
- 1. You’ve got mail
- 2. The cost of cyber-attacks
- 3. New identity, who dis?
- 4. Privacy policy: trick or treat?
- 5. Wanted: Highly-skilled hackers
- 6. Password: misterfluffles
- 7. The first cybercrime
- 8. One in five
- 9. Newsflash: You’ve been hacked
- 10. Ye olde hack of 1903
- 11. Beware of Rabbits
- 12. A male-dominated sector
- 13. The most wanted cybercriminal of all time
- Conclusion
If you think cybersecurity is boring, you probably aren’t that familiar with it.
There is no denying it, cybersecurity is a complex subject with lots of techy terminology and restrictions and rules, but there are also plenty of amusing insights that will surprise you.
Have you ever wondered how many cyber-attacks happen daily or what the most popular password is?
Eye-Opening Cybersecurity Facts
Cybersecurity facts help show how common digital threats are, how attackers typically operate, and which security mistakes put people most at risk. From email-based malware and weak passwords to identity theft and data breaches, these insights give useful context for understanding why cybersecurity habits matter in everyday life.
Why these cybersecurity facts matter:
- They reveal how often cyber threats happen.
- They show which attack methods are most common.
- They highlight everyday security mistakes people make.
- They help readers understand where stronger digital habits are needed.
Read on to discover our list of eye-opening internet security facts.
1. You’ve got mail
A recent Verizon data breach investigations report states that 94% of malware is delivered via email. Terrifying to think about, isn’t it? Well yes and no. Just remember to be cautious of unknown senders and never open strange-looking emails. Be sure to set up email security to protect your inbox too.
Security note
Email remains one of the most effective malware delivery channels because attackers can use phishing messages, fake attachments, and malicious links to trick people into opening infected files or visiting compromised websites.
2. The cost of cyber-attacks
Can you believe that every 60 seconds $1,138,888 million is lost to cybercrime? Apart from financial losses, 1,861 people become victims of cyber-attacks every minute, and according to Maryland University, hackers attack every 39 seconds. Small businesses aren’t safe either; it’s estimated that they face 65,000 attempted cyber-attacks everyday.
Important to know
The cost of cyber-attacks usually includes more than stolen money. It can also involve business downtime, data recovery, legal expenses, reputational damage, and the cost of restoring affected systems.
3. New identity, who dis?
Move aside Sandra Bullock, 28% of Americans said they faced identity theft problems in the previous 12 months, according to a survey conducted by Pewresearch. The most common problem was fraudulent charges appearing on their credit or debit cards.
Identity theft often starts with exposed personal information. Common sources include data breaches, phishing scams, stolen financial details, and online accounts protected by weak or reused passwords.
4. Privacy policy: trick or treat?
Do you always read the privacy policy before accepting it? No... we didn’t think so. Don’t beat yourself up about it though, a Pewresearch survey shows that only 9% of Americans read privacy policies before accepting them. Maybe you will change your ways when you realise that these policies may contain information on selling or giving third parties access to your personal data.
Implementation note
When checking a privacy policy, pay close attention to whether the company shares data with third parties, how long it keeps your information, and whether your activity may be used for advertising, profiling, or tracking purposes.
5. Wanted: Highly-skilled hackers
You might be thinking that hackers are hired by shady crooks or rebellious hacktivist groups that want to take down the system. But in reality, the banking industry and other large enterprises are first in line when it comes to attracting top hacking talent. Afterall, the best way to keep their networks safe is by having really good hackers test them thoroughly.
This type of work is commonly known as ethical hacking or penetration testing. Security professionals use these methods to identify vulnerabilities before malicious attackers can exploit them.
6. Password: misterfluffles
Statistic shows that 83% of Americans are using weak passwords. The most popular options include a pet’s name, their own name, or the name of a family member. They’re followed by birthday dates, words related to hobbies, and even part of people’s home addresses. If your passwords fall within these categories, change them immediately. Or you could call your dog B1gLeBoWoW$k1%539.
Pro tip
A strong password should be long, unique, and hard to guess. It is best to avoid names, birthdays, addresses, and other personal details, and to use a password manager to create and store complex passwords securely.
7. The first cybercrime
The internet was invented in the 1960s, but the first cybercrime is believed to have taken place long before that. In 1834, the Blanc brothers infiltrated the French Telegraph System by bribing a telegraph operator and stole financial market information. The scam was uncovered two years later, but the Blanc brothers couldn’t be convicted since there was no appropriate law at that time.
This case shows that information theft did not begin with modern computers. Long before the internet, communication systems were already vulnerable to manipulation, interception, and abuse for financial gain.
8. One in five
Cybersecurity statistics show that nearly one in five people have had their financial information leaked in a data breach. The cyber attacks caused damage such as the leaking of credit and debit card information (circa 26%) and, in some cases, bank account or routing number (6%).
A data breach happens when sensitive information is exposed, accessed without authorization, or stolen from a company or service. Depending on the breach, the leaked data may include payment details, account credentials, contact information, or other personal records.
9. Newsflash: You’ve been hacked
As many as 43% of victims discovered their data was stolen from media reports... Ouch! And they say that breaking up over a text is harsh. Only 42% got information about data breaches directly from the company that was breached. To make matters worse, the average time to detect a data breach is 197 days, meaning that companies could be in the dark about information leaks.
Breaches often take a long time to detect because attackers may stay hidden inside systems, move slowly to avoid suspicion, or exploit organizations that lack continuous monitoring and incident detection processes.
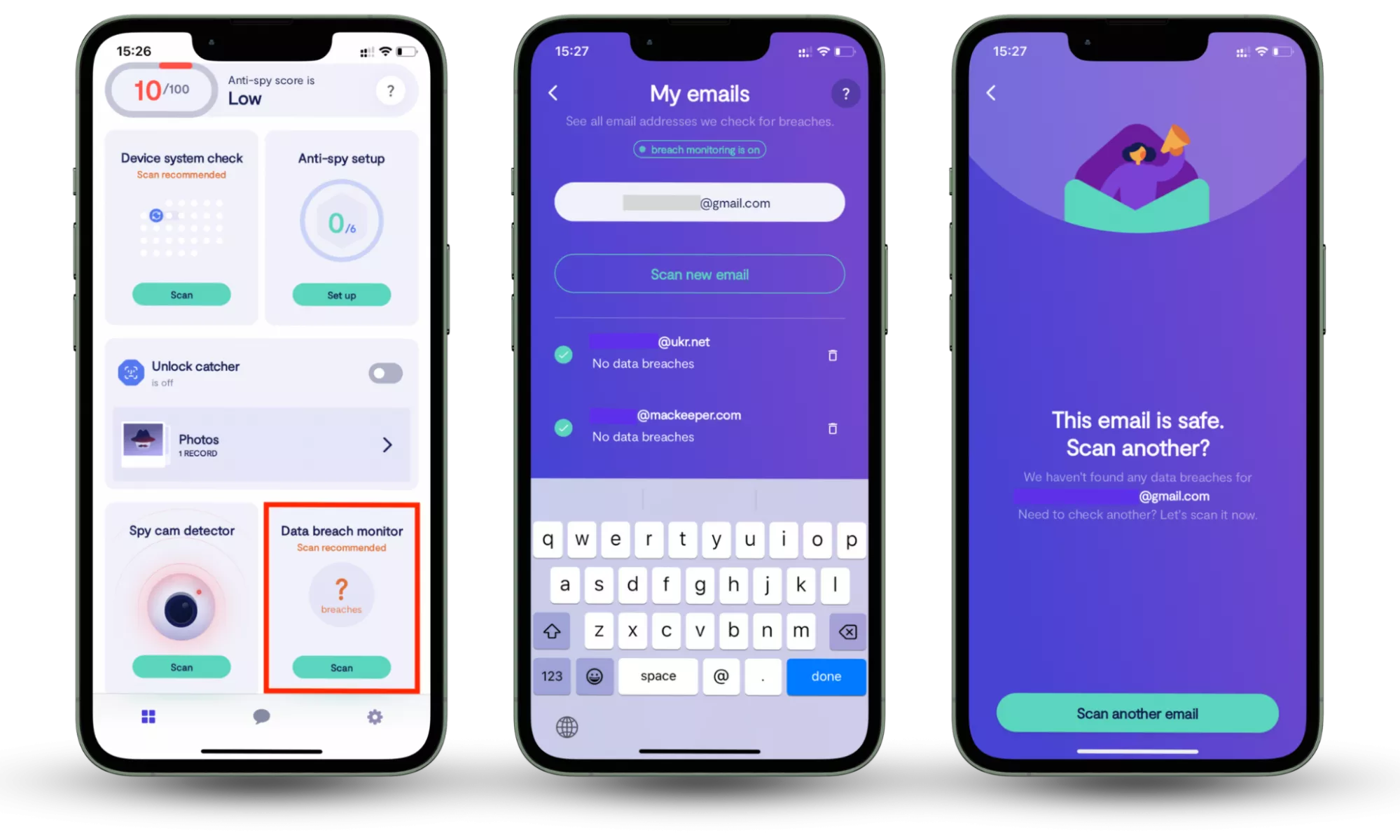
Since companies may take months to detect breaches, it’s important to monitor your own accounts for leaked data. Tools like Clario Anti Spy’s Data Breach Monitor help you check whether your email addresses appear in known data breaches and alert you if your information becomes exposed online.
Available for iOS and Android, the feature scans your email addresses against known breach databases and shows which services may have leaked your data. After reviewing the results, you can secure affected accounts by changing passwords or enabling stronger protections.
How to check whether your information is compromised:
- Download Clario Anti Spy and subscribe.
- Open the app, and, under Data breach monitor, tap Scan.
- Enter your email address.
- When the scan is complete, follow the on-screen guidance to review any data breaches.
- Repeat the process for any other email addresses.
10. Ye olde hack of 1903
In June 1903, just before a public demonstration of Guglielmo Marconi’s invention - a secure wireless telegraph, the machine suddenly began tapping out ‘Rats’. It was later revealed that magician and rival inventor Nevil Maskelyne was behind the “hack”. This was the first time a person hacked something to highlight security flaws.
This incident is often treated as an early example of exposing security weaknesses in public. It demonstrated that even technology promoted as secure could still be disrupted, intercepted, or challenged under real-world conditions.
11. Beware of Rabbits
It all started at the University of Washington Computer Center in 1974. Someone installed a tiny, inconspicuous program that continually made copies of itself until the computer overloaded and stopped working. Known as Rabbit or Wabbit, it is thought to be one of the first computer viruses created. You’ve probably already guessed why it was called that. Unfortunately, the name of its engineer is unknown.
A Rabbit virus is a self-replicating program that repeatedly copies itself until it consumes system resources and disrupts normal performance. Even simple malicious code can cause serious damage when it spreads uncontrollably.
12. A male-dominated sector
The security sector as a whole is currently male-dominated, and cybersecurity is no exception. As of 2017, only 11% of women in the world worked in the information security sector. The proportion of women is almost ten times smaller due to a 23% pay gap, discrimination, and lack of advancement. But the women that do work in this particular industry are beyond inspiring.
Important to know
Workforce diversity remains an important issue in cybersecurity, especially as the industry continues to face skills shortages and growing demand for qualified professionals across security, privacy, and risk management roles.
13. The most wanted cybercriminal of all time
Kevin Mitnick owns two security companies and is a trusted white hat hacker for Fortune 500 companies and governments worldwide. But can you believe that less than three decades ago he used to be the FBI’s most wanted cybercriminal? Kevin hacked into 40 major corporations, including Nokia and Motorola, purely for a challenge and served five years in prison for the crime.
A white-hat hacker is a security professional who legally tests systems, networks, or applications to uncover vulnerabilities and help organizations strengthen their defenses before criminals can exploit those weaknesses.
Important to know
Cybersecurity statistics can change over time as new reports are published and attack trends evolve. That is why it is important to treat security facts as ongoing indicators of risk rather than fixed numbers that never change.
Conclusion
You see, cybersecurity is as interesting as it’s important. And if you’d like to learn more about this topic after reading our surprising facts, Clario’s blog is an excellent starting point.
But learning about threats is only the first step. It’s also important to know if your personal data has already been exposed. With Clario Anti Spy’s Data Breach Monitor, you can scan your email for compromised accounts and receive alerts if your information appears in a known data breach, helping you secure affected accounts before attackers can misuse them.
Read more: